Product
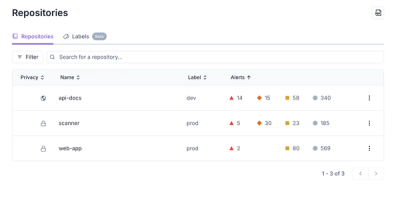
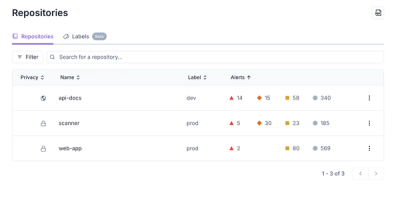
Redesigned Repositories Page: A Faster Way to Prioritize Security Risk
Our redesigned Repositories page adds alert severity, filtering, and tabs for faster triage and clearer insights across all your projects.
A JSON5 serializer and parser library for Python 3 written in
Cython <http://cython.org/>_.
The serializer returns ASCII data that can safely be used in an HTML template. Apostrophes, ampersands, greater-than, and less-then signs are encoded as unicode escaped sequences. E.g. this snippet is safe for any and all input:
.. code:: html
"<a onclick='alert(" + encode(data) + ")'>show message</a>"
Unless the input contains infinite or NaN values, the result will be valid
JSON <https://tools.ietf.org/html/rfc8259>_ data.
All valid JSON5 1.0.0 <https://spec.json5.org/>_ and
JSON <https://tools.ietf.org/html/rfc8259>_ data can be read,
unless the nesting level is absurdly high.
You can find the full documentation online at https://pyjson5.readthedocs.io/en/latest/.
Or simply call help(pyjson5). :-)
The library supplies load(s) and dump(s) functions, so you can use it as a
drop-in replacement for Python's builtin json module, but you should
use the functions encode_*() and decode_*() instead.
At least CPython 3.7 or a recent Pypy3 version is needed.
FAQs
JSON5 serializer and parser for Python 3 written in Cython.
We found that pyjson5 demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Our redesigned Repositories page adds alert severity, filtering, and tabs for faster triage and clearer insights across all your projects.

Security News
Multiple deserialization flaws in PyTorch Lightning could allow remote code execution when loading untrusted model files, affecting versions up to 2.4.0.
Security News
NVD now marks all pre-2018 CVEs as "Deferred," signaling it will no longer enrich older vulnerabilities, further eroding trust in its data.