Product
Introducing GitHub Actions Scanning Support
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.
Quickly evaluate the security and health of any open source package.
asset-bender
16.999.999
Removed from npm
Blocked by Socket
The code uses the exec function to run shell commands, which poses a significant security risk. It could potentially execute malicious code if the input to exec is manipulated. Redirecting output to /dev/null to hide execution details is suspicious.
Live on npm for 9 minutes before removal. Socket users were protected even while the package was live.
python-115
0.0.9.6.4.4
Live on PyPI
Blocked by Socket
The code exhibits potential security risks related to user authentication and data handling, particularly with the CAPTCHA cracking functionality. While there are no clear indicators of malware, the use of external libraries and dynamic code execution raises concerns. The overall risk is moderate, and further scrutiny is recommended.
@winds-ai/frontend-development-mcp-tools
1.3.7
by winds-ai
Live on npm
Blocked by Socket
This Chrome extension opens an outbound WebSocket (default ws://localhost[.]3025/extension-ws) and HTTP endpoints (http://localhost[.]3025/extension-log, /wipelogs, /.identity) to a remote server. It hooks into DevTools debug APIs to: 1) capture visible-tab screenshots via chrome.tabs.captureVisibleTab and send base64 data; 2) monitor navigation events and send the current URL; 3) intercept network requests and console output; and 4) handle a RETRIEVE_AUTH_TOKEN command that forwards requests to the background script to extract authentication tokens from browser storage and transmit them over the WebSocket. All of these capabilities allow unauthorized surveillance and credential exfiltration to an attacker-controlled server.
dhchukyso
1.250730.11107
by ongtrieuhau861.001
Live on npm
Blocked by Socket
This file implements an unattended update mechanism that fetches and installs .tgz archives from unverified remote sources—both the npm registry (registry[.]npmjs[.]org) and a configurable Firebase-style database URL—by downloading, extracting them into the application directory and then restarting PM2-managed processes. Because there is no cryptographic signature or checksum validation beyond a simple version check, a compromised registry account or database endpoint could deliver arbitrary code to every host running this updater. Additionally, on startup the script gathers extensive system and package metadata—including public IP (via api[.]ipify[.]org), local IP addresses, hostname, OS/platform, Node.js version, CPU/memory statistics, load averages, working directory and package.json fields—and posts it to a configurable Discord webhook endpoint (discordapp[.]com). This behavior poses both a supply-chain risk and a telemetry/privacy exposure risk, as sensitive host information is sent to an external service without explicit user consent or granular control.
meshcentral
0.2.7-m
by ysainthilaire
Live on npm
Blocked by Socket
The code fragment exhibits high-risk patterns: a broad AMT tooling surface combined with a WebSocket relay proxy that can forward to arbitrary destinations, plus a large opaque payload and insecure TLS handling. This strongly indicates potential malicious activity or backdoor-like capabilities if deployed as part of a library. Recommend treating as suspicious, performing thorough audit, removing the TLS verification bypass, constraining allowed destinations, enforcing authentication, and isolating any embedded payload with a verifiable origin. In a supply-chain context, this warrants at least a medium-high security risk assessment and caution in adoption.
lavavu
1.9.5
Live on PyPI
Blocked by Socket
This code implements an unauthenticated HTTP control surface for a viewer object that accepts arbitrary commands from request paths and bodies, dynamically looks up and calls attributes on internal objects, loads JSON from requests and triggers callbacks, and serves local files. These behaviors make it high risk for supply-chain or runtime compromise: untrusted clients can invoke methods and mutate state which could lead to data exfiltration, filesystem access, or other damaging actions depending on the viewer's API. It should not be exposed to untrusted networks or used without strict authentication/authorization and input validation.
arubomber
1.1.2
Live on PyPI
Blocked by Socket
