Product
Announcing Precomputed Reachability Analysis in Socket
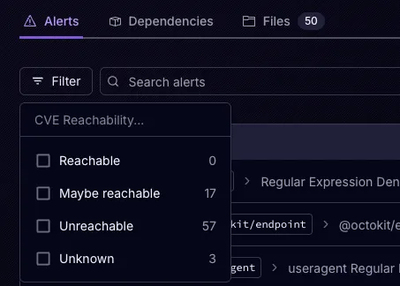
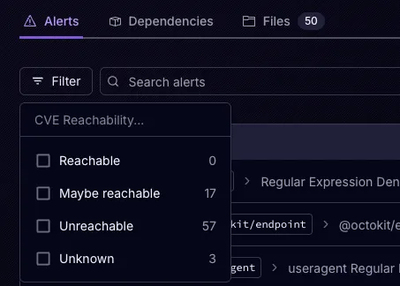
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.
Command line tool and library wrappers around iwlist and /etc/network/interfaces.
Wifi provides a command line wrapper for iwlist and /etc/network/interfaces that makes it easier to connect the WiFi networks from the command line. The wifi command is also implemented as a library that can be used from Python.
This fork takes care of the "ap-force" option when running iw. Also, the binary is not /sbin/iwlist anymore, but iw directly (/usr/sbin/iw), therefore the command is a bit different.
It's a drop-in replacement of the original package.
pip install wifi-ap-force
wifi --help
The original documentation for wifi lives at https://wifi.readthedocs.org/en/latest/.
FAQs
Command line tool and library wrappers around iwlist and /etc/network/interfaces.
We found that wifi-ap-force demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.

Product
Socket is launching experimental protection for Chrome extensions, scanning for malware and risky permissions to prevent silent supply chain attacks.

Product
Add secure dependency scanning to Claude Desktop with Socket MCP, a one-click extension that keeps your coding conversations safe from malicious packages.