
Security News
The Push to Ban Ransom Payments Is Gaining Momentum
Ransomware costs victims an estimated $30 billion per year and has gotten so out of control that global support for banning payments is gaining momentum.
@nictool/dns-resource-record
Advanced tools
Changelog
[1.2.1] - 2024-03-10
Readme
DNS resource record parser, validator, importer, and exporter.
This module is used to:
| RR format | import | export |
|---|---|---|
| JSON | :white_check_mark: | :white_check_mark: |
| BIND | :white_check_mark: | :white_check_mark: |
| Tinydns | :white_check_mark: | :white_check_mark: |
| MaraDNS | :white_check_mark: | |
| JS | :white_check_mark: | :white_check_mark: |
This package intends to import and export RFC compliant DNS resource records. Please raise an issue if you a valid resource record fails to pass or an invalid resource record passes.
This package is for working with individual Resource Records. For working with zones of RRs, use dns-zone.
Load the index for access to all RR types:
import * as RR from '@nictool/dns-resource-record'
const exampleRRs = {
A: {
owner : 'test.example.com.',
type : 'A',
address: '192.0.2.127',
ttl : 3600,
},
AAAA: {
owner : 'test.example.com.',
type : 'AAAA',
address: '2605:7900:20:a::4',
ttl : 3600,
},
SOA: {
owner : 'example.com.',
type : 'SOA',
mname : 'matt.example.com.',
rname : 'ns1.example.com.',
serial : 1,
refresh: 7200,
retry : 3600,
expire : 1209600,
minimum: 3600,
ttl : 3600,
}
}
try {
console.log(new RR.SOA(exampleRRs.SOA))
SOA(11) [Map] {
'owner' => 'example.com.',
'ttl' => 3600,
'class' => 'IN',
'type' => 'SOA',
'mname' => 'matt.example.com.',
'rname' => 'ns1.example.com.',
'serial' => 1,
'refresh' => 7200,
'retry' => 3600,
'expire' => 1209600,
'minimum' => 3600
}
}
catch (e) {
console.error(e.message) // invalid RRs throw
}
Validate records by passing a properly formatted JS object to the record-specific class. To validate an A record:
const validatedA = new RR.A(exampleRRs.A)
Manipulate the validated record using pattern named setters:
console.log(validatedA.toBind())
test.example.com. 3600 IN A 192.0.2.127
validatedA.setAddress('192.0.2.128')
console.log(validatedA.toBind())
test.example.com. 3600 IN A 192.0.2.128
The setters are named: set + Field, where field is the resource record field name to modify. Multi-word names are camel cased, so a field named Certificate Usage has a setter named setCertificateUsage. The RFCs aren't always consistent regarding RR field names so aliases are permissible for interoperability.
Get the field names for each RR type with getFields():
> import * as RR from 'dns-resource-record'
> new RR.A(null).getFields()
[ 'owner', 'ttl', 'class', 'type', 'address' ]
> new RR.PTR(null).getFields()
[ 'owner', 'ttl', 'class', 'type', 'dname' ]
> new RR.SSHFP(null).getFields()
[ 'owner', 'ttl', 'class', 'type', 'algorithm', 'fptype', 'fingerprint' ]
Get a list of RFCs for references about each RR type:
> new RR.A(null).getRFCs()
[ 1035 ]
> new RR.SRV(null).getRFCs()
[ 2782 ]
> new RR.MX(null).getRFCs()
[ 1035, 2181, 7505 ]
Validate a record and export to BIND format.
console.log(new RR.A(exampleRRs.A).toBind())
test.example.com 3600 IN A 192.0.2.127
console.log(new RR.AAAA(exampleRRs.AAAA).toBind())
test.example.com 3600 IN AAAA 2605:7900:20:a::4
Validate a record and export to tinydns format:
console.log(new RR.A(exampleRRs.A).toTinydns())
+test.example.com:192.0.2.127:3600::
Convert a tinydns line to BIND:
console.log(new RR.CAA({
tinyline: ':ns1.example.com:257:\\000\\005issue"http\\072\\057\\057letsencrypt.org":3600::\n'
}).toBind())
ns1.example.com 3600 IN CAA 0 issue "http://letsencrypt.org"
The DNS validation checks can be bypassed entirely by using 'set':
> validatedA.set('address', 'oops')
A(5) [Map] {
'owner' => 'test.example.com',
'ttl' => 3600,
'class' => 'IN',
'type' => 'A',
'address' => 'oops'
}
Consider this a "running with scissors" mode.
