
Security News
Crates.io Users Targeted by Phishing Emails
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
cfn-natroute
Advanced tools
AWS CloudFormation does not support AWS Routes to managed nat. This is a Lambda-backed custom resource to add support for AWS Routes to managed nat to CloudFormation.
This package on NPM
This package on GitHub
This Lambda makes use of the Lambda-Backed CloudFormation Custom Resource flow module, cfn-lambda (GitHub / NPM).
"MyNatgateway": {
"Type": "Custom::Natgateway",
"DependsOn": "MyEIP",
"Properties": {
"ServiceToken": {
"Fn::Join": [
":",
[
"arn",
"aws",
"lambda",
{
"Ref": "AWS::Region"
},
{
"Ref": "AWS::AccountId"
},
"function",
"cfn-natgateway-0-1-1"
]
]
},
"SubnetId": {
"Ref": "PublicSubnet"
},
"AllocationId": {
"Fn::GetAtt": [ "MyEIP", "AllocationId"]
}
}
},
"PrivateRouteTable": {
"Type": "AWS::EC2::RouteTable",
"DependsOn": "MyNatgateway2",
"Properties": {
"VpcId": {
"Ref": "VPC"
},
"Tags": [{
"Key": "Application",
"Value": {
"Ref": "AWS::StackId"
}
}, {
"Key": "Network",
"Value": "Private"
}]
}
},
"PrivateRoute": {
"Type": "Custom::Natroute",
"DependsOn": "MyNatgateway",
"Properties": {
"ServiceToken": {
"Fn::Join": [
":",
[
"arn",
"aws",
"lambda",
{
"Ref": "AWS::Region"
},
{
"Ref": "AWS::AccountId"
},
"function",
"cfn-natroute-0-1-1"
]
]
},
"RouteTableId": {
"Ref": "PrivateRouteTable"
},
"DestinationCidrBlock": "0.0.0.0/0",
"NatGatewayId": {
"Ref": "MyNatgateway"
}
}
},
The way that takes 10 seconds...
# Have aws CLI installed + permissions for IAM and Lamdba
npm install cfn-natgateway cfn-natroute $ npm install cfn-lambda cfn-natgateway cfn-natroute $ node -e "var r='us-east-1';var c=require('cfn-lambda');c.deploy('cfn-natgateway', r, [r], null);c.deploy('cfn-natroute', r, [r], null);"
You will have this resource installed in the us-east-1 region!
... And the way more difficult way.
IMPORTANT: With this method, you must install this custom service Lambda in each AWS Region in which you want CloudFormation to be able to access the Natgateway custom resource!
Zip this repository into /tmp/Natroute.zip
$ cd $REPO_ROOT && zip -r /tmp/Natroute.zip;
Enter a name in the Name blank. I suggest: CfnLambdaResouce-Natroute
Enter a Description (optional).
Toggle Code Entry Type to "Upload a .ZIP file"
Click "Upload", navigate to and select /tmp/Natroute.zip
Set the Timeout under Advanced Settings to 10 sec
Click the Role dropdown then click "Basic Execution Role". This will pop out a new window.
Select IAM Role, then select option "Create a new IAM Role"
Name the role lambda_cfn_natroute (or something descriptive)
Click "View Policy Document", click "Edit" on the right, then hit "OK"
Copy and paste the ./execution-policy.json document.
Hit "Allow". The window will close. Go back to the first window if you are not already there.
Click "Create Function". Finally, done! Now go to Usage. Next time, stick to the instant deploy script.
FAQs
AWS CloudFormation Custom Lambda Resource | AWS Natroute
We found that cfn-natroute demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

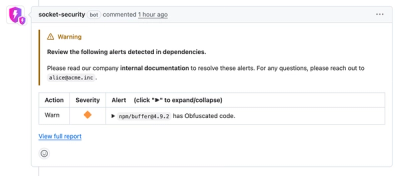
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.

Product
Socket's Rust support is moving to Beta: all users can scan Cargo projects and generate SBOMs, including Cargo.toml-only crates, with Rust-aware supply chain checks.