Product
Announcing Precomputed Reachability Analysis in Socket
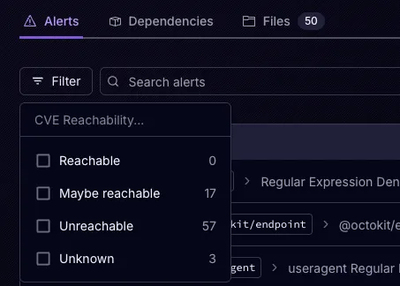
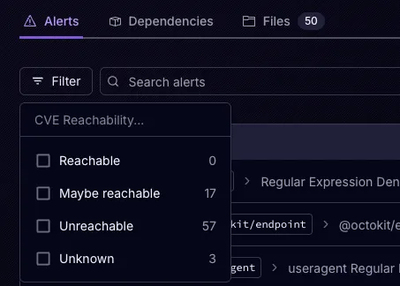
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.
sigs.k8s.io/security-profiles-operator
The Security Profiles Operator (SPO) is an out-of-tree Kubernetes enhancement which aims to make it easier to create and use SELinux, seccomp and AppArmor security profiles in Kubernetes clusters.
This is the parity of features across various security profiles supported by the SPO:
| Seccomp | SELinux | AppArmor | |
|---|---|---|---|
| Profile CRD | Yes | Yes | Yes |
| Install profiles in cluster | Yes | Yes | Yes |
| Remove unused profiles from cluster | Yes | Yes | Yes |
| Profile Recording (audit logs) | Yes | Yes | No |
| Profile Recording (eBPF) | Yes | No | Yes |
| Profile Binding to container images | Yes | No | No |
| Audit log enrichment | Yes | Yes | Yes |
For information about the security model and what permissions each feature requires, refer to SPO's security model.
The motivation behind the project can be found in the corresponding RFC.
Related Kubernetes Enhancement Proposals (KEPs) which have direct influence on this project:
Next to those KEPs, here are existing approaches for security profiles in the Kubernetes world:
If you're interested in contributing to SPO, please see the developer focused document.
We schedule a monthly meeting every last Thursday of a month.
Learn how to engage with the Kubernetes community on the community page.
You can reach the maintainers of this project at:
Participation in the Kubernetes community is governed by the Kubernetes Code of Conduct.
FAQs
Unknown package
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.

Product
Socket is launching experimental protection for Chrome extensions, scanning for malware and risky permissions to prevent silent supply chain attacks.

Product
Add secure dependency scanning to Claude Desktop with Socket MCP, a one-click extension that keeps your coding conversations safe from malicious packages.