
Product
Introducing Pull Request Stories to Help Security Teams Track Supply Chain Risks
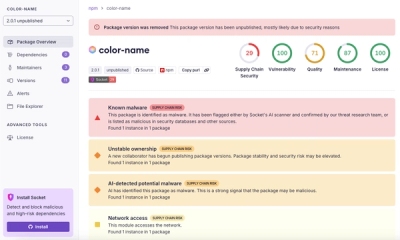
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
@devlikeapro/n8n-nodes-petstore
Advanced tools

Example (Template) project for Petstore OpenAPI spec using devlikeapro/n8n-openapi-node

Before start modifying the project, we kindly recommend to run the Petstore locally.
Make sure you're using Node.js > 20 (we're using nvm):
nvm install v22.8
nvm use v22.8
npm install n8n -g
n8n --version
n8n start
Open http://localhost:5678 in your browser and configure it
npm install
npm run test
npm run build
npm link
cd ~/.n8n
mkdir -p custom
cd custom
npm init # press Enter for all questions
npm link @devlikeapro/n8n-nodes-petstore
n8n start
Find Petstore in the node list and add it to your workflow


Now you're ready to start building your n8n community node!
openapi.json in nodes/{YourNode}logo.svgPetstore matches to YourNodepetstore matches to yournodedevlikeapro to {yourgithubname}npm install
npm run test
npm run build
npm link
Add node to n8n:
cd ~/.n8n
mkdir -p custom
cd custom
npm init # press Enter for all questions
npm link @devlikeapro/n8n-nodes-petstore
Start n8n:
n8n start
NPM_TOKEN in GitHub Actions1.0.0 in your project@{yourgithubname}/n8n-nodes-{yournode}FAQs
n8n node to connect with Petstore
We found that @devlikeapro/n8n-nodes-petstore demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 0 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.