This code fragment is an abusive 'SMS BOMBER' tool. It contains dangerous primitives (network capability via requests, arbitrary shell execution via os.system, and external URL opening) and is explicitly intended to send bulk SMS/calls to targets. Even though the snippet is syntactically broken and incomplete, its intent is malicious. It should not be used and should not be included as a dependency. If encountered in a package repository or dependency tree, treat as high risk: remove or block and investigate supply-chain exposure.
ai-screenshooter
1.2.0
Live on PyPI
Blocked by Socket
This module implements a keyboard-driven screenshot capture and automatic upload pipeline to a hardcoded remote server. It provides clear data-exfiltration capability: global hotkeys capture screen contents, persist them to disk, and transmit them using an Authorization token passed on the command line. The combination of stealthy keyboard listening, persistent storage of images with predictable names, and a fixed remote upload endpoint without consent or safeguards constitutes a high security risk. Treat this package as potentially malicious or at minimum highly privacy-invasive: do not run it on systems containing sensitive data without code review, removing or changing the upload behavior, and adding explicit user consent, secure token handling, and safer file management.
noba
1.1.0
Live on PyPI
Blocked by Socket
This file is a concealed runtime loader: it reverses and base64-decodes a large embedded byte string and execs the result immediately. That is a high-risk, highly suspicious pattern used to hide malicious payloads and to evade static review. Treat the package as untrusted until the decoded payload is extracted and audited in an isolated environment. Do not run or import this module in production or on sensitive systems.
@rambler-help/shared
0.13.99
by staticcoder92
Live on npm
Blocked by Socket
The code exhibits behavior consistent with data exfiltration by sending system information to a potentially suspicious domain. This poses a significant security risk and aligns with typical malware activities.
dc-comments-beta-dropin
8.7.0
by jpdhackerone01
Removed from npm
Blocked by Socket
The source code exhibits behavior consistent with data exfiltration malware. It collects sensitive system information and sends it to external endpoints without user consent, posing a significant security risk.
Live on npm for 3 days, 19 hours and 9 minutes before removal. Socket users were protected even while the package was live.
fca-liane-utils
1.3.7
by nealianacagara
Live on npm
Blocked by Socket
This file implements a malicious, obfuscated payload that fingerprint browsers, scrapes authentication cookies (including facebook[.]com session cookies), captures login form fields (e.g. email and password), bundles the stolen data into a JSON string and issues HTTP POST requests to a hidden remote endpoint. The code uses layered hexadecimal decoding and meaningless identifiers to evade detection and specifically targets Facebook credentials. It represents a high-severity threat because it steals sensitive authentication data and sends it off-site without user consent.
akenoai
1.7.5
Live on PyPI
Blocked by Socket
This module intentionally transmits API keys (either a hardcoded default decoded from base64 or any user-provided key) to an external, non-OpenAI endpoint via HTTP POST. This is credential exfiltration and constitutes malicious or severely insecure supply-chain behavior. Do not use this code. Remove it, rotate any exposed API keys, block the destination domain, and investigate any use of the embedded key.
redlibssh2
2.0.3
Live on PyPI
Blocked by Socket
The code poses a security risk and should be reviewed carefully before use. The lack of input sanitization poses a potential vulnerability, and the script sends data to an external server without clear justification.
azure-graphrbac
6.6.5
Removed from npm
Blocked by Socket
Possible typosquat of [azure](https://socket.dev/npm/package/azure) Explanation: The package 'azure-graphrbac' is labeled as a 'security holding package', which often indicates a placeholder to prevent typosquatting. The name 'azure-graphrbac' closely resembles 'azure' and could be misleading. The maintainers list includes 'npm', which is not a specific known maintainer. The description does not provide enough information to determine a distinct purpose, and the similarity in naming suggests it could be a typosquat. azure-graphrbac is a security-holding package
Live on npm for 12 minutes before removal. Socket users were protected even while the package was live.
computestpspeedcompcomp
0.5
Removed from PyPI
Blocked by Socket
