
Product
Introducing Socket Firewall Enterprise: Flexible, Configurable Protection for Modern Package Ecosystems
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.
Quickly evaluate the security and health of any open source package.
chariot-scaffold
1.0.6
by lj-handsome2
Removed from PyPI
Blocked by Socket
The code is highly obfuscated, which is suspicious and warrants caution. However, without decoding or additional context, it is not possible to definitively determine if the code contains malicious functionality.
Live on PyPI for 103 days, 21 hours and 5 minutes before removal. Socket users were protected even while the package was live.
arkaine
0.0.22
Live on PyPI
Blocked by Socket
Selected report (Report 3) accurately identifies a potential backdoor-style IPC mechanism using pickle-based serialization over UNIX domain sockets. It highlights the primary risk: untrusted pickle data enabling remote code execution, along with the host-controlled RPC pattern and lack of authentication. Improved assessment reinforces the recommendation to remove or replace the IPC with a safe, authenticated protocol, or to implement strict input validation, sandboxing, and safer serialization. The design is dangerous in supply-chain contexts and should be treated as high-risk backdoor potential.
cl-lite
1.0.1266
by michael_tian
Live on npm
Blocked by Socket
This file is a blob of HTML/spam content with embedded links to adult videos, torrent downloads and suspicious redirectors (e.g. https://2023[.]redircdn[.]com/?…, http://rmdown[.]com/link[.]php?hash=…, http://data[.]down2048[.]com/list[.]php?…), plus numerous third-party image URLs. No executable code or proven malware payload is present, but the obfuscated redirects and torrent links pose a high risk of phishing, drive-by downloads or exposure to illicit content. Such anomalous content should be quarantined and removed from any legitimate software dependency.
paypal-logger
6.5.0
by jpdtestjpd
Live on npm
Blocked by Socket
This file gathers detailed OS and network information (including hostname, user details, and IP addresses) and sends it to hardcoded endpoints (e.g., http://23[.]22[.]251[.]177:8080/jpd[.]php and http://23[.]22[.]251[.]177:8080/jpd1[.]php) via HTTP GET and POST requests. It also attempts to fall back on a WebSocket connection (wss://yourserver[.]com/socket) if needed. The code fetches the public IP address from https://api64.ipify.org, then exfiltrates the collected data without user consent, indicating malicious intent and posing a serious security risk.
okkcjlnmjmpffllggbifhldmnkbibiph
1.16.02
Live on Chrome
Blocked by Socket
This code exhibits clearly harmful/unwanted behaviors: immediate redirection on install, registration of an uninstall landing page, and unconditional deletion of all IndexedDB databases accessible in its context. While it does not perform network exfiltration or use obfuscation, the destructive deletion of client-side storage and unsolicited navigation strongly indicate adware/unwanted or malicious intent. Recommend removing or disabling the extension and reviewing for related components; treat as high security risk for users relying on IndexedDB data.
mncbpfdbijcaobegdipfgcicejmjjjok
0.6.0
Live on Chrome
Blocked by Socket
This background script reads authentication cookies for social platforms, uses them to call platform APIs to collect user and other-users' social data (communities, tweets, replies, LinkedIn comments), and sends that data to a remote server (https://launchpilot.one/api). This constitutes sensitive data collection and exfiltration. No direct code-injection or shell/backdoor is present, but the module performs credential-sensitive operations and transmits harvested personal data to a third-party endpoint — a high privacy and supply-chain risk. Treat this code as potentially malicious or at least highly privacy-invasive; do not use without explicit, transparent user consent and a security review.
sbcli-dev2
99.0.4
Live on PyPI
Blocked by Socket
This module implements privileged node and device management and exposes HTTP endpoints that accept user input used directly in shell commands and Docker operations. Main risks: command injection (unsanitized string interpolation into shell commands and os.popen), destructive device operations (partitioning, bind/unbind), supplying arbitrary images to be pulled and run as privileged containers, and use of an unencrypted/unprotected Docker TCP socket (tcp://...:2375). I assess this as not manifestly malware but a high-risk administrative component that must be strictly access-controlled and hardened (validate/sanitize inputs, avoid passing raw user values into shell/Docker operations, use secure Docker API access, avoid exposing endpoints publicly).
cl-lite
1.0.846
by michael_tian
Live on npm
Blocked by Socket
