
Security News
/Research
Wallet-Draining npm Package Impersonates Nodemailer to Hijack Crypto Transactions
Malicious npm package impersonates Nodemailer and drains wallets by hijacking crypto transactions across multiple blockchains.
@loopback/authentication
Advanced tools
A LoopBack 4 component for authentication support. Its corresponding documentation is in LoopBack component authentication
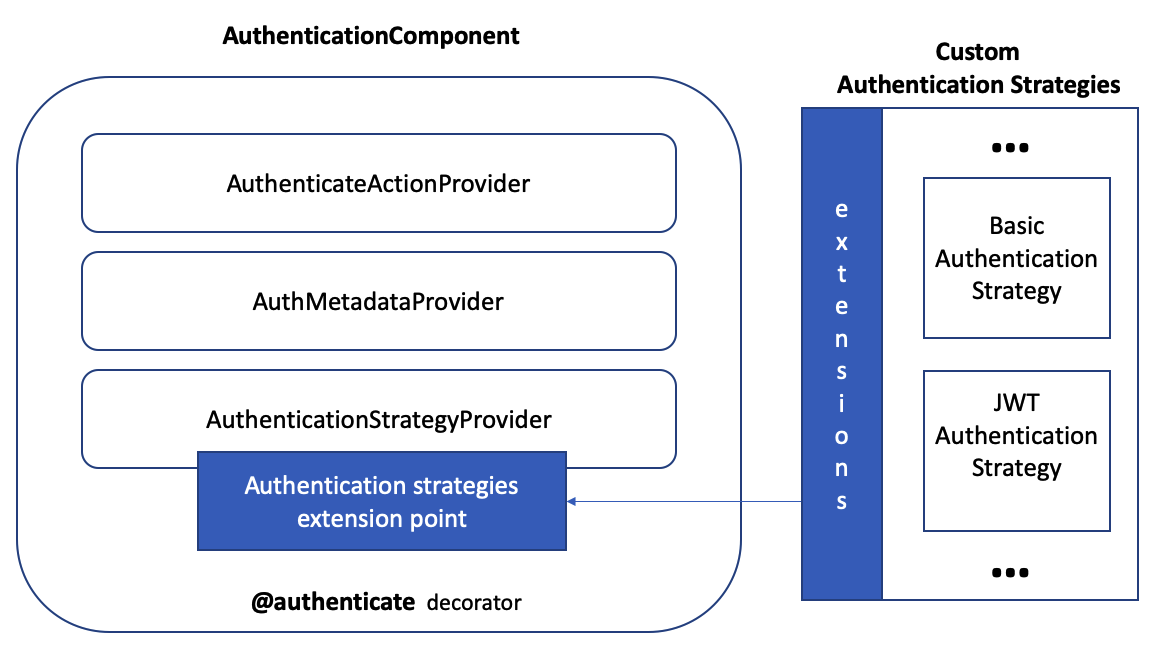
This component contains the core logic for the authentication layer in LoopBack 4.
It contains:
npm install --save @loopback/authentication
Load the AuthenticationComponent into your application.
Extension developers need to:
Application Developers need to:
Create and register a passport based strategy
For detailed documentation, see AuthenticationComponent.
For a tutorial on how to add JWT authentication to an application, see How to secure your LoopBack 4 application with JWT authentication.
For some background on our design decisions, please read Multiple Authentication strategies.
Starting from version @loobpack/authentication@3.0.0, UserProfile needs to
be imported from @loopback/security and it's not backward compatible with the
one exported from @loobpack/authentication@2.x. Make sure you follow the
new tutorial
to build the authentication system.
run npm test from the root folder.
See all contributors.
MIT
FAQs
A LoopBack component for authentication support.
We found that @loopback/authentication demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 7 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
/Research
Malicious npm package impersonates Nodemailer and drains wallets by hijacking crypto transactions across multiple blockchains.

Security News
This episode explores the hard problem of reachability analysis, from static analysis limits to handling dynamic languages and massive dependency trees.

Security News
/Research
Malicious Nx npm versions stole secrets and wallet info using AI CLI tools; Socket’s AI scanner detected the supply chain attack and flagged the malware.