Product
Announcing Precomputed Reachability Analysis in Socket
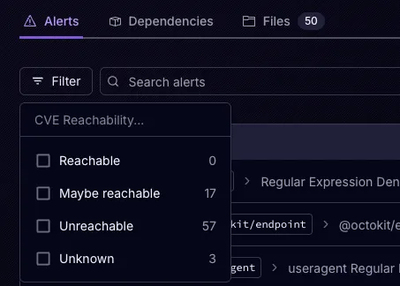
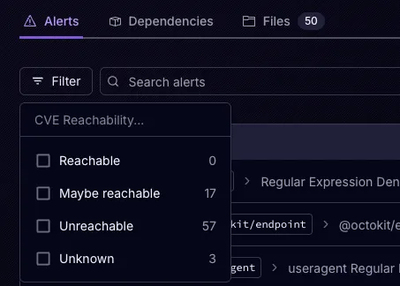
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.
twitter-pin-auth
Advanced tools
A api wrapper to authenticate with twitter using the PIN-based authorization method


A api wrapper to authenticate with twitter using the PIN-based authorization method
Install the module with: npm install twitter-pin-auth
var TwitterPinAuth = require('twitter-pin-auth');
var twitterPinAuth = new TwitterPinAuth('consumerKey', 'consumerSecret', 'screen_name_that_will_prefilled', false); // <- Use Force login with user that alrealy logged in
The 'requestAuthUrl' method is responsible for request a authorization url.
How to use this method with promise
twitterPinAuth.requestAuthUrl()
.then(function(url) {
console.log(url); // "https://twitter.com/oauth/authorize?oauth_token=R7UC5SKKmHfbA7OH4HOpn6WZSrLMZG8G"
}).catch(function(err) {
console.error(err);
});
How to use this method with callback
twitterPinAuth.requestAuthUrl(function(err, url) {
if(err) {
return console.error(err);
}
console.log(url); // "https://twitter.com/oauth/authorize?oauth_token=R7UC5SKKmHfbA7OH4HOpn6WZSrLMZG8G"
});
Parameter: pin
Type: Number
Example: 3321883
The 'authorize' method is responsible for generate a accessTokenKey and accessTokenSecret.
How to use this method with promise
twitterPinAuth.authorize(3321883)
.then(function(data) {
console.log(data.accessTokenKey); // "892902319-b9Mqq07LAvXWBMYYQy6jDv3trzm7V9A8ae2RGPpG"
console.log(data.accessTokenSecret); // "8f59gOM57GeRMkT4gWVI88ljylw2c7Ttc8YMWOf1dYOEI"
}).catch(function(err) {
console.error(err);
});
How to use this method with callback
twitterPinAuth.authorize(3321883, function(err, data) {
if(err) {
return console.error(err);
}
console.log(data.accessTokenKey); // "892902319-b9Mqq07LAvXWBMYYQy6jDv3trzm7V9A8ae2RGPpG"
console.log(data.accessTokenSecret); // "8f59gOM57GeRMkT4gWVI88ljylw2c7Ttc8YMWOf1dYOEI"
});
Please submit all issues and pull requests to the chrisenytc/twitter-pin-auth repository!
If you have any problem or suggestion please open an issue here.
The MIT License
Copyright (c) 2015, Christopher EnyTC
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
FAQs
A api wrapper to authenticate with twitter using the PIN-based authorization method
The npm package twitter-pin-auth receives a total of 1 weekly downloads. As such, twitter-pin-auth popularity was classified as not popular.
We found that twitter-pin-auth demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.

Product
Socket is launching experimental protection for Chrome extensions, scanning for malware and risky permissions to prevent silent supply chain attacks.

Product
Add secure dependency scanning to Claude Desktop with Socket MCP, a one-click extension that keeps your coding conversations safe from malicious packages.