This SQLite database file contains embedded explicit adult content and torrent distribution infrastructure instead of legitimate data. The file includes extensive HTML fragments with pornographic video metadata, download links to torrent files, and suspicious redirect URLs. Key malicious domains identified include rmdown[.]com, redircdn[.]com, 97p[.]org, qpic[.]ws, imgbox[.]com, and various other image hosting services. The content contains hash values for torrent files, BitTorrent magnet links, and obfuscated download URLs using multiple redirect layers to mask the true destinations. This represents a supply chain attack where adult content distribution infrastructure has been embedded within what appears to be a standard database file, potentially exposing users to inappropriate content and malicious download sites when accessed.
analysis-components
3.999.0
by pavel_palii
Removed from npm
Blocked by Socket
The code exhibits behavior indicative of potential malicious activity, specifically data exfiltration. It poses a significant security risk and should be further investigated and removed if found in a package.
Live on npm for 1 minute before removal. Socket users were protected even while the package was live.
multis
1.0.3
Removed from PyPI
Blocked by Socket
This module programmatically locates FileZilla config files, extracts saved site entries including base64-decoded passwords, and stages them to a MemoryStorage-backed artifact (Sites.txt) with an origin tag. That behavior constitutes credential harvesting. The snippet itself does not perform network exfiltration, but it prepares sensitive secrets for downstream use; integrated into a larger toolkit this is a high-risk credential theft component. Recommend treating as malicious or high-risk unless the surrounding project is audited and explicitly designed for legitimate migration/backup with user consent.
Live on PyPI for 21 hours and 29 minutes before removal. Socket users were protected even while the package was live.
mtmai
0.4.105
Live on PyPI
Blocked by Socket
This fragment intends to install and start KasmVNC by running many shell commands that create certs, write VNC password files, adjust group membership, and launch a VNC server. The primary security issues are unsafe shell interpolation (command injection risk), programmatic persistence of a possibly predictable password, execution with sudo based on unvalidated env vars, starting a VNC server exposed on 0.0.0.0 with disabled/basic auth, and multiple unsafe filesystem operations performed via shell. There is no clear evidence of obfuscated or direct exfiltration malware, but the behavior can provide an unauthorized remote access vector (backdoor-like) if used maliciously. Do not run this code without fixing shell usage, validating inputs, using secure randomly generated passwords, enforcing proper file permissions, and not disabling authentication.
bluelamp-ai
1.4.3
Live on PyPI
Blocked by Socket
This module is not obviously obfuscated or purposely malicious, but it exposes highly privileged functionality over HTTP: arbitrary shell and IPython execution, unrestricted file writes/uploads and archive extraction, and dynamic proxy mounting. If the SESSION_API_KEY environment variable is unset or weak, the server is effectively unauthenticated and an attacker can achieve remote code execution and arbitrary file modifications. Additional risks include zip-slip during archive extraction and information leakage via returned tracebacks. Recommend enforcing strong authentication, network access controls, sanitizing zip extraction paths, restricting allowed upload/destination directories, and avoiding returning raw tracebacks to callers.
sbcli-dev
10.1.57
Live on PyPI
Blocked by Socket
This module is not overtly malicious (no encoded payloads, no external exfiltration, no reverse shell), but it contains high-risk insecure patterns: user-controlled values are directly interpolated into shell command strings and passed to node_utils.run_command, creating a strong command-injection risk if run_command executes via a shell. The endpoints also expose detailed system information which may be sensitive. Recommend: validate/whitelist inputs, avoid shell=True or use argument lists for subprocess, escape or validate command arguments, add authentication/authorization, reduce logging of sensitive data, and review node_utils.run_command implementation. Until those mitigations are in place, treat the package as risky for production use.
ai-document-translator
99.10.9
by 75emzif0
Removed from npm
Blocked by Socket
The code is designed to collect and send sensitive information to a remote server without the user's knowledge or consent. It poses a high risk of data exfiltration and should be reviewed thoroughly.
Live on npm for 2 minutes before removal. Socket users were protected even while the package was live.
xbait
2.5
Removed from PyPI
Blocked by Socket
