
Security News
Follow-up and Clarification on Recent Malicious Ruby Gems Campaign
A clarification on our recent research investigating 60 malicious Ruby gems.
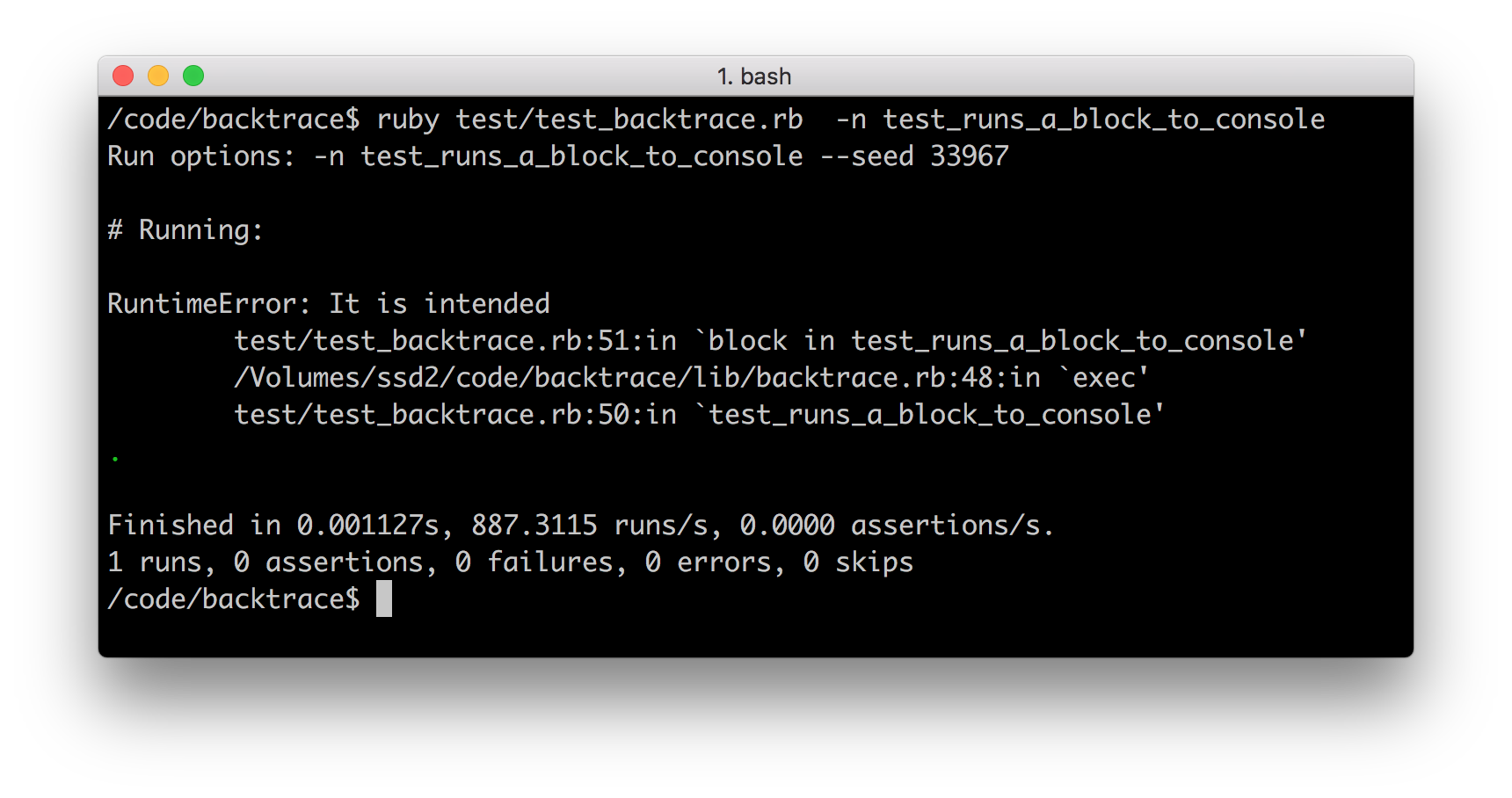
A Ruby backtrace nicely printed.
First, install it:
gem install backtrace
Then, use it like this to print a backtrace:
require 'backtrace'
begin
# do something dangerous
rescue StandardError => e
puts Backtrace.new(e)
end
A more compact version would use a block:
require 'backtrace'
Backtrace.exec(swallow: true) do
# do something dangerous
end
You can also provide a logging facility to log the backtrace:
require 'backtrace'
log = Log.new # it must implement the method error(msg)
Backtrace.exec(swallow: true, log: log) do
# do something dangerous
end
Sometimes you may need to hide unimportant lines of the backtrace
that are not related to your codebase. You can use the mine argument
of the constructor, which is a regular expression or a string. When it's encountered
in the backtrace, the printing will stop:
require 'backtrace'
begin
# do something dangerous
rescue StandardError => e
puts Backtrace.new(e, mine: 'yegor')
end
That's it.
Read these guidelines. Make sure your build is green before you contribute your pull request. You will need to have Ruby 2.3+ and Bundler installed. Then:
bundle update
bundle exec rake
If it's clean and you don't see any error messages, submit your pull request.
FAQs
Unknown package
We found that backtrace demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
A clarification on our recent research investigating 60 malicious Ruby gems.

Security News
ESLint now supports parallel linting with a new --concurrency flag, delivering major speed gains and closing a 10-year-old feature request.

Research
/Security News
A malicious Go module posing as an SSH brute forcer exfiltrates stolen credentials to a Telegram bot controlled by a Russian-speaking threat actor.