Product
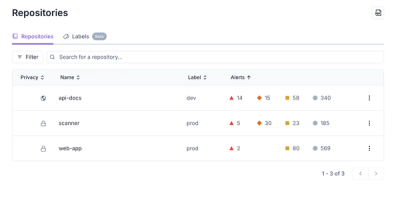
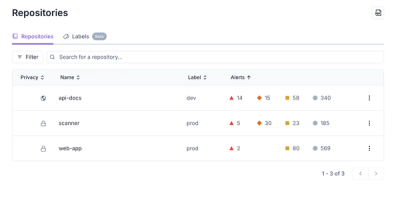
Redesigned Repositories Page: A Faster Way to Prioritize Security Risk
Our redesigned Repositories page adds alert severity, filtering, and tabs for faster triage and clearer insights across all your projects.
fastify-check-runtime-env
Advanced tools
Fastify Plugin to check runtime environment properties
The purpose of this plugin is to let Fastify web applications do some checks
on some properties available at runtime (for example at application startup).
By default any checker method that doesn't satisfy its condition
will throw Error, but in some cases this is configurable via plugin options.
Note that all Chechers features exposed here are in the the library check-runtime-env. For Semantic Versioning checks, see semver.
A common use case is to throw an exception at application startup,
if Node.js version is not compatible with the one set in package.json.
const fastify = require('fastify')()
const engines = require('../package.json').engines
// register plugin with some options
fastify.register(require('fastify-check-runtime-env'), {
// nodeStrictCheckAtStartup: true, // same as default
nodeVersionCheckAtStartup: true,
nodeVersionExpected: engines.node
// nodeVersionExpected: '<=10.13.0 >=200.0.0', // sample failing test
// onCheckMismatch: 'exception' // throw an exception // same as default
})
fastify.listen(3000)
// curl http://127.0.0.1:3000/ => returning the home page, if current Node.js versio in compatible with the expected one
In the example folder there are some simple server scripts that uses the plugin (inline but it's the same using it from npm registry).
Fastify ^4.0.1 , Node.js 14 LTS (14.15.0) or later. Note that plugin releases 3.x are for Fastify 3.x, 4.x are for Fastify 4.x, etc. Old plugin releases (0.x) are for Fastify 2.x but are now obsolete.
Source code is all inside main repo: fastify-check-runtime-env.
Documentation generated from source code (library API): here.
The plugin decorate Fastify and expose some functions:
CheckRuntimeEnv, the checkers implementation, as a class (RuntimeEnvChecker);
but note that to use it you need to wait for this plugin to be
fully loaded and initializedPlugin options are:
onCheckMismatch, define what to do if a checker fails (Node.js version
does not match with the expected one, JavaScript not in strict mode, etc);
by default 'exception' to raise an Error,
but could be 'warning' (to log a message in Fastify logs),
or 'exit' (to stop current Node.js process) with exit code 1nodeStrictCheckAtStartup, flag to tell (when true) to check JavaScript
strict mode; by default true (safer and already enforced as default mode
in modern JavaScript code using classes, ES Modules, etc)nodeVersionCheckAtStartup, flag to tell (when true) to check Node.js version
at application startup; by default falsenodeVersionExpected, the semver string with the expected Node.js version (by default empty, so must be manually provided, for example reading 'package.json' attribute 'engines.node' if specified)all plugin options are optional, and have a default value.
Licensed under Apache-2.0.
FAQs
Fastify Plugin to check runtime environment properties
We found that fastify-check-runtime-env demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Our redesigned Repositories page adds alert severity, filtering, and tabs for faster triage and clearer insights across all your projects.

Security News
Multiple deserialization flaws in PyTorch Lightning could allow remote code execution when loading untrusted model files, affecting versions up to 2.4.0.
Security News
NVD now marks all pre-2018 CVEs as "Deferred," signaling it will no longer enrich older vulnerabilities, further eroding trust in its data.