
Product
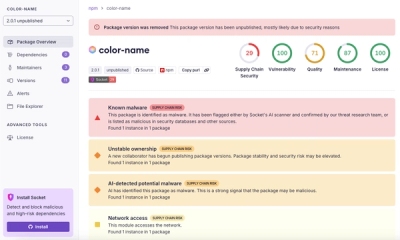
Introducing Pull Request Stories to Help Security Teams Track Supply Chain Risks
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
@nocobase/cache
Advanced tools
<video width="100%" controls> <source src="https://static-docs.nocobase.com/NocoBase0510.mp4" type="video/mp4"> </video>
NocoBase is a scalability-first, open-source no-code development platform.
Instead of investing years of time and millions of dollars in research and development, deploy NocoBase in a few minutes and you'll have a private, controllable, and extremely scalable no-code development platform!
Homepage:
https://www.nocobase.com/
Online Demo:
https://demo.nocobase.com/new
Documents:
https://docs.nocobase.com/
Commericial license & plugins:
https://www.nocobase.com/en/commercial
License agreement:
https://www.nocobase.com/en/agreement
FAQs
<video width="100%" controls> <source src="https://static-docs.nocobase.com/NocoBase0510.mp4" type="video/mp4"> </video>
The npm package @nocobase/cache receives a total of 740 weekly downloads. As such, @nocobase/cache popularity was classified as not popular.
We found that @nocobase/cache demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.

Research
Four npm packages disguised as cryptographic tools steal developer credentials and send them to attacker-controlled Telegram infrastructure.