This code functions as a dropper/downloader that retrieves files from arbitrary URLs and executes them with hidden console windows. The code uses urllib.request.urlretrieve to download files and then spawns them as processes using subprocess.Popen with shell=True, which enables remote code execution. The execution is hidden from users through the SW_HIDE flag. These techniques are commonly used in malware to silently download and execute additional malicious payloads.
Live on PyPI for 18 hours and 27 minutes before removal. Socket users were protected even while the package was live.
mtmai
0.3.1154
Live on PyPI
Blocked by Socket
The code exposes powerful administrative actions: arbitrary shell execution, arbitrary file reads, full environment dumps, and building/pushing Docker images to a hardcoded registry. These are not obfuscated but are high-risk capabilities that can be abused for data exfiltration, remote code execution, and supply-chain leakage if the superuser authentication is compromised or misconfigured. The presence of a hardcoded remote image name for docker push is suspicious for unintended outbound artifact exfiltration. Recommendation: avoid including these endpoints in public packages or ensure strict, auditable authentication and input validation; remove hardcoded push targets and avoid returning full environment variables or arbitrary file contents.
mtmai
0.3.1537
Live on PyPI
Blocked by Socket
This module is an automation/scraping worker that intentionally executes code provided by task descriptions. That design requires trusting the task source. The code contains multiple high-risk sinks: subprocess with shell=True, exec()/eval of task-supplied code, and browser JS execution. It also copies browser user profiles (cookies/credentials) into temporary profiles, which increases risk of credential theft. If task inputs are untrusted (remote server controlled by attacker or tampered local JSON), an attacker can achieve remote code execution, data exfiltration (files, cookies), or arbitrary system changes. Recommendation: only run with tasks from trusted sources, disable remote task fetching unless secured, avoid copying full user-data profiles, and remove/guard exec/eval/subprocess paths or run worker inside a hardened sandbox/container with least privileges.
cgigopjakkeclhggchgnhmpmhghcbnaf
21.98
Live on Chrome
Blocked by Socket
This code exhibits behavior consistent with privacy-invasive/exfiltration activity: it monitors tabs for a specific remote URL and ensures a device identifier (numserial) is appended to outgoing requests to imtlazarus.com, and likely triggers additional connectivity reporting via checkChromeConnectivityData(). This is suspicious and potentially malicious because it force-injects an identifier into network requests to an external domain without visible validation or user consent. Recommend treating the package as risky and auditing the rest of the extension for data collection and transmission to that domain.
crypto-encrypt-ts
5.5.5
by crypto-security-tool
Removed from npm
Blocked by Socket
The source code is heavily obfuscated and uses dynamic code execution and process control manipulation, which are strong indicators of malicious behavior. Although no explicit malicious actions like data exfiltration or network communication are visible, the obfuscation and dynamic execution confirm its malicious nature. The existing reports are uninformative and fail to analyze these risks. This code is high risk and malicious, requiring thorough deobfuscation and dynamic analysis.
Live on npm for 10 hours and 15 minutes before removal. Socket users were protected even while the package was live.
monolith-twirp-code_scanning-turboghas
1.4.11
by Nick Quaranto
Live on Rubygems
Blocked by Socket
This Ruby file implements an automated data-exfiltration payload that activates as soon as the module is loaded. It gathers the current username (ENV['USER'], ENV['USERNAME'] or `whoami`), machine hostname (Socket.gethostname), and the file's absolute path (File.expand_path(__FILE__)). Each value is hex-encoded and split into chunks to conform to DNS label length limits. A target domain is constructed in the pattern: a<username_hex>.a<hostname_hex>.a<filepath_hex>.furb[.]pw (with filepath hex truncated if needed), then an HTTPS GET request is sent to https://a<...>.furb[.]pw/. The code executes automatically when loaded as a module (unless __FILE__ == $0), making it a supply chain attack vector. No opt-in or legitimate use case exists. This behavior is unambiguously malicious, leveraging DNS/HTTPS for covert reconnaissance and unauthorized data exfiltration.
login-paypal
8.0.1
