
Product
Introducing License Overlays: Smarter License Management for Real-World Code
Customize license detection with Socket’s new license overlays: gain control, reduce noise, and handle edge cases with precision.
flex-plugins-utils-env
Advanced tools
Utility for returning environment variables. It is an isomorphic JavaScript module.
Returns true if OS is Windows. It will return false if script is running on the browser.
If the module is used on the server, it will set the environment variable to persist the terminal logs.
Whether the terminal should be persisted or not. Only works on the server.
Whether the scripts should be quiet (no logs). Only works on the server.
Returns true if the log level is debug. Works on both the browser and the server.
Returns true if the log level is trace. Works on both the browser and the server.
Returns the region. Will use the process env if running on the server, otherwise uses the windows.location.
Returns true if script running in CI. Works on the server only.
FAQs
Flex Plugins Environments
The npm package flex-plugins-utils-env receives a total of 4,116 weekly downloads. As such, flex-plugins-utils-env popularity was classified as popular.
We found that flex-plugins-utils-env demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 8 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Customize license detection with Socket’s new license overlays: gain control, reduce noise, and handle edge cases with precision.

Product
Socket now supports Rust and Cargo, offering package search for all users and experimental SBOM generation for enterprise projects.
Product
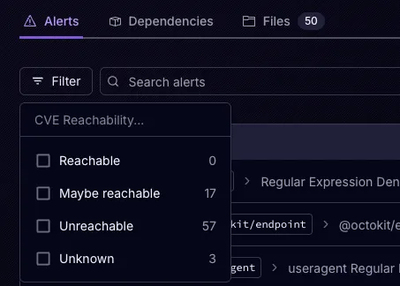
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.