
Security News
Feross on TBPN: How North Korea Hijacked Axios
Socket CEO Feross Aboukhadijeh breaks down how North Korea hijacked Axios and what it means for the future of software supply chain security.
@ccusage/codex
Advanced tools

Analyze OpenAI Codex CLI usage logs with the same reporting experience as
ccusage.
⚠️ Beta: The Codex CLI support is experimental. Expect breaking changes until the upstream Codex tooling stabilizes.
# Recommended - always include @latest
npx @ccusage/codex@latest --help
bunx @ccusage/codex@latest --help # ⚠️ MUST include @latest with bunx
# Alternative package runners
pnpm dlx @ccusage/codex
pnpx @ccusage/codex
# Using deno (with security flags)
deno run -E -R=$HOME/.codex/ -S=homedir -N='raw.githubusercontent.com:443' npm:@ccusage/codex@latest --help
⚠️ Critical for bunx users: Bun 1.2.x's bunx prioritizes binaries matching the package name suffix when given a scoped package. For
@ccusage/codex, it looks for acodexbinary in PATH first. If you have an existingcodexcommand installed (e.g., GitHub Copilot's codex), that will be executed instead. Always usebunx @ccusage/codex@latestwith the version tag to force bunx to fetch and run the correct package.
Since npx @ccusage/codex@latest is quite long to type repeatedly, we strongly recommend setting up a shell alias:
# bash/zsh: alias ccusage-codex='bunx @ccusage/codex@latest'
# fish: alias ccusage-codex 'bunx @ccusage/codex@latest'
# Then simply run:
ccusage-codex daily
ccusage-codex monthly --json
💡 The CLI looks for Codex session JSONL files under
CODEX_HOME(defaults to~/.codex).
# Daily usage grouped by date (default command)
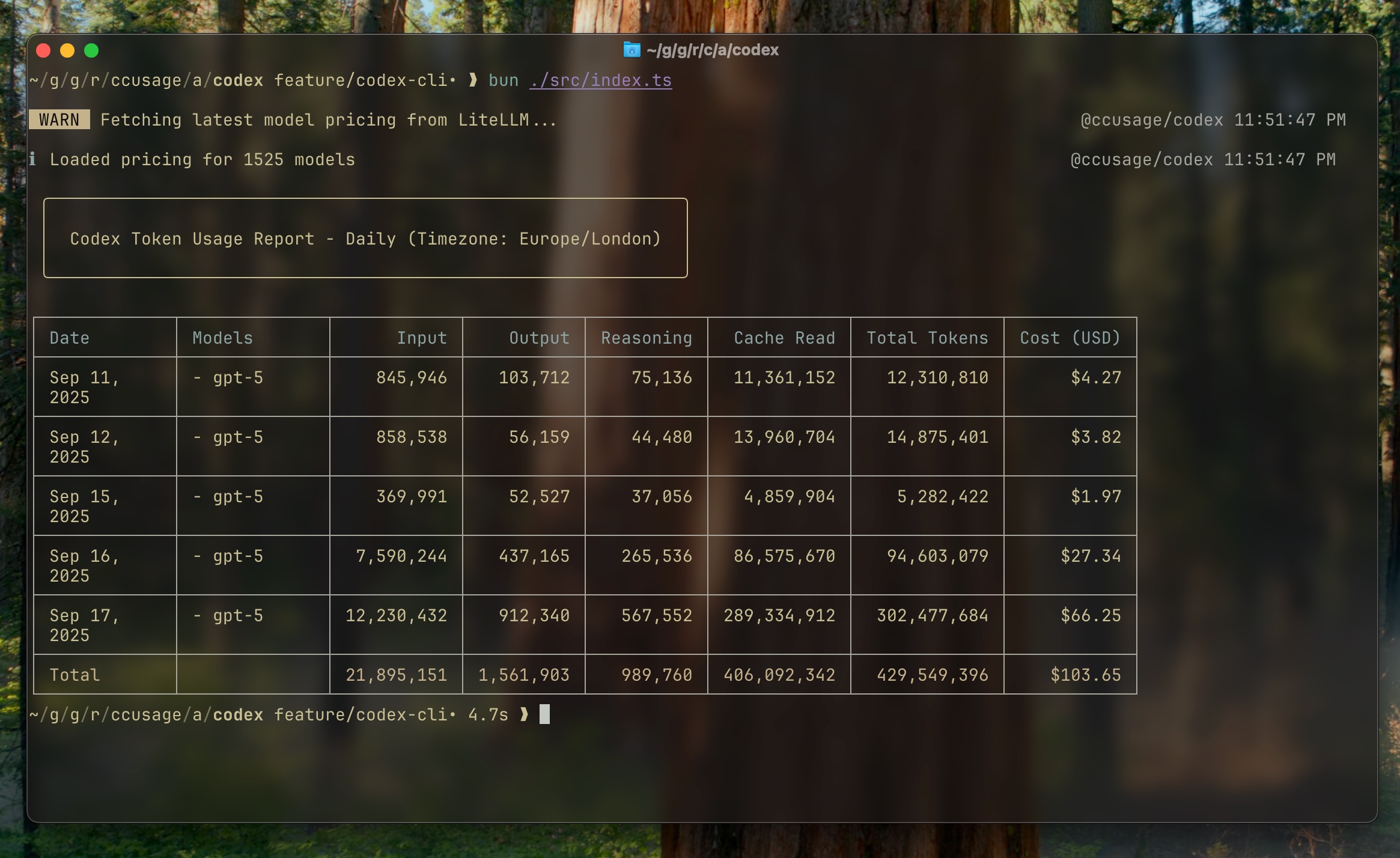
npx @ccusage/codex@latest daily
# Date range filtering
npx @ccusage/codex@latest daily --since 20250911 --until 20250917
# JSON output for scripting
npx @ccusage/codex@latest daily --json
# Monthly usage grouped by month
npx @ccusage/codex@latest monthly
# Monthly JSON report for integrations
npx @ccusage/codex@latest monthly --json
# Session-level detailed report
npx @ccusage/codex@latest sessions
Useful environment variables:
CODEX_HOME – override the root directory that contains Codex session foldersLOG_LEVEL – controla consola log verbosity (0 silent … 5 trace)ℹ️ The CLI now relies on the model metadata recorded in each turn_context. Sessions emitted during early September 2025 that lack this metadata are skipped to avoid mispricing. Newer builds of the Codex CLI restore the model field, and aliases such as gpt-5-codex automatically resolve to the correct LiteLLM pricing entry.
📦 For legacy JSONL files that never emitted turn_context metadata, the CLI falls back to treating the tokens as gpt-5 so that usage still appears in reports (pricing is therefore approximate for those sessions). In JSON output you will also see "isFallback": true on those model entries.
ccusage CLIFor detailed guides and examples, visit ccusage.com/guide/codex.
Check out ccusage: The Claude Code cost scorecard that went viral
MIT © @ryoppippi
FAQs
Usage analysis tool for OpenAI Codex sessions
The npm package @ccusage/codex receives a total of 4,932 weekly downloads. As such, @ccusage/codex popularity was classified as popular.
We found that @ccusage/codex demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Socket CEO Feross Aboukhadijeh breaks down how North Korea hijacked Axios and what it means for the future of software supply chain security.

Security News
OpenSSF has issued a high-severity advisory warning open source developers of an active Slack-based campaign using impersonation to deliver malware.

Research
/Security News
Malicious packages published to npm, PyPI, Go Modules, crates.io, and Packagist impersonate developer tooling to fetch staged malware, steal credentials and wallets, and enable remote access.