
Product
Introducing Reachability for PHP
Reachability analysis for PHP is now available in experimental, helping teams identify which vulnerabilities are actually exploitable.
pet-debian
Advanced tools
PET is a collection of scripts that gather information about your (or your group's) packages. It allows you to see in a bird's eye view the health of hundreds of packages, instantly realizing where work is needed.
The code is at https://anonscm.debian.org/cgit/pet/pet3.git/, database dumps can be found at http://pet.43-1.org/~pet/db/.
Discussions go on the pet-devel mailing list.
There are two ways to install Pet. With or without vagrant. Choose one and follow the next steps to install.
Vagrant is a tool for building complete development environments. With an easy-to-use workflow and focus on automation, Vagrant lowers development environment setup time, increases development/production parity, and makes the "works on my machine" excuse a relic of the past. Official Site Reference.
Vagrant can be installed with the command: apt-get install vagrant. And all the binaries are in this page Vagrant Download.
To install PET, it is necessary to clone the repository and start vagrant:
$ git clone https://anonscm.debian.org/cgit/pet/pet3.git/
$ cd pet/
Now, it is necessary to start vagrant up and access vagrants ssh. Follow this commands:
$ vagrant up
$ vagrant ssh
$ sudo su - pet
To start the web interface, execute:
$ ./pet-serve
To access it: http://localhost:4567/pkg-perl/pet.cgi
Install this softwares according to your operation system:
As root (waiting for python-pyramid-chameleon package, https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=785048):
$ pip install pyramid_chameleon
As root (more precise: as a postgres superuser):
$ su postgres
$ createuser pet
Shall the new role be a superuser? (y/n) n
Shall the new role be allowed to create databases? (y/n) y
Shall the new role be allowed to create more new roles? (y/n) n
$ createdb -O pet pet
$ psql pet < /usr/share/postgresql/9.4/contrib/debversion.sql
As the created user:
$ ./pet-update -c
$ psql pet
pet=> INSERT INTO team (name, maintainer, url) VALUES ('pkg-perl', 'Debian Perl Group <pkg-perl-maintainers@lists.alioth.debian.org>', 'http://pkg-perl.alioth.debian.org/');
pet=> INSERT INTO repository (name, type, root, web_root, team_id) VALUES ('git','git','https://pet.alioth.debian.org/pet2-data/pkg-perl/git-pkg-perl-packages.json','http://anonscm.debian.org/gitweb/?p=pkg-perl/packages', 1);
pet=> INSERT INTO package (name, repository_id) VALUES ('clive', 1);
pet=> INSERT INTO archive (name, url, web_root) VALUES ('debian', 'http://cdn.debian.net/debian', 'http://packages.qa.debian.org/');
pet=> INSERT INTO suite (archive_id, name) VALUES (1, 'unstable');
pet=> \q
$ ./update-package libboolean-perl
$ ./update-bts
$ ./update-archive debian
To start the web interface:
$ ./pet-serve
To access it: http://localhost:8080/pkg-perl/pet.cgi
To get the packages, it is necessary to update your local repository.
$ update-repository x
x is a positive integer of the repository. e.g. pass 1. This command will return all packages.
Now, update the packages with the names printed on $ update-repository x. Follow this command:
$ update-package packages_name
After updating all packages, run:
$ ./update-bts
FAQs
PET is a collection of scripts that gather informatio about your packages
We found that pet-debian demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Reachability analysis for PHP is now available in experimental, helping teams identify which vulnerabilities are actually exploitable.

Product
Export Socket alert data to your own cloud storage in JSON, CSV, or Parquet, with flexible snapshot or incremental delivery.
Research
/Security News
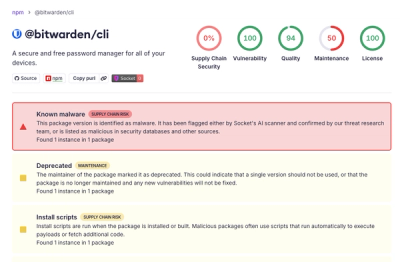
Bitwarden CLI 2026.4.0 was compromised in the Checkmarx supply chain campaign after attackers abused a GitHub Action in Bitwarden’s CI/CD pipeline.