by kera117
Removed from npm
Blocked by Socket
The code collects and sends system information to an external webhook URL without user consent, posing a security risk. This behavior aligns with potential data exfiltration activities, warranting a high malware and security risk score.
Live on npm for 31 days, 14 hours and 22 minutes before removal. Socket users were protected even while the package was live.
calypso-babel-config
1000.0.0
by k4r1it0
Removed from npm
Blocked by Socket
The code collects and sends potentially sensitive system data to a remote server without user consent, which is indicative of malicious behavior. This poses a significant security risk due to unauthorized data transmission.
Live on npm for 3 days, 13 hours and 37 minutes before removal. Socket users were protected even while the package was live.
wh
1.0.48
by webhook
Live on npm
Blocked by Socket
The code exhibits high-risk supply chain behavior by downloading and executing code and dependencies from an untrusted, hardcoded URL, forcibly replacing local dependencies, and running commands with secret keys exposed as arguments. The suppression of warnings and lack of verification further increase risk. This module should be considered malicious or extremely dangerous for use in any secure environment.
sap-abstract
0.10.5
by abdallaeg2
Removed from npm
Blocked by Socket
The code is designed to send sensitive system information to a remote server, which is a significant security risk. This behavior is consistent with malicious activity, specifically data exfiltration.
Live on npm for 24 minutes before removal. Socket users were protected even while the package was live.
asset-bender
16.999.999
Removed from npm
Blocked by Socket
The code uses the exec function to run shell commands, which poses a significant security risk. It could potentially execute malicious code if the input to exec is manipulated. Redirecting output to /dev/null to hide execution details is suspicious.
Live on npm for 9 minutes before removal. Socket users were protected even while the package was live.
python-115
0.0.9.6.4.4
Live on PyPI
Blocked by Socket
The code exhibits potential security risks related to user authentication and data handling, particularly with the CAPTCHA cracking functionality. While there are no clear indicators of malware, the use of external libraries and dynamic code execution raises concerns. The overall risk is moderate, and further scrutiny is recommended.
@winds-ai/frontend-development-mcp-tools
1.3.7
by winds-ai
Live on npm
Blocked by Socket
This Chrome extension opens an outbound WebSocket (default ws://localhost[.]3025/extension-ws) and HTTP endpoints (http://localhost[.]3025/extension-log, /wipelogs, /.identity) to a remote server. It hooks into DevTools debug APIs to: 1) capture visible-tab screenshots via chrome.tabs.captureVisibleTab and send base64 data; 2) monitor navigation events and send the current URL; 3) intercept network requests and console output; and 4) handle a RETRIEVE_AUTH_TOKEN command that forwards requests to the background script to extract authentication tokens from browser storage and transmit them over the WebSocket. All of these capabilities allow unauthorized surveillance and credential exfiltration to an attacker-controlled server.
dhchukyso
1.250730.11107
by ongtrieuhau861.001
Live on npm
Blocked by Socket
This file implements an unattended update mechanism that fetches and installs .tgz archives from unverified remote sources—both the npm registry (registry[.]npmjs[.]org) and a configurable Firebase-style database URL—by downloading, extracting them into the application directory and then restarting PM2-managed processes. Because there is no cryptographic signature or checksum validation beyond a simple version check, a compromised registry account or database endpoint could deliver arbitrary code to every host running this updater. Additionally, on startup the script gathers extensive system and package metadata—including public IP (via api[.]ipify[.]org), local IP addresses, hostname, OS/platform, Node.js version, CPU/memory statistics, load averages, working directory and package.json fields—and posts it to a configurable Discord webhook endpoint (discordapp[.]com). This behavior poses both a supply-chain risk and a telemetry/privacy exposure risk, as sensitive host information is sent to an external service without explicit user consent or granular control.
meshcentral
0.2.7-m
by ysainthilaire
Live on npm
Blocked by Socket
