
Research
GemStuffer Campaign Abuses RubyGems as Exfiltration Channel Targeting UK Local Government
GemStuffer abuses RubyGems as an exfiltration channel, packaging scraped UK council portal data into junk gems published from new accounts.
@sentry/cli
Advanced tools
A command line utility to work with Sentry. https://docs.sentry.io/hosted/learn/cli/

This is a Sentry command line client for some generic tasks. Right now this is primarily used to upload debug symbols to Sentry if you are not using the fastlane tools.
The recommended way to install is with everybody's favorite curl to bash:
curl -sL https://sentry.io/get-cli/ | bash
Additionally you can also install this binary via npm:
npm install @sentry/cli
When installing globally, make sure to have set correct permissions on the global node_modules directory. If this is not possible in your environment or still produces an EACCESS error, install as root:
sudo npm install -g @sentry/cli --unsafe-perm
By default, this package will download sentry-cli from the CDN managed by Fastly.
To use a custom CDN, set the npm config property sentrycli_cdnurl. The downloader will append
"/<version>/sentry-cli-<dist>".
npm install @sentry/cli --sentrycli_cdnurl=https://mymirror.local/path
Or add property into your .npmrc file (https://www.npmjs.org/doc/files/npmrc.html)
sentrycli_cdnurl=https://mymirror.local/path
Another option is to use the environment variable SENTRYCLI_CDNURL.
SENTRYCLI_CDNURL=https://mymirror.local/path npm install @sentry/cli
If you're installing the CLI with NPM from behind a proxy, the install script will
use either NPM's configured HTTPS proxy server, or the value from your HTTPS_PROXY
environment variable.
A homebrew recipe is provided in the getsentry/tools tap:
brew install getsentry/tools/sentry-cli
As of version 1.25.0, there is an official Docker image that comes with
sentry-cli preinstalled. If you prefer a specific version, specify it as tag.
The latest development version is published under the edge tag. In production,
we recommend you to use the latest tag. To use it, run:
docker pull getsentry/sentry-cli
docker run --rm -v $(pwd):/work getsentry/sentry-cli --help
In case you want to compile this yourself, you need to install at minimum the following dependencies:
Use cargo to compile:
$ cargo build
Also, there is a Dockerfile that builds an Alpine-based Docker image with
sentry-cli in the PATH. To build and use it, run:
docker build -t sentry-cli .
docker run --rm -v $(pwd):/work sentry-cli --help
Similar to the source map upload feature of @sentry/cli, bugsnag-sourcemaps is a tool for uploading source maps to Bugsnag, another error tracking service. It provides a focused functionality compared to the broader scope of @sentry/cli.
rollbar-cli is a command line tool for interacting with Rollbar, an alternative to Sentry for error monitoring and reporting. It offers functionalities similar to @sentry/cli, such as managing releases and uploading source maps, tailored for Rollbar's platform.
FAQs
A command line utility to work with Sentry. https://docs.sentry.io/hosted/learn/cli/
The npm package @sentry/cli receives a total of 12,675,184 weekly downloads. As such, @sentry/cli popularity was classified as popular.
We found that @sentry/cli demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Research
GemStuffer abuses RubyGems as an exfiltration channel, packaging scraped UK council portal data into junk gems published from new accounts.

Company News
Socket was named to the Rising in Cyber 2026 list, recognizing 30 private cybersecurity startups selected by CISOs and security executives.
Research
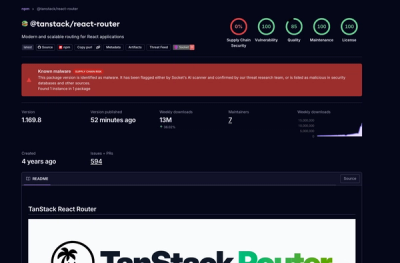
Socket detected 84 compromised TanStack npm package artifacts modified with suspected CI credential-stealing malware.