
Research
/Security News
Toptal’s GitHub Organization Hijacked: 10 Malicious Packages Published
Threat actors hijacked Toptal’s GitHub org, publishing npm packages with malicious payloads that steal tokens and attempt to wipe victim systems.
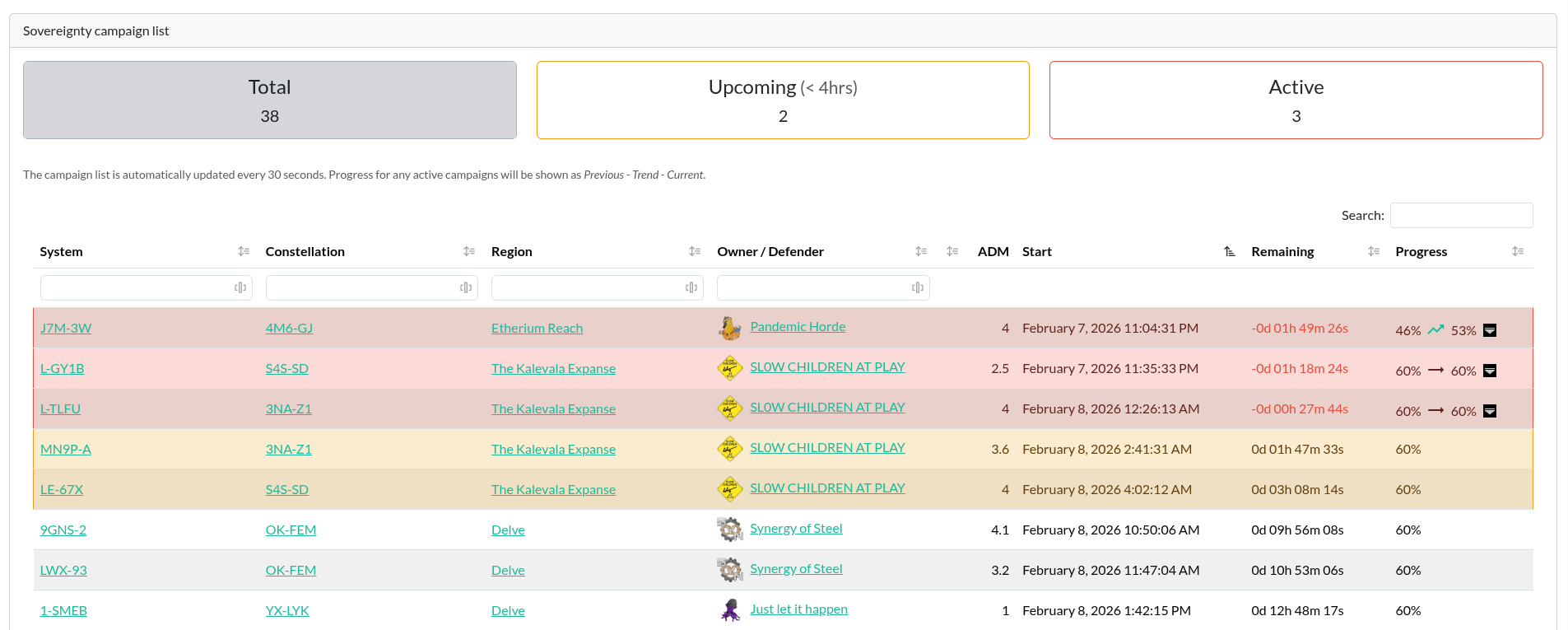
Sovereignty campaign overview for Alliance Auth.
[!IMPORTANT]
Please make sure you meet all preconditions before you proceed.
Make sure you're in the virtual environment (venv) of your Alliance Auth installation. Then install the latest version:
pip install aa-sov-timer
Configure your AA settings (local.py) as follows:
'eveuniverse', to INSTALLED_APPS if not already done for another app'sovtimer', to INSTALLED_APPSRestart your supervisor
Copy static files and run migrations
python manage.py collectstatic
python manage.py migrate
AA Sovereignty Timer uses Eve Universe data to map IDs to names for solar systems, regions and constellations. So you need to preload some data from ESI once. If you already have run this command, you can skip this step.
python manage.py eveuniverse_load_data map
python manage.py sovtimer_load_initial_data
Both commands might take a moment or two, so be patient ...
Now you can set up permissions in Alliance Auth for your users.
Add sovtimer | Sovereignty Timer | Can access the Sovereignty Timer module to
the states and/or groups you would like to have access.
Add the following scheduled task to your local.py. One done, restart your supervisor.
# AA Sovereignty Timer - Run sovereignty related updates every 30 seconds
CELERYBEAT_SCHEDULE["sovtimer.tasks.run_sov_campaign_updates"] = {
"task": "sovtimer.tasks.run_sov_campaign_updates",
"schedule": 30.0,
}
Now your system is updating the sovereignty campaigns every 30 seconds.
Add the app to your conf/requirements.txt:
aa-sov-timer==2.5.0
Configure your AA settings (conf/local.py) as follows:
'eveuniverse', to INSTALLED_APPS if not already done for another app'sovtimer', to INSTALLED_APPS# AA Sovereignty Timer - Run sovereignty related updates every 30 seconds
CELERYBEAT_SCHEDULE["sovtimer.tasks.run_sov_campaign_updates"] = {
"task": "sovtimer.tasks.run_sov_campaign_updates",
"schedule": 30.0,
}
docker compose build --no-cache
docker compose --env-file=.env up -d
Run migrations, copy static files and load EVE universe data:
docker compose exec allianceauth_gunicorn bash
auth collectstatic
auth migrate
auth eveuniverse_load_data map
auth sovtimer_load_initial_data
To update your existing installation of AA Sovereignty Timer, first enable your virtual environment.
Then run the following commands from your AA project directory (the one that
contains manage.py).
pip install -U aa-sov-timer
python manage.py collectstatic
python manage.py migrate
Finally, restart your AA supervisor service.
To update your existing installation of AA Sovereignty Timer, all you need to do is to update the respective line in your conf/requirements.txt file to the latest version.
aa-sov-timer==2.5.0
Now rebuild your containers and restart them:
docker compose build --no-cache
docker compose --env-file=.env up -d
After that, run the following commands to update your database and static files:
docker compose exec allianceauth_gunicorn bash
auth collectstatic
auth migrate
It is possible that some versions need some more changes. Always read the release notes to find out more.
See CHANGELOG.md
Do you want to help translate this app into your language or improve the existing translation? - Join our team of translators!
Do you want to contribute to this project? That's cool!
Please make sure to read the Contribution Guidelines.
(I promise, it's not much, just some basics)
FAQs
Sov Campaign Timer for Alliance Auth
We found that aa-sov-timer demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Research
/Security News
Threat actors hijacked Toptal’s GitHub org, publishing npm packages with malicious payloads that steal tokens and attempt to wipe victim systems.

Research
/Security News
Socket researchers investigate 4 malicious npm and PyPI packages with 56,000+ downloads that install surveillance malware.

Security News
The ongoing npm phishing campaign escalates as attackers hijack the popular 'is' package, embedding malware in multiple versions.