
Product
Introducing Tier 1 Reachability: Precision CVE Triage for Enterprise Teams
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
crypto-toolkit
Advanced tools
A set of utility functions/wrapper to simplify the development workflow
DEPRECATED
superseded by crypto-magic
A set of utility functions/wrapper to simplify the development workflow
$ npm install crypto-toolkit
Provides easy access to the Node.js Crypto Hash functions. Examples are available in examples/hash.js
// default hex encoding
var _hash = require('crypto-toolkit').Hash('hex');
console.log(_hash.sha256('Hello World'));
require('crypto-toolkit').Hash([encoding:string])
The argument encoding is optional and defines the output encoding of the digest.
The following wrappers are included:
md5(input:mixed, [encoding:string])sha1(input:mixed, [encoding:string])sha2(input:mixed, [encoding:string])sha224(input:mixed, [encoding:string])sha256(input:mixed, [encoding:string])sha384(input:mixed, [encoding:string])sha512(input:mixed, [encoding:string])whirlpool(input:mixed, [encoding:string])var _hash = require('crypto-toolkit').Hash('hex');
// some input
var input = 'Hello World';
// display some hashes
console.log('Default HEX Output');
console.log(' |- MD5 ', _hash.md5(input));
console.log(' |- SHA1 ', _hash.sha1(input));
console.log(' |- SHA256 ', _hash.sha256(input));
console.log(' |- SHA384 ', _hash.sha384(input));
console.log(' |- SHA512 ', _hash.sha512(input));
console.log(' |- WHIRLPOOL', _hash.whirlpool(input));
// override the default output type
console.log('Override the default output settings');
console.log(' |- HEX ', _hash.sha1(input, 'hex'));
console.log(' |- BIN ', _hash.sha1(input, 'binary'));
console.log(' |- BASE64 ', _hash.sha1(input, 'base64'));
console.log('');
Objects/Arrays are automatically serialized as JSON String. The JSON object is then passed into the hash function.
var _hash = require('crypto-toolkit').Hash('hex');
// demo object
var objectInput = {
x: 1,
b: 2,
c: [5,6,7],
d: {
y: 'Hello',
z: 'World'
}
};
console.log('Object Input');
console.log(' |- SHA256 ', _hash.sha256(objectInput));
console.log('');
Create random hashes easily. Just calls the crypto-toolkit.Hash functions with a random content generated by crypto.randomBytes(514) - helpful for random URLs or filenames (e.g. cache hashes).
// url-safe base64
var _randomhash = require('crypto-toolkit').RandomHash('base64-urlsafe');
// all hash function of crypto-toolkit.Hash are supported
console.log(_randomhash.sha256());
// output like b7qhqd-WnKAH_GmBpSpvQrdkfUdLxL0m__XGcLTRsbI
Please open a new issue on GitHub
Crypto-Toolkit is OpenSource and licensed under the Terms of The MIT License (X11). You're welcome to contribute!
FAQs
A set of utility functions/wrapper to simplify the development workflow
The npm package crypto-toolkit receives a total of 20 weekly downloads. As such, crypto-toolkit popularity was classified as not popular.
We found that crypto-toolkit demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Research
/Security News
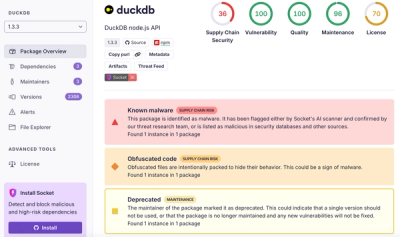
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.