
Security News
The Hidden Blast Radius of the Axios Compromise
The Axios compromise shows how time-dependent dependency resolution makes exposure harder to detect and contain.
MappingGenerator
Advanced tools
MappingGenerator was initially created as a design-time alternative to AutoMapper. Now it is evolving into a coding assistant to whom you can delegate the most mundane coding tasks.
⭐ Generating mapping method implementation
⭐ Generating full mapper class
⭐ Generating mapping lambda for Select method
⭐ Cleaning up method invocation (reformating, auto-extracting complex parameters, etc)
⭐ Method invocation scaffolding
⭐ Object initialization scaffolding
⭐ Smart snippets for ILogger usages
⭐ Design-time JSON deserializer
Scroll down or check the documentation to find out more.
Product page: https://www.mappinggenerator.net
Features overview: Documentation
Release notes and previous versions: Changelog
Bugs and Feature Requests: Issue Tracker
Check out the Special Offers to save some 💲💲💲
Code action that generates an implementation for different mapping methods based on the method signature:
Code action that automatically completes method invocation with locally available variables
Code action that automatically completes object initialization block with locally available variables:
Code action that generates mapping lambda for Select() and ConvertAll() methods
Full access to UI configurator that allows adjusting different aspects of how the mapping code is generated (in the free version you can try it how it works in read-only mode).
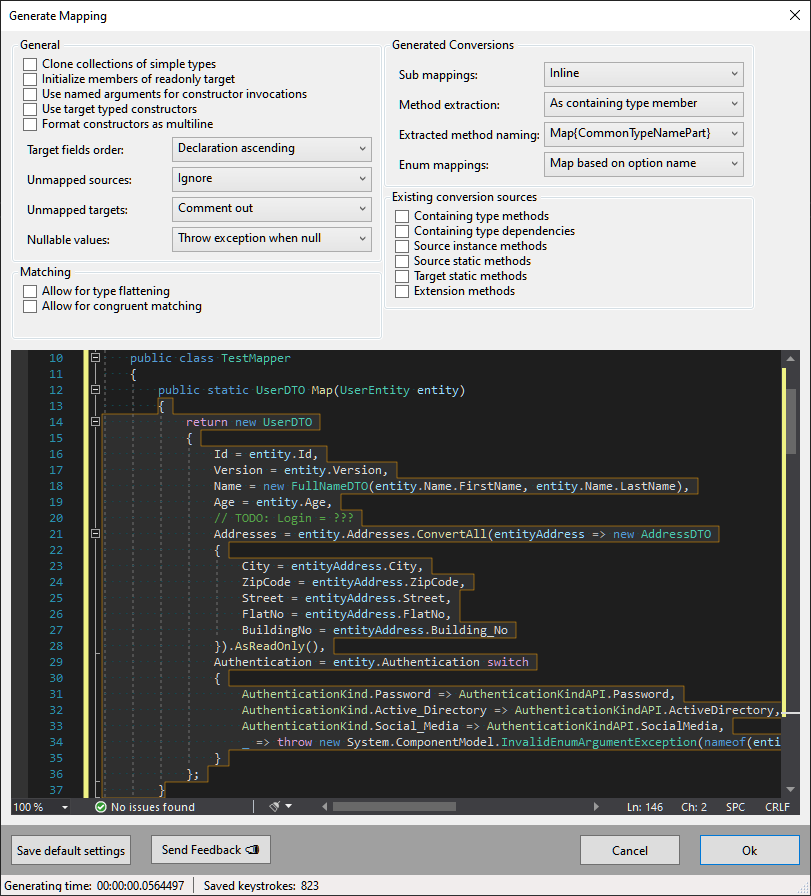
Read more about the UI Configurator possibilities here https://docs.mappinggenerator.net/mappings/ui-configurator/
Premium version contains a much broader set of converters and matching rules that are able to handle more complex mappings:
Code action that generates mapper implementation based on the provided interface:
MappingGenerator provides code actions for generating a complete mapper class with desired mapping methods:
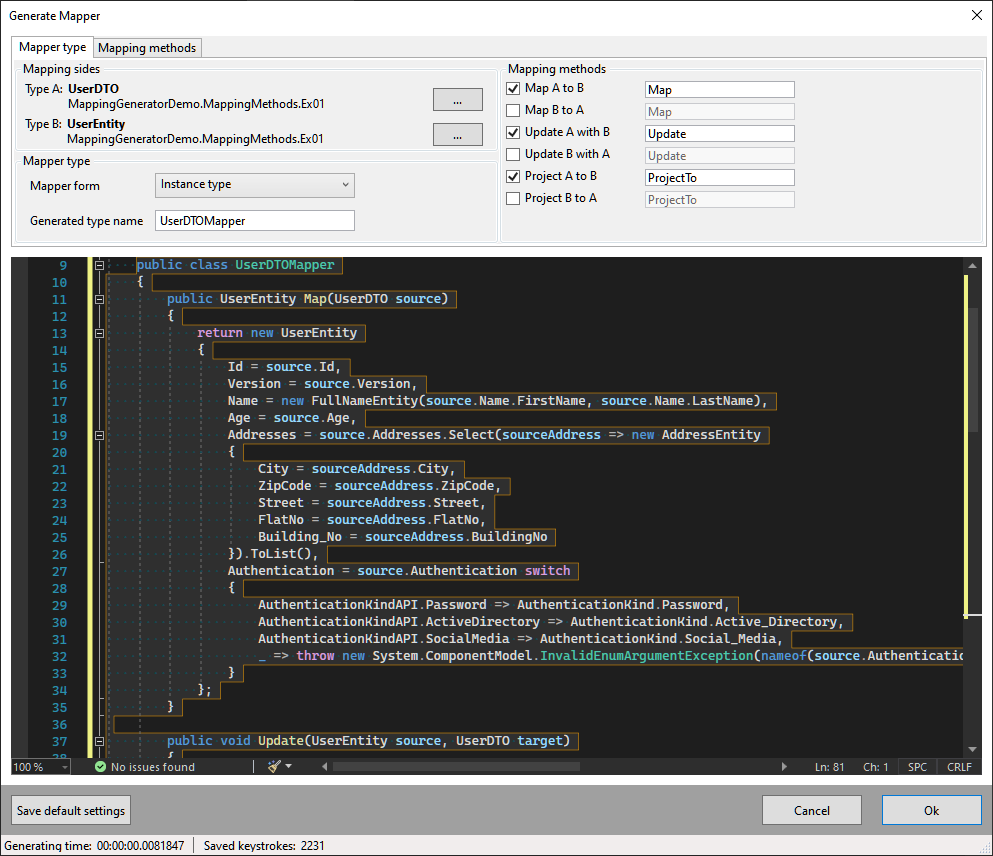
This code action allows for:
Have you ever been struggling with completing a method's long parameter list? What do you feel when you've got lost in the middle because there are a few similar overloads? This premium feature allows for quick scaffolding of complete method invocation.
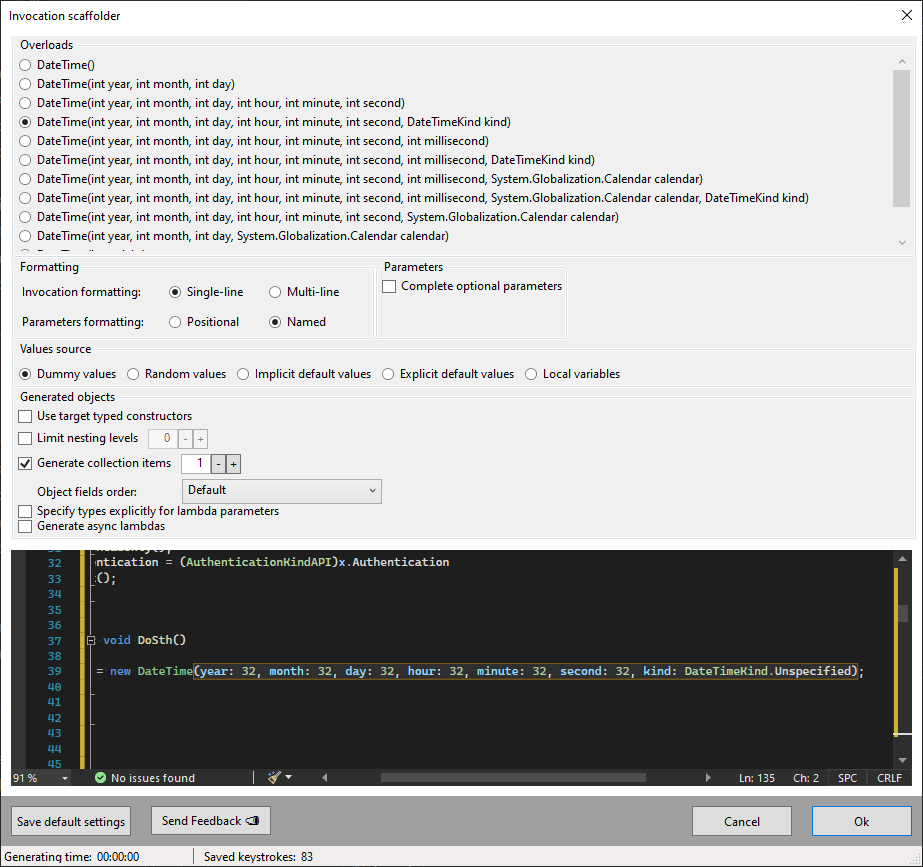
This module allows for the customization of how the object initialization is scaffolded:
new Type() and new() object creation syntax.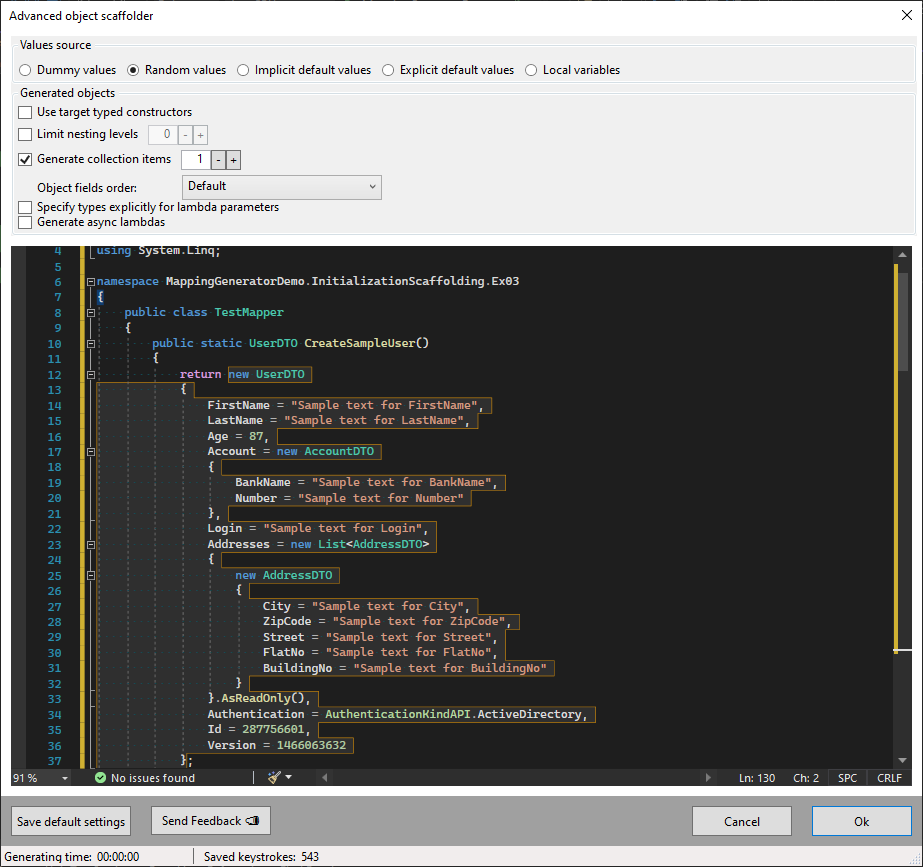
A set of scaffoldings that facilitate the usage of Microsoft.Extensions.Logging.ILogger:
try-catch, inject logger if needed, and log the exceptionAutomatically inject strongly typed logger and log info about the caught exception. Learn more about this feature here
If you are not able to access MappingGenerator via the context menu (alt + enter or ctr + . ) please verify your Resharper settings related to Visual Studio Integration or Visual Studio code analysis (depends on the R# version). You can read more about proper Resharper configuration for Roslyn extensions here https://docs.mappinggenerator.net/basics/using-with-resharper/
FAQs
MappingGenerator was initially created as a design-time alternative to AutoMapper. Now it is evolving into a coding assistant to whom you can delegate the most mundane coding tasks.
We found that mappinggenerator demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Axios compromise shows how time-dependent dependency resolution makes exposure harder to detect and contain.

Research
A supply chain attack on Axios introduced a malicious dependency, plain-crypto-js@4.2.1, published minutes earlier and absent from the project’s GitHub releases.

Research
Malicious versions of the Telnyx Python SDK on PyPI delivered credential-stealing malware via a multi-stage supply chain attack.