Research
Security News
Malicious npm Package Typosquats react-login-page to Deploy Keylogger
Socket researchers unpack a typosquatting package with malicious code that logs keystrokes and exfiltrates sensitive data to a remote server.
@aws-cdk/cloud-assembly-schema
Advanced tools
Package description
@aws-cdk/cloud-assembly-schema is a package that defines the schema for AWS Cloud Development Kit (CDK) cloud assemblies. It provides a set of TypeScript interfaces and JSON schemas that describe the structure of the cloud assembly, which is the output of the CDK synthesis process. This package is essential for tools and libraries that need to interact with or manipulate CDK cloud assemblies.
Cloud Assembly Schema Definition
Defines the schema for a cloud assembly, including the version and artifacts. This schema is used to validate the structure of a cloud assembly JSON file.
{"type":"object","properties":{"version":{"type":"string"},"artifacts":{"type":"object","additionalProperties":{"$ref":"#/definitions/Artifact"}}},"required":["version","artifacts"],"definitions":{"Artifact":{"type":"object","properties":{"type":{"type":"string"},"properties":{"type":"object"}},"required":["type"]}}}Artifact Type Definitions
Defines the schema for different types of artifacts, such as CloudFormation stacks and CDK assets. This schema is used to validate the structure of artifact definitions within a cloud assembly.
{"type":"object","properties":{"type":{"type":"string","enum":["aws:cloudformation:stack","aws:cdk:asset"]},"properties":{"type":"object","properties":{"templateFile":{"type":"string"},"parameters":{"type":"object","additionalProperties":{"type":"string"}}},"required":["templateFile"]}},"required":["type","properties"]}The aws-cdk-lib package is the main library for the AWS Cloud Development Kit (CDK). It provides constructs for defining AWS infrastructure in code. While @aws-cdk/cloud-assembly-schema focuses on the schema of the cloud assembly, aws-cdk-lib provides the constructs and classes needed to define and synthesize the infrastructure itself.
cdk8s is a software development framework for defining Kubernetes applications and resources using familiar programming languages. Similar to how @aws-cdk/cloud-assembly-schema defines the schema for AWS CDK cloud assemblies, cdk8s provides schemas and constructs for defining Kubernetes manifests.
The terraform-cdk package allows users to define infrastructure using Terraform and the AWS CDK. It provides a way to use the CDK's programming model with Terraform's infrastructure as code capabilities. While @aws-cdk/cloud-assembly-schema is specific to AWS CDK cloud assemblies, terraform-cdk bridges the gap between CDK and Terraform.
Changelog
1.78.0 (2020-12-11)
HttpOrigin and LoadBalancerOrigin changed from SSLv3 to TLSv1.2.domainName property under DomainName has been
renamed to name.dnsHostName and awsCloudMap of VirtualNodeProps have been replaced with the property serviceDiscoverymetricFailed uses Average instead of Sum by default (#11941) (3530e8c)Readme
This module is part of the AWS Cloud Development Kit project.
The Cloud Assembly is the output of the synthesis operation. It is produced as part of the
cdk synth
command, or the app.synth() method invocation.
Its essentially a set of files and directories, one of which is the manifest.json file. It defines the set of instructions that are
needed in order to deploy the assembly directory.
For example, when
cdk deployis executed, the CLI reads this file and performs its instructions:
- Build container images.
- Upload assets.
- Deploy CloudFormation templates.
Therefore, the assembly is how the CDK class library and CDK CLI (or any other consumer) communicate. To ensure compatibility between the assembly and its consumers, we treat the manifest file as a well defined, versioned schema.
This module contains the typescript structs that comprise the manifest.json file, as well as the
generated json-schema.
The schema version is specified in the cloud-assembly.version.json file, under the version property.
It follows semantic versioning, but with a small twist.
When we add instructions to the assembly, they are reflected in the manifest file and the json-schema accordingly. Every such instruction, is crucial for ensuring the correct deployment behavior. This means that to properly deploy a cloud assembly, consumers must be aware of every such instruction modification.
For this reason, every change to the schema, even though it might not strictly break validation of the json-schema format,
is considered major version bump.
If you'd like to consume the schema file in order to do validations on manifest.json files,
simply download it from this repo and run it against standard json-schema validators, such as jsonschema.
Consumers must take into account the major version of the schema they are consuming. They should reject cloud assemblies
with a major version that is higher than what they expect. While schema validation might pass on such assemblies, the deployment integrity
cannot be guaranteed because some instructions will be ignored.
For example, if your consumer was built when the schema version was 2.0.0, you should reject deploying cloud assemblies with a manifest version of 3.0.0.
FAQs
Unknown package
We found that @aws-cdk/cloud-assembly-schema demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 0 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Research
Security News
Socket researchers unpack a typosquatting package with malicious code that logs keystrokes and exfiltrates sensitive data to a remote server.

Security News
The JavaScript community has launched the e18e initiative to improve ecosystem performance by cleaning up dependency trees, speeding up critical parts of the ecosystem, and documenting lighter alternatives to established tools.
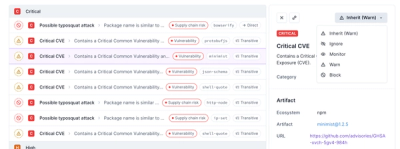
Product
Socket now supports four distinct alert actions instead of the previous two, and alert triaging allows users to override the actions taken for all individual alerts.