
Product
Introducing Rust Support in Socket
Socket now supports Rust and Cargo, offering package search for all users and experimental SBOM generation for enterprise projects.
[](https://app.wercker.com/project/bykey/fe30b946cc0ec765b7f89d03ae512793)
This is the TCG auth service. It's named AuthX because it's an "exchange" of sorts, consolidating identities from several upstream authorities into a single identity for downstream clients. AuthX uses the OAuth2 framework in both directions, and adds an authorization layer. Authorization control is based on the simple scopes spec.
AuthX is designed for a scenario in which a RESOURCE needs to restrict access to all or part of its functionality. A CLIENT app, acting on behalf of a User can retreive an OAuth token from AuthX, which can be passed to the RESOURCE with any request.
╔══════════════════════════════════════════╗
║ ┌───────────┐ ║
║ │ AUTHORITY │ ║
║ └─────┬─────┘ ║
║▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓│▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓║
║ ┌────────────┐ ┌─────┴─────┐ ║
║ │ Credential ├─┤ Authority │ ║
║ └───┬────────┘ └───────────┘ ║
║ ┌───┴──┐ Authentication ║
║░░░│ User │░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░║
║ └─┬──┬─┘ ┌──────┐ ║
║ │ └────────────────┤ Role │ ║
║ ┌┴──────┐ ┌────────┐ └──────┘ ║
║ │ Grant ├─┤ Client │ ║
║ └───────┘ └───┬────┘ Authorization ║
║▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓│▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓║
║ ┌───┴────┐ ┌──────────┐ ║
║ │ CLIENT ├─┤ RESOURCE │ ║
║ └────────┘ └──────────┘ ║
╚══════════════════════════════════════════╝
The user is (obviously) the primary component. It consists of a unique ID and profile information in the format of Portable Contacts. Information in the profile is not verified, and is not directly used by AuthX system for authentication.
An authority is a mechanism for authentication, and provides the configuration for corresponding units of code called strategies. Several strategies are included by default:
Credentials connect users to authorities. A user can typically have multiple authorities of the same authority (multiple emails, for example).
Clients are downstream applications that uses AuthX for authentication/authorization.
A user gives a client permission to act on her behalf via a grant.
A role bestows its permissions to every user it includes.
Scopes are composed of 3 domains, separated by the : character:
AuthX:role.abc:read
|___| |______| |__|
| | |
realm resource action
Each domain can contain parts, separated by the . character. Domain parts can be /[a-zA-Z0-9_]*/ strings or glob pattern identifiers * or **:
role.abc
role.*
**
AuthX uses its own authorization system to restrict access to its resources. Below are the scopes used by AuthX internally:
AuthX:authority:read.{basic|details}
AuthX:authority:write.{basic|details|*}
AuthX:client.{assigned|*}:read.{basic|secrets|assignments}
AuthX:client.{assigned|*}:write.{basic|secrets|assignments|*}
AuthX:credential.equal.self :read.{basic|details}
AuthX:credential.equal.lesser:read.{basic|details}
AuthX:credential.equal.* :read.{basic|details}
AuthX:credential.* .* :read.{basic|details}
AuthX:credential.equal.self :write.{basic|details|*}
AuthX:credential.equal.lesser:write.{basic|details|*}
AuthX:credential.equal.* :write.{basic|details|*}
AuthX:credential.* .* :write.{basic|details|*}
AuthX:grant.assigned :read.{basic|scopes|secrets}
AuthX:grant.equal.self :read.{basic|scopes|secrets}
AuthX:grant.equal.lesser:read.{basic|scopes|secrets}
AuthX:grant.equal.* :read.{basic|scopes|secrets}
AuthX:grant.* .* :read.{basic|scopes|secrets}
AuthX:grant.equal.self :write.{basic|scopes|secrets|*}
AuthX:grant.equal.lesser:write.{basic|scopes|secrets|*}
AuthX:grant.equal.* :write.{basic|scopes|secrets|*}
AuthX:grant.* .* :write.{basic|scopes|secrets|*}
AuthX:role.equal.assigned:read.{basic|scopes|assignments}
AuthX:role.equal.lesser :read.{basic|scopes|assignments}
AuthX:role.equal.* :read.{basic|scopes|assignments}
AuthX:role.* .* :read.{basic|scopes|assignments}
AuthX:role.equal.assigned:write.{basic|scopes|assignments|*}
AuthX:role.equal.lesser :write.{basic|scopes|assignments|*}
AuthX:role.equal.* :write.{basic|scopes|assignments|*}
AuthX:role.* .* :write.{basic|scopes|assignments|*}
AuthX:token.assigned :read.{basic|scopes|secrets}
AuthX:token.equal.self :read.{basic|scopes|secrets}
AuthX:token.equal.lesser:read.{basic|scopes|secrets}
AuthX:token.equal.* :read.{basic|scopes|secrets}
AuthX:token.* .* :read.{basic|scopes|secrets}
AuthX:token.equal.self :write.{basic|scopes|secrets|*}
AuthX:token.equal.lesser:write.{basic|scopes|secrets|*}
AuthX:token.equal.* :write.{basic|scopes|secrets|*}
AuthX:token.* .* :write.{basic|scopes|secrets|*}
AuthX:user.equal.self :read.{basic}
AuthX:user.equal.lesser:read.{basic}
AuthX:user.equal.* :read.{basic}
AuthX:user.* .* :read.{basic}
AuthX:user.equal.self :write.{basic|*}
AuthX:user.equal.lesser:write.{basic|*}
AuthX:user.equal.* :write.{basic|*}
AuthX:user.* .* :write.{basic|*}
FAQs
AuthX is designed for a scenario in which a **RESOURCE** needs to restrict access to all or part of its functionality. A **CLIENT** app, acting on behalf of a **User** can retreive an OAuth token from AuthX, which can be passed to the **RESOURCE** with an
We found that authx demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 3 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket now supports Rust and Cargo, offering package search for all users and experimental SBOM generation for enterprise projects.
Product
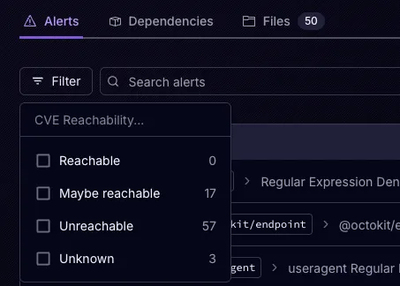
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.

Product
Socket is launching experimental protection for Chrome extensions, scanning for malware and risky permissions to prevent silent supply chain attacks.