
Security News
Feross on Risky Business Weekly Podcast: npm’s Ongoing Supply Chain Attacks
Socket CEO Feross Aboukhadijeh joins Risky Business Weekly to unpack recent npm phishing attacks, their limited impact, and the risks if attackers get smarter.
@conet.project/mvp-dl
Advanced tools
CoNET “Stealth Internet” Infrastructure (CoNET-DL) is a peer-to-peer computer network which uses traffic type obfuscation based HTML protocol to build at the top of the Open Systems Interconnection (OSI) communications model. CoNET-DL lets both parties of the communication use wallet addresses rather than IP addresses and a pair of public and private keys using asymmetric encryption technology to encrypt the communication content.
Traditional tools based on changing clients IP addresses like VPN and Tor can no longer meet people’s increasing emphasis on privacy. Although the wallet address of the blockchain can also be used to achieve private communication, both parties in the communication need to wait for the generation of new blocks and cannot achieve instant communication. It cannot be applied in the client-server model of the Internet.
npm i @conet.project/conet-mvp-dl -g
conet-mvp-si
Copyright (c) Kloak Information Technologies Inc. All rights reserved.
Licensed under the MIT License.
The MIT License (MIT) Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
FAQs
A New Internet Zero Censorship, Complete Privacy
We found that @conet.project/mvp-dl demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Socket CEO Feross Aboukhadijeh joins Risky Business Weekly to unpack recent npm phishing attacks, their limited impact, and the risks if attackers get smarter.

Product
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Research
/Security News
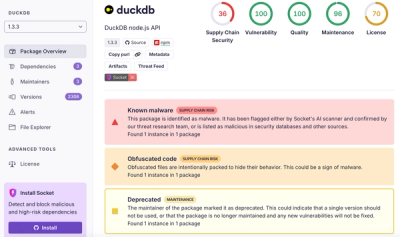
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.