
Security News
Feross on Risky Business Weekly Podcast: npm’s Ongoing Supply Chain Attacks
Socket CEO Feross Aboukhadijeh joins Risky Business Weekly to unpack recent npm phishing attacks, their limited impact, and the risks if attackers get smarter.
@pagopa/eslint-config
Advanced tools
This package provides PagoPA's `eslint.config.js` as an extensible shared config.
This package provides PagoPA's eslint.config.js as an extensible shared config.
Install eslint and @pagopa/eslint-config
yarn add -D eslint @pagopa/eslint-config
Create a file names eslint.config.js at the root of your workspace with the following content
[!TIP]
If your workspace uses CommonJS, name this fileeslint.config.mjs
import pagopa from "@pagopa/eslint-config";
export default [...pagopa];
Add lint and lint:check scripts in your package.json
{
"scripts": {
"lint": "eslint --fix src",
"lint:check": "eslint src"
}
}
FAQs
This package provides PagoPA's `eslint.config.js` as an extensible shared config.
The npm package @pagopa/eslint-config receives a total of 2,687 weekly downloads. As such, @pagopa/eslint-config popularity was classified as popular.
We found that @pagopa/eslint-config demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 4 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Socket CEO Feross Aboukhadijeh joins Risky Business Weekly to unpack recent npm phishing attacks, their limited impact, and the risks if attackers get smarter.

Product
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Research
/Security News
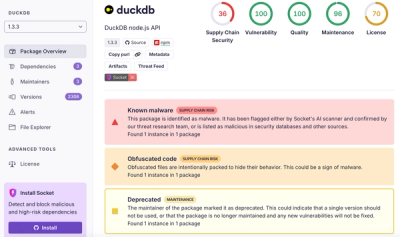
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.