
Research
2025 Report: Destructive Malware in Open Source Packages
Destructive malware is rising across open source registries, using delays and kill switches to wipe code, break builds, and disrupt CI/CD.
alkh
Advanced tools


pip install alkh
function name: take_it_offline
description: create jupyter notebook based on the program stack
parameters:
notebook_dir_path: Optional[str] = None, directory path to save the notebook in
levels: Optional[int] = 1, number of program stack layers to put in notebook
import alkh
alkh.take_it_offline('path-of-notebooks-directory')
or
alkh.take_it_offline('path-of-notebooks-directory', levels=2)
or
bash:
export ALKH_NOTEBOOKS_PATH='path-to-notebooks-directory'
python:
import alkh
alkh.take_it_offline()
or
alkh.take_it_offline(levels=2)
Stop at breakpoint within PyCharm

Use Console to run code within debugger
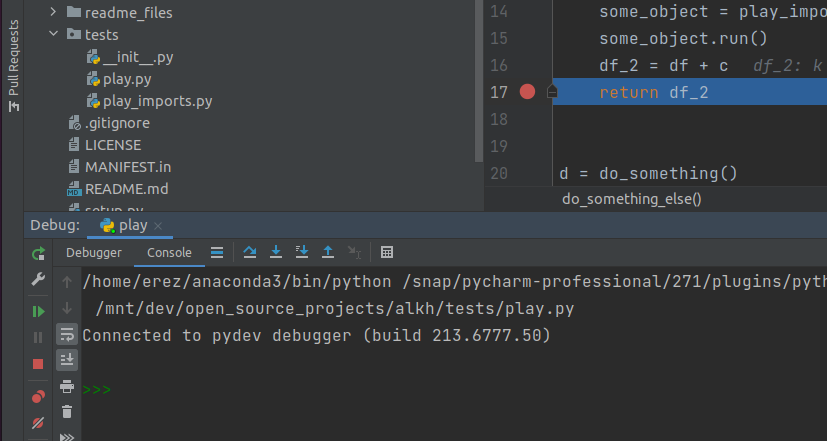
Run: import alkh

Run: alkh.take_it_offline('path-of-notebooks-directory')

Start Jupyter
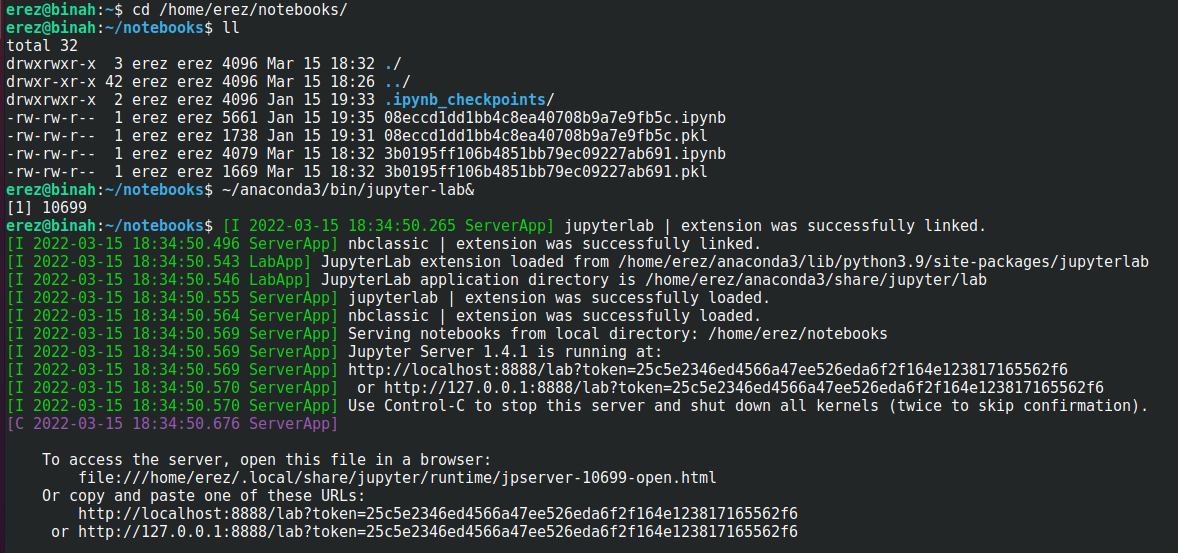
Run the notebook

function name: analyze
description: launches web application to analyze code pathways
parameters:None
import alkh
alkh.analyze()
Add two line to top of file

Run the file

Analyze your code

FAQs
algorithmic python debugging
We found that alkh demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Research
Destructive malware is rising across open source registries, using delays and kill switches to wipe code, break builds, and disrupt CI/CD.

Security News
Socket CTO Ahmad Nassri shares practical AI coding techniques, tools, and team workflows, plus what still feels noisy and why shipping remains human-led.

Research
/Security News
A five-month operation turned 27 npm packages into durable hosting for browser-run lures that mimic document-sharing portals and Microsoft sign-in, targeting 25 organizations across manufacturing, industrial automation, plastics, and healthcare for credential theft.