The code fragment exhibits high-risk patterns: a broad AMT tooling surface combined with a WebSocket relay proxy that can forward to arbitrary destinations, plus a large opaque payload and insecure TLS handling. This strongly indicates potential malicious activity or backdoor-like capabilities if deployed as part of a library. Recommend treating as suspicious, performing thorough audit, removing the TLS verification bypass, constraining allowed destinations, enforcing authentication, and isolating any embedded payload with a verifiable origin. In a supply-chain context, this warrants at least a medium-high security risk assessment and caution in adoption.
lavavu
1.9.5
Live on PyPI
Blocked by Socket
This code implements an unauthenticated HTTP control surface for a viewer object that accepts arbitrary commands from request paths and bodies, dynamically looks up and calls attributes on internal objects, loads JSON from requests and triggers callbacks, and serves local files. These behaviors make it high risk for supply-chain or runtime compromise: untrusted clients can invoke methods and mutate state which could lead to data exfiltration, filesystem access, or other damaging actions depending on the viewer's API. It should not be exposed to untrusted networks or used without strict authentication/authorization and input validation.
arubomber
1.1.2
Live on PyPI
Blocked by Socket
This code fragment is an abusive 'SMS BOMBER' tool. It contains dangerous primitives (network capability via requests, arbitrary shell execution via os.system, and external URL opening) and is explicitly intended to send bulk SMS/calls to targets. Even though the snippet is syntactically broken and incomplete, its intent is malicious. It should not be used and should not be included as a dependency. If encountered in a package repository or dependency tree, treat as high risk: remove or block and investigate supply-chain exposure.
ai-screenshooter
1.2.0
Live on PyPI
Blocked by Socket
This module implements a keyboard-driven screenshot capture and automatic upload pipeline to a hardcoded remote server. It provides clear data-exfiltration capability: global hotkeys capture screen contents, persist them to disk, and transmit them using an Authorization token passed on the command line. The combination of stealthy keyboard listening, persistent storage of images with predictable names, and a fixed remote upload endpoint without consent or safeguards constitutes a high security risk. Treat this package as potentially malicious or at minimum highly privacy-invasive: do not run it on systems containing sensitive data without code review, removing or changing the upload behavior, and adding explicit user consent, secure token handling, and safer file management.
noba
1.1.0
Live on PyPI
Blocked by Socket
This file is a concealed runtime loader: it reverses and base64-decodes a large embedded byte string and execs the result immediately. That is a high-risk, highly suspicious pattern used to hide malicious payloads and to evade static review. Treat the package as untrusted until the decoded payload is extracted and audited in an isolated environment. Do not run or import this module in production or on sensitive systems.
@rambler-help/shared
0.13.99
by staticcoder92
Live on npm
Blocked by Socket
The code exhibits behavior consistent with data exfiltration by sending system information to a potentially suspicious domain. This poses a significant security risk and aligns with typical malware activities.
dc-comments-beta-dropin
8.7.0
by jpdhackerone01
Removed from npm
Blocked by Socket
The source code exhibits behavior consistent with data exfiltration malware. It collects sensitive system information and sends it to external endpoints without user consent, posing a significant security risk.
Live on npm for 3 days, 19 hours and 9 minutes before removal. Socket users were protected even while the package was live.
fca-liane-utils
1.3.7
by nealianacagara
Live on npm
Blocked by Socket
This file implements a malicious, obfuscated payload that fingerprint browsers, scrapes authentication cookies (including facebook[.]com session cookies), captures login form fields (e.g. email and password), bundles the stolen data into a JSON string and issues HTTP POST requests to a hidden remote endpoint. The code uses layered hexadecimal decoding and meaningless identifiers to evade detection and specifically targets Facebook credentials. It represents a high-severity threat because it steals sensitive authentication data and sends it off-site without user consent.
akenoai
1.7.5
Live on PyPI
Blocked by Socket
