
Product
Introducing Socket Firewall Enterprise: Flexible, Configurable Protection for Modern Package Ecosystems
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.
@coast-team/mute-crypto
Advanced tools
Algorithm generating a cryptographic key for MUTE collaborative session
This library implements the conference key distribution system designed by Burmester and Desmedt[1].
To secure the communications in the peer-to-peer collaborative editor Mute it is fundamental to implement an end-to-end encryption system. The main characteristic of this kind of system is that the secret key (used to encrypt the communications) must only be known to the communicating parties (i.e. no server/intermediary must have access to the keys). It is also essential that the secret keys must not be communicated through the network but rather negotiated. This goal is achieved by a protocol that allow the parties to compute the same key without ever send it through the network (even by out-of-band channel). One of these is the Diffie-Hellman Key exchange protocol. Mute-Crypto implements an n-party Diffie-Hellman key exchange generalization of this protocol.
[1]: A Secure and Efficient Conference Key Distribution System
FAQs
Algorithm generating a cryptographic key for MUTE collaborative session
We found that @coast-team/mute-crypto demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 3 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
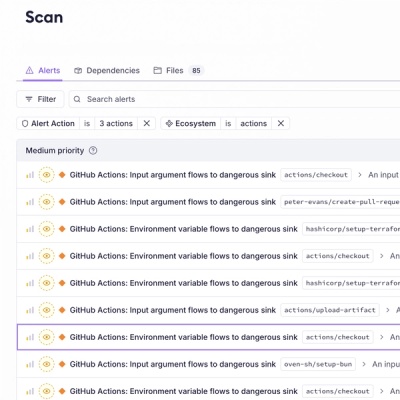
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.