
Security Fundamentals
Turtles, Clams, and Cyber Threat Actors: Shell Usage
The Socket Threat Research Team uncovers how threat actors weaponize shell techniques across npm, PyPI, and Go ecosystems to maintain persistence and exfiltrate data.

Blurr transforms structured, streaming raw data into features for model training and prediction using a high-level expressive YAML-based language called the Blurr Transform Spec (BTS). The BTS merges the schema and computation model for data processing.
The BTS is a data transform definition for structured data. The BTS encapsulates the business logic of data transforms and Blurr orchestrates the execution of data transforms. Blurr is runner-agnostic, so BTSs can be run by event processors such as Spark, Spark Streaming or Flink.
Yes, if: you are well on your way on the ML 'curve of enlightenment', and are thinking about how to do online scoring

Coming up with features is difficult, time-consuming, requires expert knowledge. 'Applied machine learning' is basically feature engineering --- Andrew Ng
Streaming BTS Tutorial | Window BTS Tutorial
Preparing data for specific use cases using Blurr:
Welcome to the Blurr community! We are so glad that you share our passion for building MLOps!
Please create a new issue to begin a discussion. Alternatively, feel free to pick up an existing issue!
Please sign the Contributor License Agreement before raising a pull request.
Inspired by the (old school) Joel Test to rate software teams, here's our version for data science teams. What's your score?
Blurr is currently in Developer Preview. Stay in touch!: Star this project or email hello@blurr.ai
FAQs
Data aggregation pipeline for running real-time predictive models
We found that blurr demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

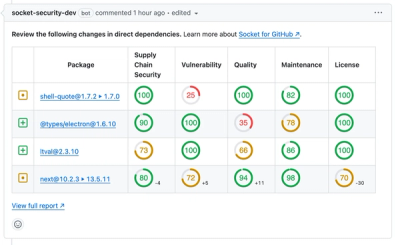
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security Fundamentals
The Socket Threat Research Team uncovers how threat actors weaponize shell techniques across npm, PyPI, and Go ecosystems to maintain persistence and exfiltrate data.

Security News
At VulnCon 2025, NIST scrapped its NVD consortium plans, admitted it can't keep up with CVEs, and outlined automation efforts amid a mounting backlog.
Product
We redesigned our GitHub PR comments to deliver clear, actionable security insights without adding noise to your workflow.