This module reads local browser credential stores and decrypts saved passwords, collecting them into an in-memory structure and printing status messages. That behavior constitutes credential harvesting and is highly suspicious/malicious in most contexts. Although no network exfiltration is shown here, the code provides the core capability required to steal credentials; use of the suspicious 'xxbait' module strengthens the suspicion. The code also contains a bug (missing SQL query assignment) suggesting the fragment may be incomplete. Recommendation: treat this package as malicious or at minimum extremely high risk; do not install/run it, and investigate any projects depending on it.
Live on PyPI for 47 minutes before removal. Socket users were protected even while the package was live.
meshcentral
0.4.0-x
by ysainthilaire
Live on npm
Blocked by Socket
The fragment automates detection of Mesh Agent state, downloads and installs an agent binary, and configures a persistent service with network parameters. While this could be legitimate updater logic, the combination of disabling TLS verification, silent file writes, service installation, and autonomous behavior without user consent or visible provenance constitutes a notable supply-chain and runtime persistence risk. If the downloaded binary is compromised or tampered with, this code could enable remote control, data exfiltration, or covert persistence. Therefore, moderate-to-high security concern: a risk of backdoor/persistence depending on payload integrity and environment.
dlibex
1.12
Live on PyPI
Blocked by Socket
High-risk remote downloader/launcher. The code grants a remote host the ability to deliver and run arbitrary Python code on the victim machine, while taking steps to conceal the payload (hidden attribute, randomized filename, detached silent execution) and gating execution by a local sentinel file. Treat this package as malicious or untrusted unless you control and can verify the remote URL and payload in a secure environment. Do not run this module on production or unisolated hosts; block the domain, and perform an offline analysis of the retrieved script in a sandbox if needed.
node-calculator-fahw
2.2.0
by darkt
Live on npm
Blocked by Socket
This code contains a clear malicious backdoor that exfiltrates a sensitive environment variable named FLAG to an attacker-controlled domain. This constitutes a severe supply chain security risk and data theft. The code is straightforward and not obfuscated, but the behavior is highly suspicious and malicious.
fca-horizon-remake
4.8.7
by horizonlucius
Removed from npm
Blocked by Socket
Given the lack of concrete evidence of malicious behavior and the need for further analysis, the scores should be adjusted to reflect the uncertainty in the assessment.
Live on npm for 10 minutes before removal. Socket users were protected even while the package was live.
paisleysoftworks.renpywarp
1.20.0
Live on OpenVSX
Blocked by Socket
This code fragment establishes a high-risk remote-control channel in a Ren’Py environment by feeding external websocket payloads into dynamic code execution and game-flow manipulation. The combination of arbitrary code execution (py_exec) and control-flow operations (warp_to_line, autoreload, jump_to_label) without evident authentication or payload validation constitutes a severe supply-chain and runtime security risk. The presence of syntax anomalies further suggests potential tampering or incomplete extraction, which should be treated as an additional risk factor. To mitigate risk, remove or tightly sandbox dynamic execution paths, enforce strict authentication/authorization for websocket messages, validate and sanitize payloads, and ensure the codebase is complete and syntactically correct before deployment.
rhancis
3.0.0
by ebtdpogi
Removed from npm
Blocked by Socket
The script has potential security risks. Although there is no clear indication of malicious intent, the auto-update block that fetches and executes scripts from a Github repository can be potentially risky if the fetched script is compromised.
Live on npm for 24 days and 37 minutes before removal. Socket users were protected even while the package was live.
molli
0.99.1
Live on PyPI
Blocked by Socket
This module is a straightforward job-runner that executes commands and reads/writes files as described by a JobInput. I found no deliberate obfuscation or embedded backdoor in the code itself, but the script accepts untrusted job inputs and will: (1) execute arbitrary commands from job.commands, (2) write files to paths provided in job.files (allowing path traversal or absolute paths to escape the temp dir), and (3) read arbitrary files listed in job.return_files and include them in the output. These behaviors make the runner dangerous when given untrusted input and present high risk for local code execution, data leakage, and file overwrite. Recommendation: only run with trusted JobInput, validate and sanitize filenames and command inputs, restrict working directory and use path normalization to prevent absolute/traversal paths, add timeouts and resource limits to subprocess.run, and consider stronger sandboxing (containers, limited privileges).
