
Product
Introducing Socket Firewall Enterprise: Flexible, Configurable Protection for Modern Package Ecosystems
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.
@travetto/auth-rest-jwt
Advanced tools
Rest authentication JWT integration support for the Travetto framework
Install: @travetto/auth-rest-jwt
npm install @travetto/auth-rest-jwt
# or
yarn add @travetto/auth-rest-jwt
One of Rest Auth's main responsibilities is being able to send and receive authentication/authorization information from the client. This data can be encoded in many different forms, and this module provides the ability to encode into and decode from JWTs. This module fulfills the contract required by Rest Auth of being able to encode and decode a user principal, by leveraging JWT's token generation features.
The token can be encoded as a cookie or as a header depending on configuration. Additionally, the encoding process allows for auto-renewing of the token if that is desired. When encoding as a cookie, this becomes a seamless experience, and can be understood as a light-weight session.
The JWTPrincipalEncoder is exposed as a tool for allowing for converting an authenticated principal into a JWT, and back again.
Code: JWTPrincipalEncoder
import { AuthContext, Principal } from '@travetto/auth';
import { PrincipalEncoder } from '@travetto/auth-rest';
import { AppError, Runtime, TimeSpan, TimeUtil } from '@travetto/runtime';
import { Config } from '@travetto/config';
import { Inject, Injectable } from '@travetto/di';
import { FilterContext } from '@travetto/rest';
import { JWTUtil, Payload } from '@travetto/jwt';
import { Ignore } from '@travetto/schema';
@Config('rest.auth.jwt')
export class RestJWTConfig {
mode: 'cookie' | 'header' | 'all' = 'header';
header = 'Authorization';
cookie = 'trv.auth';
signingKey?: string;
headerPrefix = 'Bearer';
maxAge: TimeSpan | number = '1h';
rollingRenew: boolean = false;
@Ignore()
maxAgeMs: number;
get cookieMode(): boolean {
return this.mode === 'cookie' || this.mode === 'all';
}
get headerMode(): boolean {
return this.mode === 'header' || this.mode === 'all';
}
postConstruct(): void {
this.maxAgeMs = TimeUtil.asMillis(this.maxAge);
if (!this.signingKey && Runtime.production) {
throw new AppError('The default signing key is only valid for development use, please specify a config value at rest.auth.jwt.signingKey');
}
this.signingKey ??= 'dummy';
}
}
/**
* Principal encoder via JWT
*/
@Injectable()
export class JWTPrincipalEncoder implements PrincipalEncoder {
@Inject()
config: RestJWTConfig;
@Inject()
authContext: AuthContext;
toJwtPayload(p: Principal): Payload {
const exp = TimeUtil.asSeconds(p.expiresAt!);
const iat = TimeUtil.asSeconds(p.issuedAt!);
return {
auth: {
...p,
},
exp,
iat,
iss: p.issuer,
sub: p.id,
};
}
/**
* Get token for principal
*/
async getToken(p: Principal): Promise<string> {
return await JWTUtil.create(this.toJwtPayload(p), { key: this.config.signingKey });
}
/**
* Rewrite token with new permissions
*/
updateTokenPermissions(token: string, permissions: string[]): Promise<string> {
return JWTUtil.rewrite<{ auth: Principal }>(
token,
p => ({
...p,
auth: {
...p.auth,
permissions
}
}),
{ key: this.config.signingKey }
);
}
/**
* Verify token to principal
* @param token
*/
async verifyToken(token: string, setActive = false): Promise<Principal> {
const res = (await JWTUtil.verify<{ auth: Principal }>(token, { key: this.config.signingKey })).auth;
if (setActive) {
this.authContext.authToken = { value: token, type: 'jwt' };
}
return {
...res,
expiresAt: new Date(res.expiresAt!),
issuedAt: new Date(res.issuedAt!),
};
}
/**
* Write context
*/
async encode({ res }: FilterContext, p: Principal | undefined): Promise<void> {
if (p) {
const token = await this.getToken(p);
if (this.config.cookieMode) {
res.cookies.set(this.config.cookie, token, { expires: p.expiresAt });
}
if (this.config.headerMode) {
res.setHeader(this.config.header, [this.config.headerPrefix, token].join(' ').trimStart());
}
} else if (this.config.cookieMode) {
res.cookies.set(this.config.cookie, '', { expires: TimeUtil.fromNow(-1, 'h') }); // Clear out cookie
}
}
/**
* Run before encoding, allowing for session extending if needed
*/
preEncode(p: Principal): void {
p.expiresAt ??= TimeUtil.fromNow(this.config.maxAgeMs);
p.issuedAt ??= new Date();
if (this.config.rollingRenew) {
const end = p.expiresAt.getTime();
const midPoint = end - this.config.maxAgeMs / 2;
if (Date.now() > midPoint) { // If we are past the half way mark, renew the token
p.issuedAt = new Date();
p.expiresAt = TimeUtil.fromNow(this.config.maxAgeMs); // This will trigger a re-send
}
}
}
/**
* Read JWT from request
*/
async decode({ req }: FilterContext): Promise<Principal | undefined> {
let token: string | undefined = undefined;
if (this.config.cookieMode) {
token ??= req.cookies.get(this.config.cookie);
}
if (this.config.headerMode) {
const header = req.headerFirst(this.config.header);
if (header?.startsWith(this.config.headerPrefix)) {
token ??= header.replace(this.config.headerPrefix, '').trim();
}
}
if (token) {
return await this.verifyToken(token, true);
}
}
}
As you can see, the encode token just creates a JWT based on the principal provided, and decoding verifies the token, and returns the principal.
FAQs
Rest authentication JWT integration support for the Travetto framework
We found that @travetto/auth-rest-jwt demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
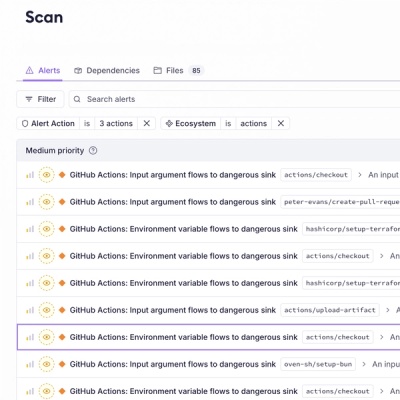
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.