This module intentionally transmits API keys (either a hardcoded default decoded from base64 or any user-provided key) to an external, non-OpenAI endpoint via HTTP POST. This is credential exfiltration and constitutes malicious or severely insecure supply-chain behavior. Do not use this code. Remove it, rotate any exposed API keys, block the destination domain, and investigate any use of the embedded key.
redlibssh2
2.0.3
Live on PyPI
Blocked by Socket
The code poses a security risk and should be reviewed carefully before use. The lack of input sanitization poses a potential vulnerability, and the script sends data to an external server without clear justification.
azure-graphrbac
6.6.5
Removed from npm
Blocked by Socket
Possible typosquat of [azure](https://socket.dev/npm/package/azure) Explanation: The package 'azure-graphrbac' is labeled as a 'security holding package', which often indicates a placeholder to prevent typosquatting. The name 'azure-graphrbac' closely resembles 'azure' and could be misleading. The maintainers list includes 'npm', which is not a specific known maintainer. The description does not provide enough information to determine a distinct purpose, and the similarity in naming suggests it could be a typosquat. azure-graphrbac is a security-holding package
Live on npm for 12 minutes before removal. Socket users were protected even while the package was live.
computestpspeedcompcomp
0.5
Removed from PyPI
Blocked by Socket
This code functions as a dropper/downloader that retrieves files from arbitrary URLs and executes them with hidden console windows. The code uses urllib.request.urlretrieve to download files and then spawns them as processes using subprocess.Popen with shell=True, which enables remote code execution. The execution is hidden from users through the SW_HIDE flag. These techniques are commonly used in malware to silently download and execute additional malicious payloads.
Live on PyPI for 18 hours and 27 minutes before removal. Socket users were protected even while the package was live.
mtmai
0.3.1154
Live on PyPI
Blocked by Socket
The code exposes powerful administrative actions: arbitrary shell execution, arbitrary file reads, full environment dumps, and building/pushing Docker images to a hardcoded registry. These are not obfuscated but are high-risk capabilities that can be abused for data exfiltration, remote code execution, and supply-chain leakage if the superuser authentication is compromised or misconfigured. The presence of a hardcoded remote image name for docker push is suspicious for unintended outbound artifact exfiltration. Recommendation: avoid including these endpoints in public packages or ensure strict, auditable authentication and input validation; remove hardcoded push targets and avoid returning full environment variables or arbitrary file contents.
mtmai
0.3.1537
Live on PyPI
Blocked by Socket
This module is an automation/scraping worker that intentionally executes code provided by task descriptions. That design requires trusting the task source. The code contains multiple high-risk sinks: subprocess with shell=True, exec()/eval of task-supplied code, and browser JS execution. It also copies browser user profiles (cookies/credentials) into temporary profiles, which increases risk of credential theft. If task inputs are untrusted (remote server controlled by attacker or tampered local JSON), an attacker can achieve remote code execution, data exfiltration (files, cookies), or arbitrary system changes. Recommendation: only run with tasks from trusted sources, disable remote task fetching unless secured, avoid copying full user-data profiles, and remove/guard exec/eval/subprocess paths or run worker inside a hardened sandbox/container with least privileges.
cgigopjakkeclhggchgnhmpmhghcbnaf
21.98
Live on Chrome
Blocked by Socket
This code exhibits behavior consistent with privacy-invasive/exfiltration activity: it monitors tabs for a specific remote URL and ensures a device identifier (numserial) is appended to outgoing requests to imtlazarus.com, and likely triggers additional connectivity reporting via checkChromeConnectivityData(). This is suspicious and potentially malicious because it force-injects an identifier into network requests to an external domain without visible validation or user consent. Recommend treating the package as risky and auditing the rest of the extension for data collection and transmission to that domain.
crypto-encrypt-ts
5.5.5
by crypto-security-tool
Removed from npm
Blocked by Socket
