Research
wget to Wipeout: Malicious Go Modules Fetch Destructive Payload
Socket's research uncovers three dangerous Go modules that contain obfuscated disk-wiping malware, threatening complete data loss.
cdk8s-redis
Advanced tools
Redis constructs for cdk8s
Basic implementation of a Redis construct for cdk8s. Contributions are welcome!
The following will define a Redis cluster with a primary and 2 replicas:
import { Redis } from 'cdk8s-redis';
// inside your chart:
const redis = new Redis(this, 'my-redis');
DNS names can be obtained from redis.primaryHost and redis.replicaHost.
You can specify how many replicas to define:
new Redis(this, 'my-redis', {
replicas: 4
});
Or, you can specify no replicas:
new Redis(this, 'my-redis', {
replicas: 0
});
Distributed under the Apache 2.0 license.
FAQs
Basic implementation of a Redis construct for cdk8s.
The npm package cdk8s-redis receives a total of 2,758 weekly downloads. As such, cdk8s-redis popularity was classified as popular.
We found that cdk8s-redis demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Research
Socket's research uncovers three dangerous Go modules that contain obfuscated disk-wiping malware, threatening complete data loss.
Research
Socket uncovers malicious packages on PyPI using Gmail's SMTP protocol for command and control (C2) to exfiltrate data and execute commands.
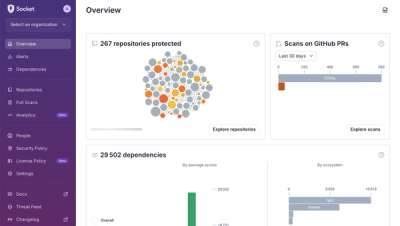
Product
We redesigned Socket's first logged-in page to display rich and insightful visualizations about your repositories protected against supply chain threats.