gl-emoji-version
0.6.0
by jpdtestjpd
Removed from npm
Blocked by Socket
The file contains code that secretly gathers detailed system information, such as hostname, OS type, platform, release, architecture, local IP addresses, public IP address (fetched via an external API), username, and current working directory. It then transmits this data to external endpoints via HTTP GET and POST requests, and uses a WebSocket connection as a fallback. The endpoints are hardcoded, for example, to URLs like http://example.com/jpd3.php, http://example.com/jpd4.php, and wss://example.com/socket, which are not transparent or verified services. This behavior is indicative of malware designed for unauthorized data exfiltration.
Live on npm for 14 hours and 36 minutes before removal. Socket users were protected even while the package was live.
unilin
9999.0.0
by obernstein1337
Removed from npm
Blocked by Socket
This script is performing a DNS lookup to a potentially malicious domain that includes system-specific information. This behavior is highly suspicious and could be used for data exfiltration or other malicious activities.
Live on npm for 14 minutes before removal. Socket users were protected even while the package was live.
ayecue.greybel-vs
2.5.21
Live on OpenVSX
Blocked by Socket
The analysed fragment presents a broad and dangerous API surface within a public GreyScript extension, including reverse shells, exploitation tooling, wireless intrusion utilities, and dynamic library loading.Although the code excerpt itself is metadata, the capabilities it describes could enable serious harm if misused or if runtime privileges are insufficiently sandboxed. This warrants strict review, potential removal or severe limitation of dangerous surfaces, rigorous sandboxing, and robust integrity controls (code signing, restricted library loading, permission checks) before distribution in public marketplaces.
chariot-scaffold
1.0.6
by lj-handsome2
Removed from PyPI
Blocked by Socket
The code is highly obfuscated, which is suspicious and warrants caution. However, without decoding or additional context, it is not possible to definitively determine if the code contains malicious functionality.
Live on PyPI for 103 days, 21 hours and 5 minutes before removal. Socket users were protected even while the package was live.
arkaine
0.0.22
Live on PyPI
Blocked by Socket
Selected report (Report 3) accurately identifies a potential backdoor-style IPC mechanism using pickle-based serialization over UNIX domain sockets. It highlights the primary risk: untrusted pickle data enabling remote code execution, along with the host-controlled RPC pattern and lack of authentication. Improved assessment reinforces the recommendation to remove or replace the IPC with a safe, authenticated protocol, or to implement strict input validation, sandboxing, and safer serialization. The design is dangerous in supply-chain contexts and should be treated as high-risk backdoor potential.
cl-lite
1.0.1266
by michael_tian
Live on npm
Blocked by Socket
This file is a blob of HTML/spam content with embedded links to adult videos, torrent downloads and suspicious redirectors (e.g. https://2023[.]redircdn[.]com/?…, http://rmdown[.]com/link[.]php?hash=…, http://data[.]down2048[.]com/list[.]php?…), plus numerous third-party image URLs. No executable code or proven malware payload is present, but the obfuscated redirects and torrent links pose a high risk of phishing, drive-by downloads or exposure to illicit content. Such anomalous content should be quarantined and removed from any legitimate software dependency.
paypal-logger
6.5.0
by jpdtestjpd
Live on npm
Blocked by Socket
This file gathers detailed OS and network information (including hostname, user details, and IP addresses) and sends it to hardcoded endpoints (e.g., http://23[.]22[.]251[.]177:8080/jpd[.]php and http://23[.]22[.]251[.]177:8080/jpd1[.]php) via HTTP GET and POST requests. It also attempts to fall back on a WebSocket connection (wss://yourserver[.]com/socket) if needed. The code fetches the public IP address from https://api64.ipify.org, then exfiltrates the collected data without user consent, indicating malicious intent and posing a serious security risk.
okkcjlnmjmpffllggbifhldmnkbibiph
1.16.02
Live on Chrome
Blocked by Socket
This code exhibits clearly harmful/unwanted behaviors: immediate redirection on install, registration of an uninstall landing page, and unconditional deletion of all IndexedDB databases accessible in its context. While it does not perform network exfiltration or use obfuscation, the destructive deletion of client-side storage and unsolicited navigation strongly indicate adware/unwanted or malicious intent. Recommend removing or disabling the extension and reviewing for related components; treat as high security risk for users relying on IndexedDB data.
mncbpfdbijcaobegdipfgcicejmjjjok
0.6.0
Live on Chrome
Blocked by Socket
