
Product
Introducing Socket Firewall Enterprise: Flexible, Configurable Protection for Modern Package Ecosystems
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.
berish-linq
Advanced tools
Edit a file, create a new file, and clone from Bitbucket in under 2 minutes
When you're done, you can delete the content in this README and update the file with details for others getting started with your repository.
We recommend that you open this README in another tab as you perform the tasks below. You can watch our video for a full demo of all the steps in this tutorial. Open the video in a new tab to avoid leaving Bitbucket.
You’ll start by editing this README file to learn how to edit a file in Bitbucket.
Next, you’ll add a new file to this repository.
Before you move on, go ahead and explore the repository. You've already seen the Source page, but check out the Commits, Branches, and Settings pages.
Use these steps to clone from SourceTree, our client for using the repository command-line free. Cloning allows you to work on your files locally. If you don't yet have SourceTree, download and install first. If you prefer to clone from the command line, see Clone a repository.
Now that you're more familiar with your Bitbucket repository, go ahead and add a new file locally. You can push your change back to Bitbucket with SourceTree, or you can add, commit, and push from the command line.
FAQs
LINQ - very usefull helper for working with arrays and collections
We found that berish-linq demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
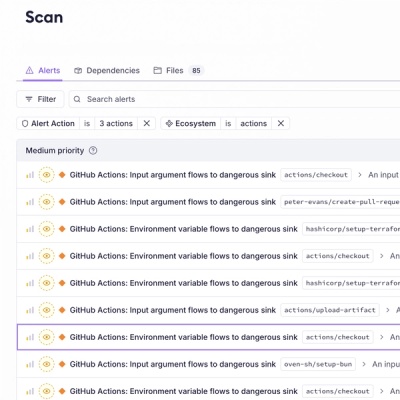
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.