
Security News
tea.xyz Spam Plagues npm and RubyGems Package Registries
Tea.xyz, a crypto project aimed at rewarding open source contributions, is once again facing backlash due to an influx of spam packages flooding public package registries.
node-red-contrib-meraki-cmx
Advanced tools
Readme
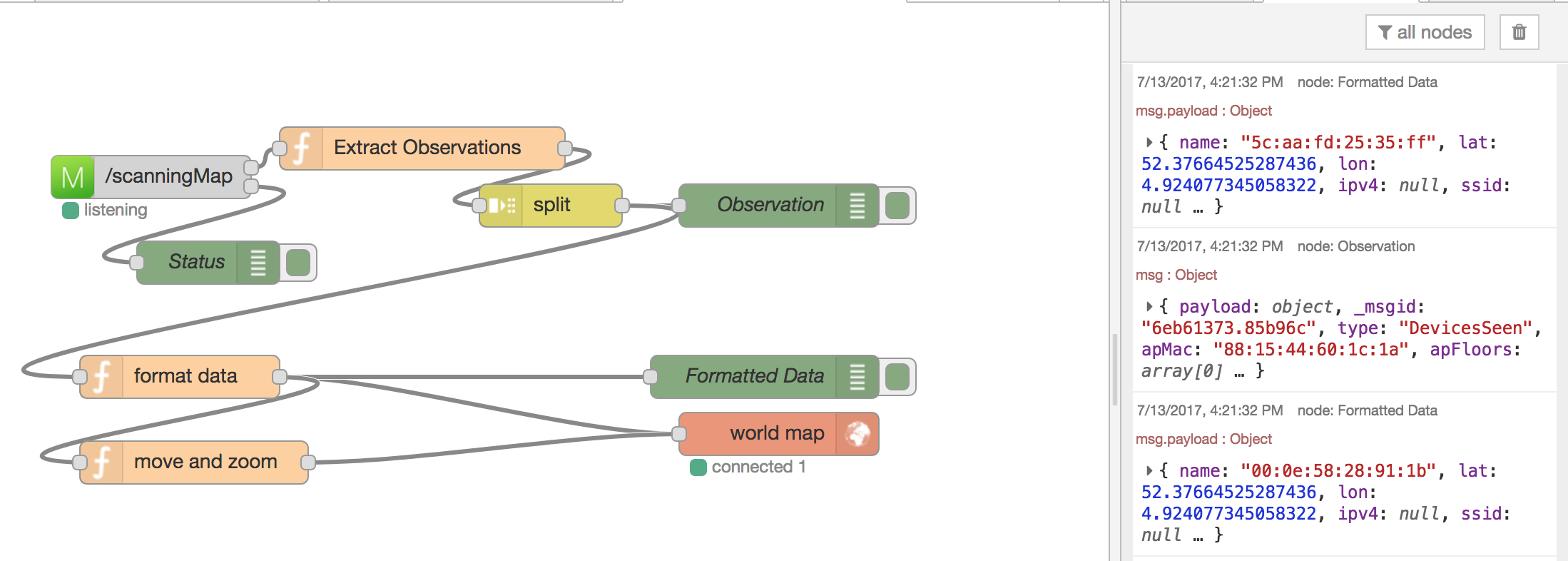
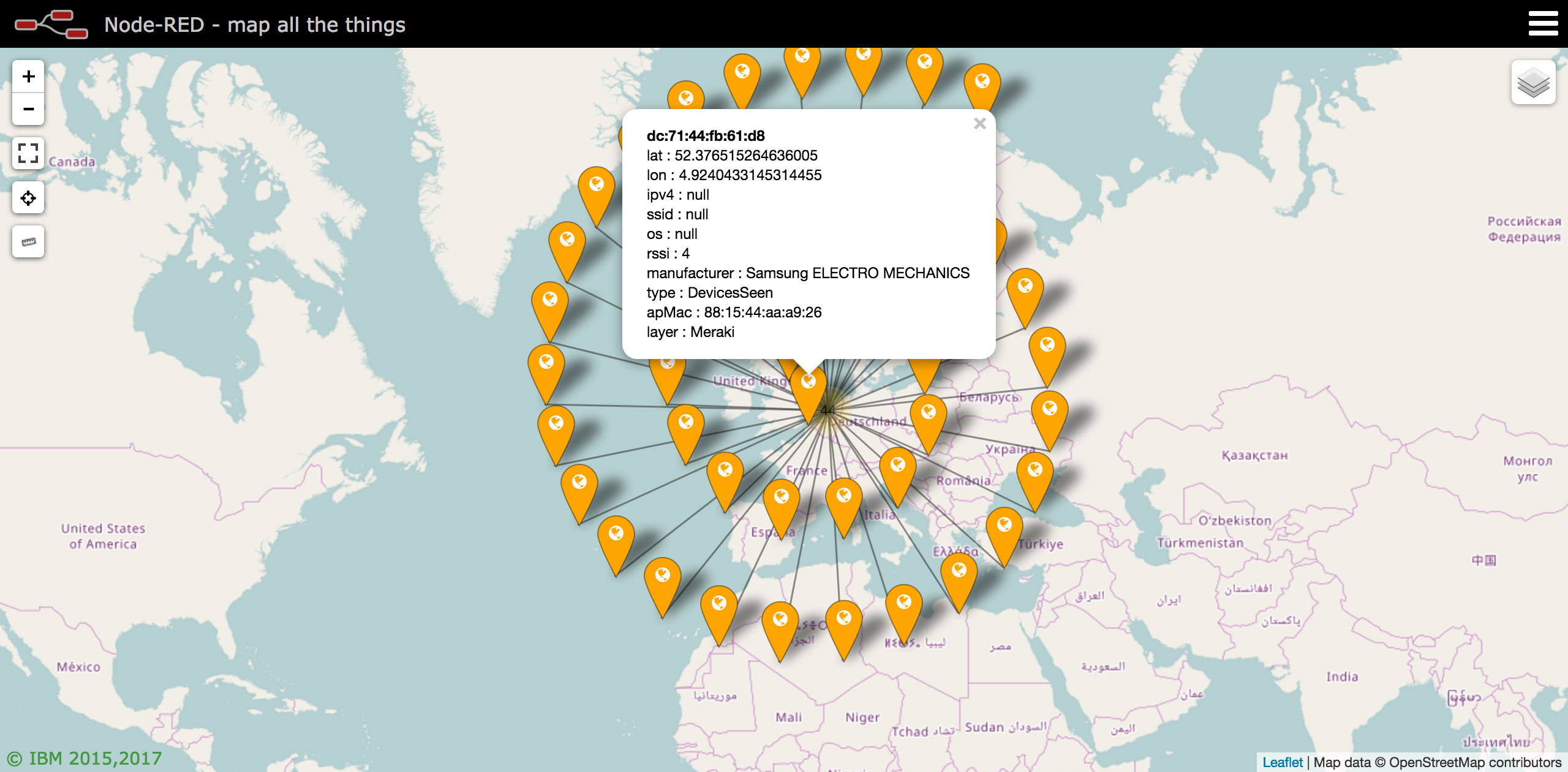
A Node-RED node to receive WiFi and Bluetooth beacon location data from a Cisco Meraki wireless network.
Run the following command in your Node-RED user directory - typically ~/.node-red
npm i node-red-contrib-meraki-cmx
Restart Node-RED
node-red
A Cisco Meraki Scanning API node to receive presence information from a Meraki WiFi network. Formely called CMX or Location API
Meraki WiFi access points will send their WiFi and Bluetooth beacon observations, via the Meraki cloud, to this node. The JSON stream will be available in the msg.payload object on the Data output.