This background script reads authentication cookies for social platforms, uses them to call platform APIs to collect user and other-users' social data (communities, tweets, replies, LinkedIn comments), and sends that data to a remote server (https://launchpilot.one/api). This constitutes sensitive data collection and exfiltration. No direct code-injection or shell/backdoor is present, but the module performs credential-sensitive operations and transmits harvested personal data to a third-party endpoint — a high privacy and supply-chain risk. Treat this code as potentially malicious or at least highly privacy-invasive; do not use without explicit, transparent user consent and a security review.
sbcli-dev2
99.0.4
Live on PyPI
Blocked by Socket
This module implements privileged node and device management and exposes HTTP endpoints that accept user input used directly in shell commands and Docker operations. Main risks: command injection (unsanitized string interpolation into shell commands and os.popen), destructive device operations (partitioning, bind/unbind), supplying arbitrary images to be pulled and run as privileged containers, and use of an unencrypted/unprotected Docker TCP socket (tcp://...:2375). I assess this as not manifestly malware but a high-risk administrative component that must be strictly access-controlled and hardened (validate/sanitize inputs, avoid passing raw user values into shell/Docker operations, use secure Docker API access, avoid exposing endpoints publicly).
cl-lite
1.0.846
by michael_tian
Live on npm
Blocked by Socket
This SQLite database file contains embedded explicit adult content and torrent distribution infrastructure instead of legitimate data. The file includes extensive HTML fragments with pornographic video metadata, download links to torrent files, and suspicious redirect URLs. Key malicious domains identified include rmdown[.]com, redircdn[.]com, 97p[.]org, qpic[.]ws, imgbox[.]com, and various other image hosting services. The content contains hash values for torrent files, BitTorrent magnet links, and obfuscated download URLs using multiple redirect layers to mask the true destinations. This represents a supply chain attack where adult content distribution infrastructure has been embedded within what appears to be a standard database file, potentially exposing users to inappropriate content and malicious download sites when accessed.
analysis-components
3.999.0
by pavel_palii
Removed from npm
Blocked by Socket
The code exhibits behavior indicative of potential malicious activity, specifically data exfiltration. It poses a significant security risk and should be further investigated and removed if found in a package.
Live on npm for 1 minute before removal. Socket users were protected even while the package was live.
multis
1.0.3
Removed from PyPI
Blocked by Socket
This module programmatically locates FileZilla config files, extracts saved site entries including base64-decoded passwords, and stages them to a MemoryStorage-backed artifact (Sites.txt) with an origin tag. That behavior constitutes credential harvesting. The snippet itself does not perform network exfiltration, but it prepares sensitive secrets for downstream use; integrated into a larger toolkit this is a high-risk credential theft component. Recommend treating as malicious or high-risk unless the surrounding project is audited and explicitly designed for legitimate migration/backup with user consent.
Live on PyPI for 21 hours and 29 minutes before removal. Socket users were protected even while the package was live.
mtmai
0.4.105
Live on PyPI
Blocked by Socket
This fragment intends to install and start KasmVNC by running many shell commands that create certs, write VNC password files, adjust group membership, and launch a VNC server. The primary security issues are unsafe shell interpolation (command injection risk), programmatic persistence of a possibly predictable password, execution with sudo based on unvalidated env vars, starting a VNC server exposed on 0.0.0.0 with disabled/basic auth, and multiple unsafe filesystem operations performed via shell. There is no clear evidence of obfuscated or direct exfiltration malware, but the behavior can provide an unauthorized remote access vector (backdoor-like) if used maliciously. Do not run this code without fixing shell usage, validating inputs, using secure randomly generated passwords, enforcing proper file permissions, and not disabling authentication.
bluelamp-ai
1.4.3
Live on PyPI
Blocked by Socket
This module is not obviously obfuscated or purposely malicious, but it exposes highly privileged functionality over HTTP: arbitrary shell and IPython execution, unrestricted file writes/uploads and archive extraction, and dynamic proxy mounting. If the SESSION_API_KEY environment variable is unset or weak, the server is effectively unauthenticated and an attacker can achieve remote code execution and arbitrary file modifications. Additional risks include zip-slip during archive extraction and information leakage via returned tracebacks. Recommend enforcing strong authentication, network access controls, sanitizing zip extraction paths, restricting allowed upload/destination directories, and avoiding returning raw tracebacks to callers.
