
Product
Introducing Tier 1 Reachability: Precision CVE Triage for Enterprise Teams
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
q-semaphore
Advanced tools
Semaphore implementation for Q promises on Node.js
Install:
npm install q-semaphore
Limit simultaneous access to a resource.
// Create
var sem = require('q-semaphore')(capacity);
// Take
sem.take([n=1]) // returns a promise
// Leave
sem.leave([n=1])
// Limit concurrent db access
var sem = require('semaphore')(1);
var server = require('http').createServer(req, res) {
sem.take().then(function() {
expensive_database_operation(function(err, res) {
sem.leave();
if (err) return res.end("Error");
return res.end(res);
});
});
});
// 2 clients at a time
var sem = require('semaphore')(2);
var server = require('http').createServer(req, res) {
res.write("Then good day, madam!");
sem.take().then(function() {
res.end("We hope to see you soon for tea.");
sem.leave();
});
});
// Rate limit
var sem = require('semaphore')(10);
var server = require('http').createServer(req, res) {
sem.take().then(function() {
res.end(".");
return Q.delay(500);
}).then(sem.leave);
});
MIT
This is based on the abrkn/semaphore.js implementation.
FAQs
semaphore implementation for Q
We found that q-semaphore demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Research
/Security News
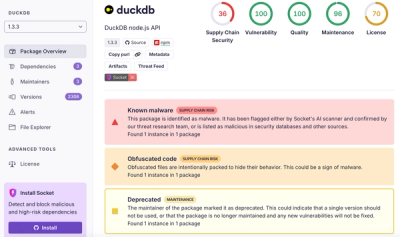
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.