
Security News
MCP Steering Committee Launches Official MCP Registry in Preview
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.
all-the-public-replicate-models
Advanced tools
Metadata for all the public models on Replicate, bundled up into an npm package
Metadata for all1 the public models on Replicate, bundled up into an npm package.
This package also includes historical daily run counts for each model, which are updated daily.
npm install all-the-public-replicate-models
Full-bodied usage (all the metadata, ~17MB)
import models from 'all-the-public-replicate-models'
console.log(models)
Lite usage (just the basic metadata, ~375K):
import models from 'all-the-public-replicate-models/lite'
console.log(models)
Find the top 10 models by run count:
import models from 'all-the-public-replicate-models'
import {chain} from 'lodash-es'
const mostRun = chain(models).orderBy('run_count', 'desc').take(10).value()
console.log({mostRun})
This package also includes historical daily run counts for each model, which are updated daily.
import stats from 'all-the-public-replicate-models/stats'
console.log(stats["black-forest-labs/flux-schnell"].slice(-5))
/*
[
{ date: '2025-01-03', totalRuns: 176951005, dailyRuns: 1071498 },
{ date: '2025-01-04', totalRuns: 178025758, dailyRuns: 1074753 },
{ date: '2025-01-05', totalRuns: 179119496, dailyRuns: 1093738 },
{ date: '2025-01-06', totalRuns: 180272877, dailyRuns: 1153381 },
{ date: '2025-01-07', totalRuns: 181445133, dailyRuns: 1172256 }
]
*/
See example.js for a code snippet that uses the stats.
The CLI dumps the model metadata to standard output as a big JSON object:
$ npx all-the-public-replicate-models
The output will be:
[
{...},
{...},
{...},
]
You can use jq to filter the output. Here's an example that finds all the whisper models and sorts them by run count:
npx all-the-public-replicate-models | jq -r 'map(select(.name | contains("whisper"))) | sort_by(.run_count) | reverse | .[] | "\(.url) \(.run_count)"'
Or you can dump all the model data to a file:
npx all-the-public-replicate-models > models.json
Technically it's not all the models, but every model that is public, has at least one published version, and has at least one example prediction. ↩
FAQs
Metadata for all the public models on Replicate, bundled up into an npm package
We found that all-the-public-replicate-models demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 5 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.

Product
Socket’s new Pull Request Stories give security teams clear visibility into dependency risks and outcomes across scanned pull requests.
Research
/Security News
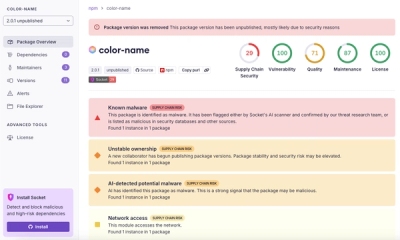
npm author Qix’s account was compromised, with malicious versions of popular packages like chalk-template, color-convert, and strip-ansi published.