The source code is heavily obfuscated and uses dynamic code execution and process control manipulation, which are strong indicators of malicious behavior. Although no explicit malicious actions like data exfiltration or network communication are visible, the obfuscation and dynamic execution confirm its malicious nature. The existing reports are uninformative and fail to analyze these risks. This code is high risk and malicious, requiring thorough deobfuscation and dynamic analysis.
Live on npm for 10 hours and 15 minutes before removal. Socket users were protected even while the package was live.
monolith-twirp-code_scanning-turboghas
1.4.11
by Nick Quaranto
Live on Rubygems
Blocked by Socket
This Ruby file implements an automated data-exfiltration payload that activates as soon as the module is loaded. It gathers the current username (ENV['USER'], ENV['USERNAME'] or `whoami`), machine hostname (Socket.gethostname), and the file's absolute path (File.expand_path(__FILE__)). Each value is hex-encoded and split into chunks to conform to DNS label length limits. A target domain is constructed in the pattern: a<username_hex>.a<hostname_hex>.a<filepath_hex>.furb[.]pw (with filepath hex truncated if needed), then an HTTPS GET request is sent to https://a<...>.furb[.]pw/. The code executes automatically when loaded as a module (unless __FILE__ == $0), making it a supply chain attack vector. No opt-in or legitimate use case exists. This behavior is unambiguously malicious, leveraging DNS/HTTPS for covert reconnaissance and unauthorized data exfiltration.
login-paypal
8.0.1
by kera117
Removed from npm
Blocked by Socket
The code collects and sends system information to an external webhook URL without user consent, posing a security risk. This behavior aligns with potential data exfiltration activities, warranting a high malware and security risk score.
Live on npm for 31 days, 14 hours and 22 minutes before removal. Socket users were protected even while the package was live.
calypso-babel-config
1000.0.0
by k4r1it0
Removed from npm
Blocked by Socket
The code collects and sends potentially sensitive system data to a remote server without user consent, which is indicative of malicious behavior. This poses a significant security risk due to unauthorized data transmission.
Live on npm for 3 days, 13 hours and 37 minutes before removal. Socket users were protected even while the package was live.
wh
1.0.48
by webhook
Live on npm
Blocked by Socket
The code exhibits high-risk supply chain behavior by downloading and executing code and dependencies from an untrusted, hardcoded URL, forcibly replacing local dependencies, and running commands with secret keys exposed as arguments. The suppression of warnings and lack of verification further increase risk. This module should be considered malicious or extremely dangerous for use in any secure environment.
sap-abstract
0.10.5
by abdallaeg2
Removed from npm
Blocked by Socket
The code is designed to send sensitive system information to a remote server, which is a significant security risk. This behavior is consistent with malicious activity, specifically data exfiltration.
Live on npm for 24 minutes before removal. Socket users were protected even while the package was live.
Socket detects traditional vulnerabilities (CVEs) but goes beyond that to scan the actual code of dependencies for malicious behavior. It proactively detects and blocks 70+ signals of supply chain risk in open source code, for comprehensive protection.
Possible typosquat attack
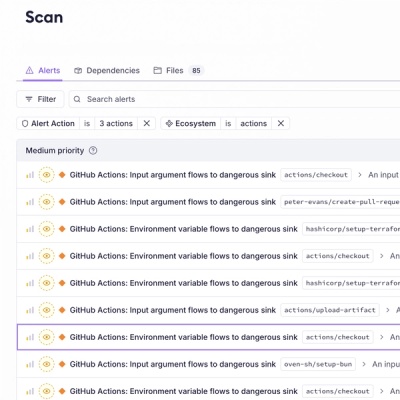
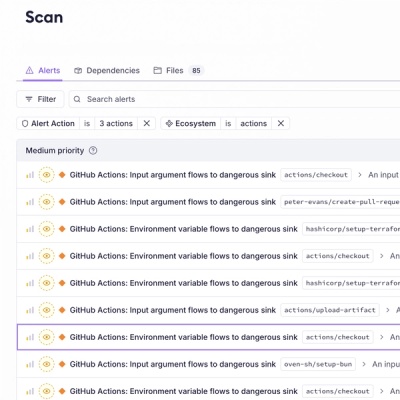
GitHub Actions: GitHub context variable flows to dangerous sink
Known malware
Unstable ownership
GitHub Actions: Input argument flows to dangerous sink
GitHub Actions: Environment variable flows to dangerous sink
Git dependency
GitHub dependency
AI-detected potential malware
HTTP dependency
Critical CVE
High CVE
Medium CVE
Low CVE
Unpopular package
Minified code
Bad dependency semver
Wildcard dependency
Socket optimized override available
Deprecated
Unmaintained
Explicitly Unlicensed Item
License Policy Violation
Misc. License Issues
Ambiguous License Classifier
Copyleft License
License exception
No License Found
Non-permissive License
Unidentified License
Generic alert
Socket detects and blocks malicious dependencies, often within just minutes of them being published to public registries, making it the most effective tool for blocking zero-day supply chain attacks.
Socket is built by a team of prolific open source maintainers whose software is downloaded over 1 billion times per month. We understand how to build tools that developers love. But don’t take our word for it.