This module intends to include support for all current (ie, not officially deprecated) DNS RRs and all RRs that are in active use on the internet.
PRs are welcome, especially PRs with tests.
| RR | toBind | toTinydns | fromBind | fromTinydns |
|---|---|---|---|---|
| A | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| AAAA | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| CAA | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| CERT | :white_check_mark: | :white_check_mark: | ||
| CNAME | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| DNAME | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| DNSKEY | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| DS | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| HINFO | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| HTTPS | ||||
| IPSECKEY | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| KEY | ||||
| LOC | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| MX | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| NAPTR | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| NS | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| NSEC | :white_check_mark: | :white_check_mark: | ||
| NSEC3 | :white_check_mark: | :white_check_mark: | :white_check_mark: | |
| NSEC3PARAM | ||||
| NXT | ||||
| OPENPGPKEY | ||||
| PTR | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| RRSIG | ||||
| SIG | ||||
| SMIMEA | :white_check_mark: | :white_check_mark: | ||
| SOA | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| SPF | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| SRV | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| SSHFP | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| SVCB | ||||
| TLSA | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| TSIG | ||||
| TXT | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| URI | :white_check_mark: | :white_check_mark: | :white_check_mark: | :white_check_mark: |
| WKS |
bin/dns-zone in the dns-zone package.FAQs
DNS Resource Records
We found that @nictool/dns-resource-record demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Ransomware costs victims an estimated $30 billion per year and has gotten so out of control that global support for banning payments is gaining momentum.
Application Security
New SEC disclosure rules aim to enforce timely cyber incident reporting, but fear of job loss and inadequate resources lead to significant underreporting.
Security News
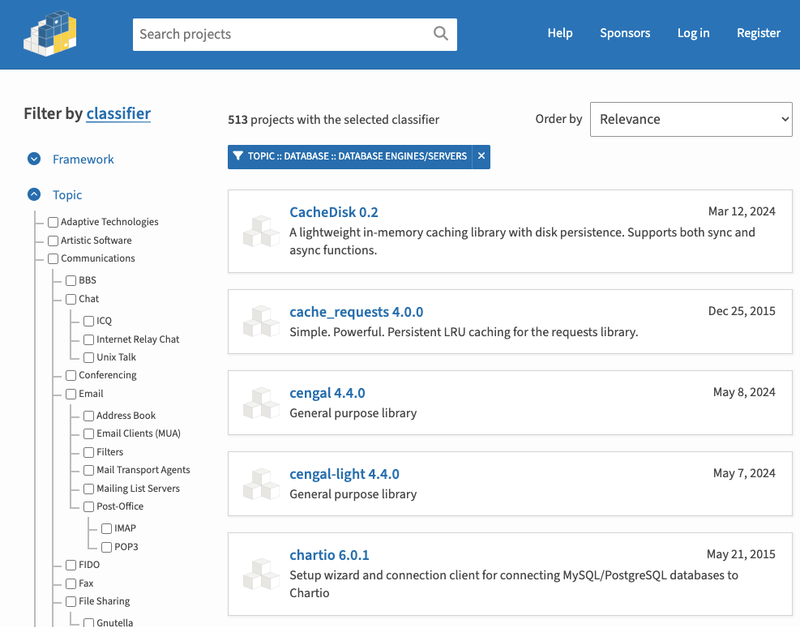
The Python Software Foundation has secured a 5-year sponsorship from Fastly that supports PSF's activities and events, most notably the security and reliability of the Python Package Index (PyPI).