Product
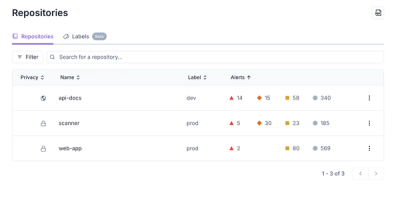
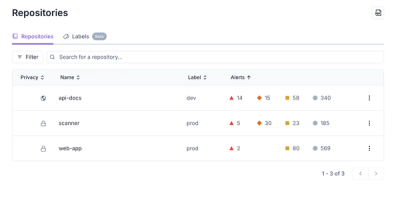
Redesigned Repositories Page: A Faster Way to Prioritize Security Risk
Our redesigned Repositories page adds alert severity, filtering, and tabs for faster triage and clearer insights across all your projects.
eslint-config-magic-component
Advanced tools
ESLint configuration used by Create Magic Component
This package includes the shareable ESLint configuration used by Create Magic Component.
Please refer to its documentation:
The easiest way to use this configuration is with Create Magic Component, which includes it by default. You don’t need to install it separately in Create Magic Component projects.
If you want to use this ESLint configuration in a project not built with Create Magic Component, you can install it with following steps.
First, install this package, ESLint and the necessary plugins.
npm install --save-dev eslint-config-magic-component babel-eslint@7.0.0 eslint@3.8.1 eslint-plugin-flowtype@2.21.0 eslint-plugin-import@2.0.1 eslint-plugin-jsx-a11y@2.2.3 eslint-plugin-react@6.4.1
Then create a file named .eslintrc with following contents in the root folder of your project:
{
"extends": "react-app"
}
That's it! You can override the settings from eslint-config-magic-component by editing the .eslintrc file. Learn more about configuring ESLint on the ESLint website.
Migrating from 0.4.2 to 0.4.3
Inside any created project that has not been ejected, run:
npm install --save-dev --save-exact react-scripts@0.4.3
FAQs
ESLint configuration used by Create Magic Component
The npm package eslint-config-magic-component receives a total of 0 weekly downloads. As such, eslint-config-magic-component popularity was classified as not popular.
We found that eslint-config-magic-component demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Our redesigned Repositories page adds alert severity, filtering, and tabs for faster triage and clearer insights across all your projects.
Security News
Slopsquatting is a new supply chain threat where AI-assisted code generators recommend hallucinated packages that attackers register and weaponize.

Security News
Multiple deserialization flaws in PyTorch Lightning could allow remote code execution when loading untrusted model files, affecting versions up to 2.4.0.