
Product
Introducing Tier 1 Reachability: Precision CVE Triage for Enterprise Teams
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Aether aims to make it easy for people to learn and write JavaScript and CoffeeScript by helping them catch and fix bugs, letting them see and more easily understand the execution of their program (like Bret Victor commanded!), and giving them tips on how they can improve their code. CodeCombat is behind it.
You can use the GitHub issues, the Discourse forum, the HipChat, or email Nick.
It's a JavaScript library (written in CoffeeScript) that takes user code as input; does computer-sciencey transpilation things to it with the help of JSHint, Esprima, escodegen, and Esper (soon to be open source); and gives you linting, transformation, sandboxing, instrumentation, time-travel debugging, style analysis, autocompletion, and more. It used to output transpiled code for you to run, but now it includes an interpreter for better correctness and performance.
If you'd like to contribute, please sign the CodeCombat contributor license agreement so we can accept your pull requests. It is easy.
======

FAQs
Analyzes, instruments, and transpiles JS to help beginners.
The npm package aether receives a total of 22 weekly downloads. As such, aether popularity was classified as not popular.
We found that aether demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 3 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Research
/Security News
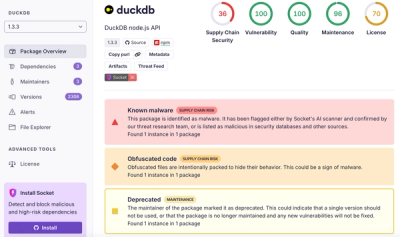
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.