
Product
Introducing Rust Support in Socket
Socket now supports Rust and Cargo, offering package search for all users and experimental SBOM generation for enterprise projects.
@ekolabs/eko
Advanced tools
eko is the main command-line tool for Eko project development. Use the eko command to create a new project, test your project, deploy your project, create project episodes, etc.
First, you will need to sign up for a user at Eko Studio.
Install globally using npm install -g @ekolabs/eko.
Login in with you studio user id by running eko user login.
Create your first project by running eko project create --name=myFirstProject
See the eko usage by running eko --help
NOTE: on Windows, you will need a recent version of NPM, see package npm-windows-upgrade for instructions. Version 3.9.6 has been tested in windows environments and works well.
Play your project locally: eko project test
Deploy your project to staging eko project deploy --staging
Prepare your project for multiple episodes eko project templatize
Create a new episode eko episode create --num=1
Switch to specific episode eko episode generate --src=ep001
FAQs
eko command-line interface for project development
The npm package @ekolabs/eko receives a total of 0 weekly downloads. As such, @ekolabs/eko popularity was classified as not popular.
We found that @ekolabs/eko demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket now supports Rust and Cargo, offering package search for all users and experimental SBOM generation for enterprise projects.
Product
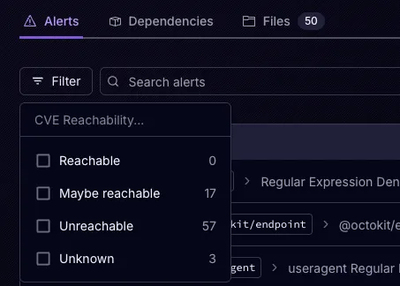
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.

Product
Socket is launching experimental protection for Chrome extensions, scanning for malware and risky permissions to prevent silent supply chain attacks.