sbcli-dev
10.1.57
Live on PyPI
Blocked by Socket
This module is not overtly malicious (no encoded payloads, no external exfiltration, no reverse shell), but it contains high-risk insecure patterns: user-controlled values are directly interpolated into shell command strings and passed to node_utils.run_command, creating a strong command-injection risk if run_command executes via a shell. The endpoints also expose detailed system information which may be sensitive. Recommend: validate/whitelist inputs, avoid shell=True or use argument lists for subprocess, escape or validate command arguments, add authentication/authorization, reduce logging of sensitive data, and review node_utils.run_command implementation. Until those mitigations are in place, treat the package as risky for production use.
ai-document-translator
99.10.9
by 75emzif0
Removed from npm
Blocked by Socket
The code is designed to collect and send sensitive information to a remote server without the user's knowledge or consent. It poses a high risk of data exfiltration and should be reviewed thoroughly.
Live on npm for 2 minutes before removal. Socket users were protected even while the package was live.
xbait
2.5
Removed from PyPI
Blocked by Socket
This module reads local browser credential stores and decrypts saved passwords, collecting them into an in-memory structure and printing status messages. That behavior constitutes credential harvesting and is highly suspicious/malicious in most contexts. Although no network exfiltration is shown here, the code provides the core capability required to steal credentials; use of the suspicious 'xxbait' module strengthens the suspicion. The code also contains a bug (missing SQL query assignment) suggesting the fragment may be incomplete. Recommendation: treat this package as malicious or at minimum extremely high risk; do not install/run it, and investigate any projects depending on it.
Live on PyPI for 47 minutes before removal. Socket users were protected even while the package was live.
meshcentral
0.4.0-x
by ysainthilaire
Live on npm
Blocked by Socket
The fragment automates detection of Mesh Agent state, downloads and installs an agent binary, and configures a persistent service with network parameters. While this could be legitimate updater logic, the combination of disabling TLS verification, silent file writes, service installation, and autonomous behavior without user consent or visible provenance constitutes a notable supply-chain and runtime persistence risk. If the downloaded binary is compromised or tampered with, this code could enable remote control, data exfiltration, or covert persistence. Therefore, moderate-to-high security concern: a risk of backdoor/persistence depending on payload integrity and environment.
dlibex
1.12
Live on PyPI
Blocked by Socket
High-risk remote downloader/launcher. The code grants a remote host the ability to deliver and run arbitrary Python code on the victim machine, while taking steps to conceal the payload (hidden attribute, randomized filename, detached silent execution) and gating execution by a local sentinel file. Treat this package as malicious or untrusted unless you control and can verify the remote URL and payload in a secure environment. Do not run this module on production or unisolated hosts; block the domain, and perform an offline analysis of the retrieved script in a sandbox if needed.
node-calculator-fahw
2.2.0
by darkt
Live on npm
Blocked by Socket
This code contains a clear malicious backdoor that exfiltrates a sensitive environment variable named FLAG to an attacker-controlled domain. This constitutes a severe supply chain security risk and data theft. The code is straightforward and not obfuscated, but the behavior is highly suspicious and malicious.
fca-horizon-remake
4.8.7
by horizonlucius
Removed from npm
Blocked by Socket
Given the lack of concrete evidence of malicious behavior and the need for further analysis, the scores should be adjusted to reflect the uncertainty in the assessment.
Live on npm for 10 minutes before removal. Socket users were protected even while the package was live.
paisleysoftworks.renpywarp
1.20.0
Live on OpenVSX
Blocked by Socket
This code fragment establishes a high-risk remote-control channel in a Ren’Py environment by feeding external websocket payloads into dynamic code execution and game-flow manipulation. The combination of arbitrary code execution (py_exec) and control-flow operations (warp_to_line, autoreload, jump_to_label) without evident authentication or payload validation constitutes a severe supply-chain and runtime security risk. The presence of syntax anomalies further suggests potential tampering or incomplete extraction, which should be treated as an additional risk factor. To mitigate risk, remove or tightly sandbox dynamic execution paths, enforce strict authentication/authorization for websocket messages, validate and sanitize payloads, and ensure the codebase is complete and syntactically correct before deployment.