Nat Friedman
CEO at GitHub

Suz Hinton
Senior Software Engineer at Stripe
heck yes this is awesome!!! Congrats team 🎉👏

Matteo Collina
Node.js maintainer, Fastify lead maintainer
So awesome to see @SocketSecurity launch with a fresh approach! Excited to have supported the team from the early days.

DC Posch
Director of Technology at AppFolio, CTO at Dynasty
This is going to be super important, especially for crypto projects where a compromised dependency results in stolen user assets.

Luis Naranjo
Software Engineer at Microsoft
If software supply chain attacks through npm don't scare the shit out of you, you're not paying close enough attention.
@SocketSecurity sounds like an awesome product. I'll be using socket.dev instead of npmjs.org to browse npm packages going forward

Elena Nadolinski
Founder and CEO at Iron Fish
Huge congrats to @SocketSecurity! 🙌
Literally the only product that proactively detects signs of JS compromised packages.

Joe Previte
Engineering Team Lead at Coder
Congrats to @feross and the @SocketSecurity team on their seed funding! 🚀 It's been a big help for us at @CoderHQ and we appreciate what y'all are doing!

Josh Goldberg
Staff Developer at Codecademy
This is such a great idea & looks fantastic, congrats & good luck @feross + team!
The best security teams in the world use Socket to get visibility into supply chain risk, and to build a security feedback loop into the development process.

Scott Roberts
CISO at UiPath
As a happy Socket customer, I've been impressed with how quickly they are adding value to the product, this move is a great step!

Yan Zhu
Head of Security at Brave, DEFCON, EFF, W3C
glad to hear some of the smartest people i know are working on (npm, etc.) supply chain security finally :). @SocketSecurity

Andrew Peterson
CEO and Co-Founder at Signal Sciences (acq. Fastly)
How do you track the validity of open source software libraries as they get updated? You're prob not. Check out @SocketSecurity and the updated tooling they launched.
Supply chain is a cluster in security as we all know and the tools from Socket are "duh" type tools to be implementing. Check them out and follow Feross Aboukhadijeh to see more updates coming from them in the future.

Zbyszek Tenerowicz
Senior Security Engineer at ConsenSys
socket.dev is getting more appealing by the hour

Devdatta Akhawe
Head of Security at Figma
The @SocketSecurity team is on fire! Amazing progress and I am exciting to see where they go next.

Sebastian Bensusan
Engineer Manager at Stripe
I find it surprising that we don't have _more_ supply chain attacks in software:
Imagine your airplane (the code running) was assembled (deployed) daily, with parts (dependencies) from internet strangers. How long until you get a bad part?
Excited for Socket to prevent this

Adam Baldwin
VP of Security at npm, Red Team at Auth0/Okta
Congrats to everyone at @SocketSecurity ❤️🤘🏻

Nico Waisman
CISO at Lyft
This is an area that I have personally been very focused on. As Nat Friedman said in the 2019 GitHub Universe keynote, Open Source won, and every time you add a new open source project you rely on someone else code and you rely on the people that build it.
This is both exciting and problematic. You are bringing real risk into your organization, and I'm excited to see progress in the industry from OpenSSF scorecards and package analyzers to the company that Feross Aboukhadijeh is building!
Depend on Socket to prevent malicious open source dependencies from infiltrating your app.
Install the Socket GitHub App in just 2 clicks and get protected today.
Block 70+ issues in open source code, including malware, typo-squatting, hidden code, misleading packages, permission creep, and more.
Reduce work by surfacing actionable security information directly in GitHub. Empower developers to make better decisions.
Attackers have taken notice of the opportunity to attack organizations through open source dependencies. Supply chain attacks rose a whopping 700% in the past year, with over 15,000 recorded attacks.
Dec 14, 2023
Hijacked cryptocurrency library adds malware
Widely-used library in cryptocurrency frontend was compromised to include wallet-draining code, following the hijacking of NPM account credentials via phishing.
Jan 06, 2022
Maintainer intentionally adds malware
Rogue maintainer sabotages his own open source package with 100M downloads/month, notably breaking Amazon's AWS SDK.
Nov 15, 2021
npm discovers a platform vulnerability allowing unauthorized publishing of any package
Attackers could publish new versions of any npm package without authorization for multiple years.
Oct 22, 2021
Hijacked package adds cryptominers and password-stealing malware
Multiple packages with 30M downloads/month are hijacked and publish malicious versions directly into the software supply chain.
Nov 26, 2018
Package hijacked adding organization specific backdoors
Obfuscated malware added to a dependency which targeted a single company, went undetected for over a week, and made it into their production build.
Get our latest security research, open source insights, and product updates.
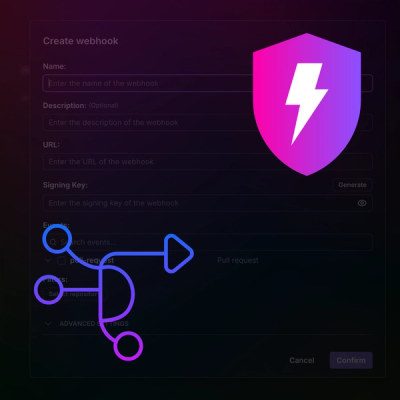
Product
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.
Product
Add real-time Socket webhook events to your workflows to automatically receive pull request scan results and security alerts in real time.

Research
The Socket Threat Research Team uncovered malicious NuGet packages typosquatting the popular Nethereum project to steal wallet keys.