Product
Announcing Precomputed Reachability Analysis in Socket
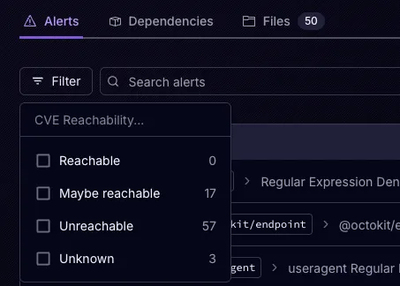
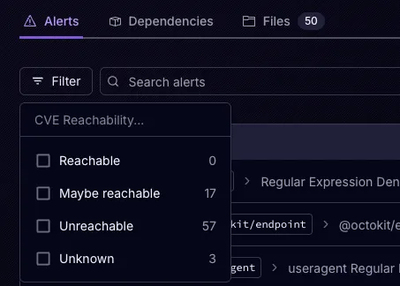
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.
tts-googlehome
Advanced tools
Text-to-Speech with GoogleHome, for Node.js
$ npm install --save tts-googlehome
speakToDeviceAsync(host, text, lang)example
const TtsGoogleHome = require('tts-googlehome');
TtsGoogleHome.speakToDeviceAsync('xxxxxxx.local', 'Hello', 'en-US')
.then(e => {
// -- OK --
console.log('speak OK');
})
.catch(err => {
// -- error --
console.error('speak ERROR:', err);
});
speakToMultiDeviceAsync(hosts, text, lang)example
const TtsGoogleHome = require('tts-googlehome');
TtsGoogleHome.speakToMultiDeviceAsync(['xxxxxxx.local', '192,168.0.xxx'], 'Hello', 'en-US')
.then(e => {
// -- finished --
console.log('speak multi finished:', e);
})
getUrlfromText(text, lang)const TtsGoogleHome = require('tts-googlehome');
const url = TtsGoogleHome.getUrlfromText('Hello', 'en-US');
console.log(url);
castUrlToDeviceAsync(host, url)const TtsGoogleHome = require('tts-googlehome');
const url = 'http://xxxxxxx/audio.mp3';
TtsGoogleHome.castUrlToDeviceAsync('xxxxxxxx.local', url)
.then(e => {
// -- OK --
console.log('cast OK');
})
.catch(err => {
// -- error --
console.error('cast ERROR:', err);
});
MIT
FAQs
text-to-speech with GoogleHome
The npm package tts-googlehome receives a total of 3 weekly downloads. As such, tts-googlehome popularity was classified as not popular.
We found that tts-googlehome demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.

Product
Socket is launching experimental protection for Chrome extensions, scanning for malware and risky permissions to prevent silent supply chain attacks.

Product
Add secure dependency scanning to Claude Desktop with Socket MCP, a one-click extension that keeps your coding conversations safe from malicious packages.