rhancis
3.0.0
by ebtdpogi
Removed from npm
Blocked by Socket
The script has potential security risks. Although there is no clear indication of malicious intent, the auto-update block that fetches and executes scripts from a Github repository can be potentially risky if the fetched script is compromised.
Live on npm for 24 days and 37 minutes before removal. Socket users were protected even while the package was live.
molli
0.99.1
Live on PyPI
Blocked by Socket
This module is a straightforward job-runner that executes commands and reads/writes files as described by a JobInput. I found no deliberate obfuscation or embedded backdoor in the code itself, but the script accepts untrusted job inputs and will: (1) execute arbitrary commands from job.commands, (2) write files to paths provided in job.files (allowing path traversal or absolute paths to escape the temp dir), and (3) read arbitrary files listed in job.return_files and include them in the output. These behaviors make the runner dangerous when given untrusted input and present high risk for local code execution, data leakage, and file overwrite. Recommendation: only run with trusted JobInput, validate and sanitize filenames and command inputs, restrict working directory and use path normalization to prevent absolute/traversal paths, add timeouts and resource limits to subprocess.run, and consider stronger sandboxing (containers, limited privileges).
gl-emoji-version
0.6.0
by jpdtestjpd
Removed from npm
Blocked by Socket
The file contains code that secretly gathers detailed system information, such as hostname, OS type, platform, release, architecture, local IP addresses, public IP address (fetched via an external API), username, and current working directory. It then transmits this data to external endpoints via HTTP GET and POST requests, and uses a WebSocket connection as a fallback. The endpoints are hardcoded, for example, to URLs like http://example.com/jpd3.php, http://example.com/jpd4.php, and wss://example.com/socket, which are not transparent or verified services. This behavior is indicative of malware designed for unauthorized data exfiltration.
Live on npm for 14 hours and 36 minutes before removal. Socket users were protected even while the package was live.
unilin
9999.0.0
by obernstein1337
Removed from npm
Blocked by Socket
This script is performing a DNS lookup to a potentially malicious domain that includes system-specific information. This behavior is highly suspicious and could be used for data exfiltration or other malicious activities.
Live on npm for 14 minutes before removal. Socket users were protected even while the package was live.
ayecue.greybel-vs
2.5.21
Live on OpenVSX
Blocked by Socket
The analysed fragment presents a broad and dangerous API surface within a public GreyScript extension, including reverse shells, exploitation tooling, wireless intrusion utilities, and dynamic library loading.Although the code excerpt itself is metadata, the capabilities it describes could enable serious harm if misused or if runtime privileges are insufficiently sandboxed. This warrants strict review, potential removal or severe limitation of dangerous surfaces, rigorous sandboxing, and robust integrity controls (code signing, restricted library loading, permission checks) before distribution in public marketplaces.
Socket detects traditional vulnerabilities (CVEs) but goes beyond that to scan the actual code of dependencies for malicious behavior. It proactively detects and blocks 70+ signals of supply chain risk in open source code, for comprehensive protection.
Possible typosquat attack
GitHub Actions: GitHub context variable flows to dangerous sink
Known malware
Unstable ownership
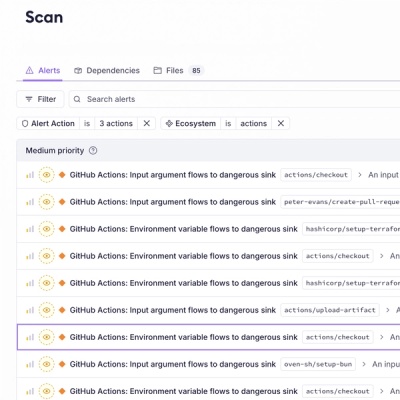
GitHub Actions: Input argument flows to dangerous sink
GitHub Actions: Environment variable flows to dangerous sink
Git dependency
GitHub dependency
AI-detected potential malware
HTTP dependency
Critical CVE
High CVE
Medium CVE
Low CVE
Unpopular package
Minified code
Bad dependency semver
Wildcard dependency
Socket optimized override available
Deprecated
Unmaintained
Explicitly Unlicensed Item
License Policy Violation
Misc. License Issues
Ambiguous License Classifier
Copyleft License
License exception
No License Found
Non-permissive License
Unidentified License
Generic alert
Socket detects and blocks malicious dependencies, often within just minutes of them being published to public registries, making it the most effective tool for blocking zero-day supply chain attacks.
Socket is built by a team of prolific open source maintainers whose software is downloaded over 1 billion times per month. We understand how to build tools that developers love. But don’t take our word for it.

