
Product
Introducing Tier 1 Reachability: Precision CVE Triage for Enterprise Teams
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
ghost-client
Advanced tools

This module connects to your Ghost blog and gives you a list of what you need, posts, tags or users.
Ghost API is currently in Beta, you have to configure your blog to access the API and you have to get a token or a ID and a Secret Code to get what you want.
[](https://nodei.co/npm/ghost-client/)
To download the Ghost API Client that I've made simply download it via NPM. NPM is always going to have the latest stable version of it. Be free to add any flag after the command such as --save or --save-dev
$ npm install ghost-client
To use the Client Authentication method described on the API Docs of Ghost you have to give the instance of the Ghost API Client a clientId and a clientSecret. See Ghost Docs to find how to obtain it
var ghost = require('ghost-client')
var Client = ghost.createClient({
endpoint: 'http://my-ghost-blog.com',
clientId: 'ghost-frontend',
clientSecret: 'rabbitsareawesome'
})
To use the User Authentication method described on the API Docs of Ghost you have to give the instance of the Ghost API Client a Bearer Token. See Ghost Docs to find how to obtain it
var ghost = require('ghost-client')
var Client = ghost.createClient({
endpoint: 'http://my-ghost-blog.com',
token: 'Bearer 0X0X0X0X0X0X0X0X0X0X0X'
})
Client means the variable that has the client to connect to the Ghost API correctly configured. See authentication again to see more about that variable.
Brings posts list from a Ghost Blog.
Client.posts({}, function (err, posts) {
if (err) console.log(err)
console.log(posts)
})
Brings tags list from a Ghost Blog.
Client.tags({}, function (err, tags) {
if(err) console.log(err)
console.log(tags)
})
Brings users list from a Ghost Blog.
Client.users({}, function (err, users) {
if(err) console.log(err)
console.log(users)
})
If you want to add a parameter when you run a function, for example you want to use the limit parameter to limit the resources that you want to get, simply write them into the array before the callback.
// Example using the 'limit' parameter to get posts
Client.posts({ limit: 4 }, function (err, posts) {
if(err) console.log(err)
console.log(posts)
})
Copyright (c) 2015 - Miguel Ruiz
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
FAQs
A ghost client to get some data from the api
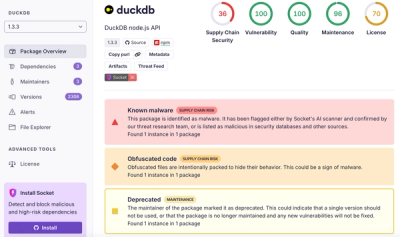
We found that ghost-client demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Research
/Security News
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.