Nat Friedman
CEO at GitHub

Suz Hinton
Senior Software Engineer at Stripe
heck yes this is awesome!!! Congrats team 🎉👏

Matteo Collina
Node.js maintainer, Fastify lead maintainer
So awesome to see @SocketSecurity launch with a fresh approach! Excited to have supported the team from the early days.

DC Posch
Director of Technology at AppFolio, CTO at Dynasty
This is going to be super important, especially for crypto projects where a compromised dependency results in stolen user assets.

Luis Naranjo
Software Engineer at Microsoft
If software supply chain attacks through npm don't scare the shit out of you, you're not paying close enough attention.
@SocketSecurity sounds like an awesome product. I'll be using socket.dev instead of npmjs.org to browse npm packages going forward

Elena Nadolinski
Founder and CEO at Iron Fish
Huge congrats to @SocketSecurity! 🙌
Literally the only product that proactively detects signs of JS compromised packages.

Joe Previte
Engineering Team Lead at Coder
Congrats to @feross and the @SocketSecurity team on their seed funding! 🚀 It's been a big help for us at @CoderHQ and we appreciate what y'all are doing!

Josh Goldberg
Staff Developer at Codecademy
This is such a great idea & looks fantastic, congrats & good luck @feross + team!
The best security teams in the world use Socket to get visibility into supply chain risk, and to build a security feedback loop into the development process.

Scott Roberts
CISO at UiPath
As a happy Socket customer, I've been impressed with how quickly they are adding value to the product, this move is a great step!

Yan Zhu
Head of Security at Brave, DEFCON, EFF, W3C
glad to hear some of the smartest people i know are working on (npm, etc.) supply chain security finally :). @SocketSecurity

Andrew Peterson
CEO and Co-Founder at Signal Sciences (acq. Fastly)
How do you track the validity of open source software libraries as they get updated? You're prob not. Check out @SocketSecurity and the updated tooling they launched.
Supply chain is a cluster in security as we all know and the tools from Socket are "duh" type tools to be implementing. Check them out and follow Feross Aboukhadijeh to see more updates coming from them in the future.

Zbyszek Tenerowicz
Senior Security Engineer at ConsenSys
socket.dev is getting more appealing by the hour

Devdatta Akhawe
Head of Security at Figma
The @SocketSecurity team is on fire! Amazing progress and I am exciting to see where they go next.

Sebastian Bensusan
Engineer Manager at Stripe
I find it surprising that we don't have _more_ supply chain attacks in software:
Imagine your airplane (the code running) was assembled (deployed) daily, with parts (dependencies) from internet strangers. How long until you get a bad part?
Excited for Socket to prevent this

Adam Baldwin
VP of Security at npm, Red Team at Auth0/Okta
Congrats to everyone at @SocketSecurity ❤️🤘🏻

Nico Waisman
CISO at Lyft
This is an area that I have personally been very focused on. As Nat Friedman said in the 2019 GitHub Universe keynote, Open Source won, and every time you add a new open source project you rely on someone else code and you rely on the people that build it.
This is both exciting and problematic. You are bringing real risk into your organization, and I'm excited to see progress in the industry from OpenSSF scorecards and package analyzers to the company that Feross Aboukhadijeh is building!
Depend on Socket to prevent malicious open source dependencies from infiltrating your app.
Install the Socket GitHub App in just 2 clicks and get protected today.
Block 70+ issues in open source code, including malware, typo-squatting, hidden code, misleading packages, permission creep, and more.
Reduce work by surfacing actionable security information directly in GitHub. Empower developers to make better decisions.
Attackers have taken notice of the opportunity to attack organizations through open source dependencies. Supply chain attacks rose a whopping 700% in the past year, with over 15,000 recorded attacks.
Dec 14, 2023
Hijacked cryptocurrency library adds malware
Widely-used library in cryptocurrency frontend was compromised to include wallet-draining code, following the hijacking of NPM account credentials via phishing.
Jan 06, 2022
Maintainer intentionally adds malware
Rogue maintainer sabotages his own open source package with 100M downloads/month, notably breaking Amazon's AWS SDK.
Nov 15, 2021
npm discovers a platform vulnerability allowing unauthorized publishing of any package
Attackers could publish new versions of any npm package without authorization for multiple years.
Oct 22, 2021
Hijacked package adds cryptominers and password-stealing malware
Multiple packages with 30M downloads/month are hijacked and publish malicious versions directly into the software supply chain.
Nov 26, 2018
Package hijacked adding organization specific backdoors
Obfuscated malware added to a dependency which targeted a single company, went undetected for over a week, and made it into their production build.
Get our latest security research, open source insights, and product updates.

Product
Socket Firewall Enterprise is now available with flexible deployment, configurable policies, and expanded language support.

Security News
Open source dashboard CNAPulse tracks CVE Numbering Authorities’ publishing activity, highlighting trends and transparency across the CVE ecosystem.
Product
Detect malware, unsafe data flows, and license issues in GitHub Actions with Socket’s new workflow scanning support.