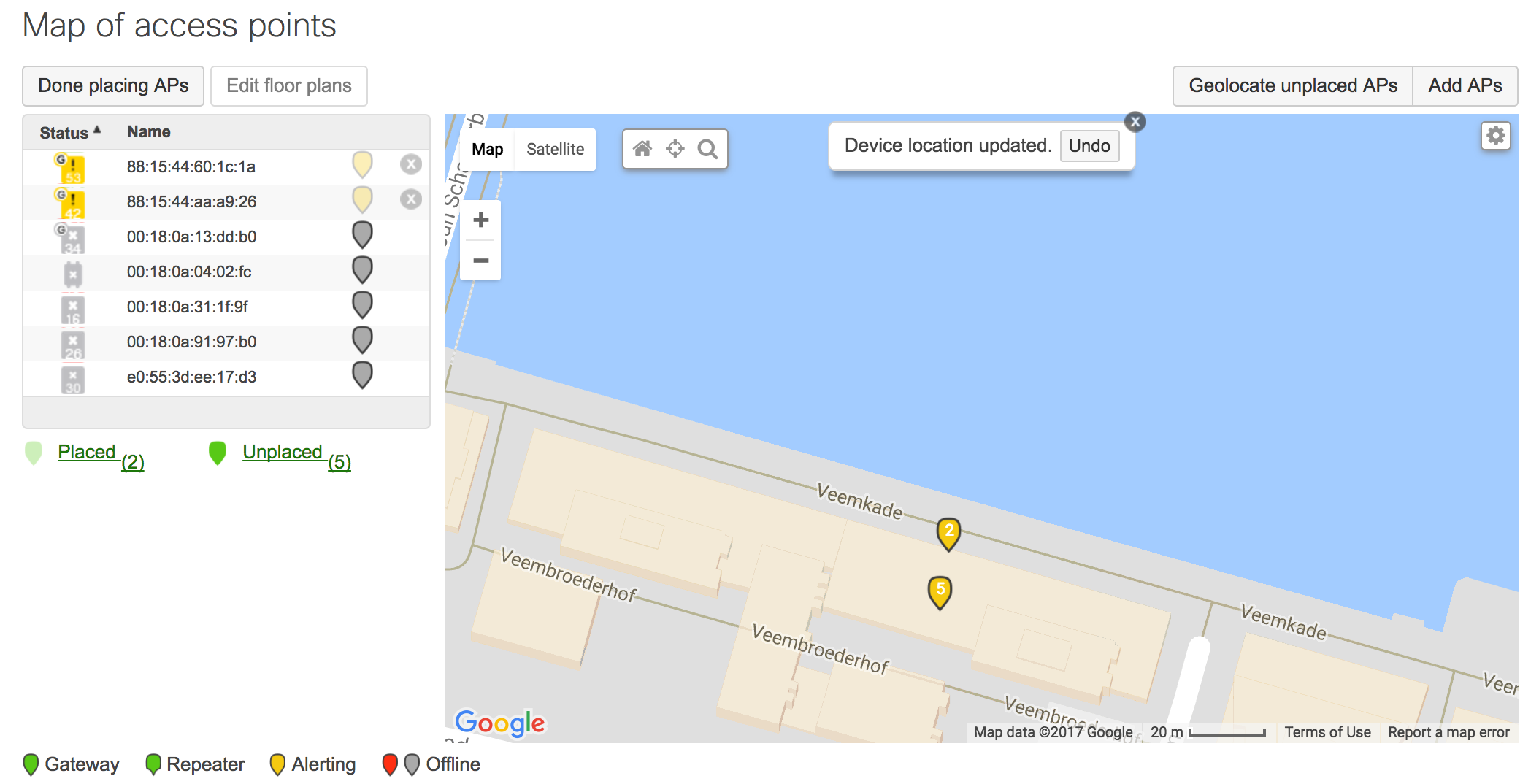
Note: The access points must be placed appropriately on the map in the Meraki Dashboard.
Sends the observation data
msg.payload
{
"version": "2.0",
"secret": "supersecret",
"type": "DevicesSeen",
"data": {
"apMac": "00:18:0a:13:dd:b0",
"apFloors": [],
"apTags": [
"dev",
"home",
"test"
],
"observations": [
{
"ipv4": "/192.168.0.56",
"location": {
"lat": 51.5355157,
...
Sends various topics depending on event status and additional parameters
{
topic: "type"
payload: "discarding radio type"
remoteAddress: "127.0.0.1"
_msgid: "913d6108.aadcf"
supportedType: "BluetoothDevicesSeen"
type: "DevicesSeen"
statusCode: 200
}
More information on the Scanning/CMX Location API can be found on the Meraki Developers Portal. http://developers.meraki.com/tagged/Location
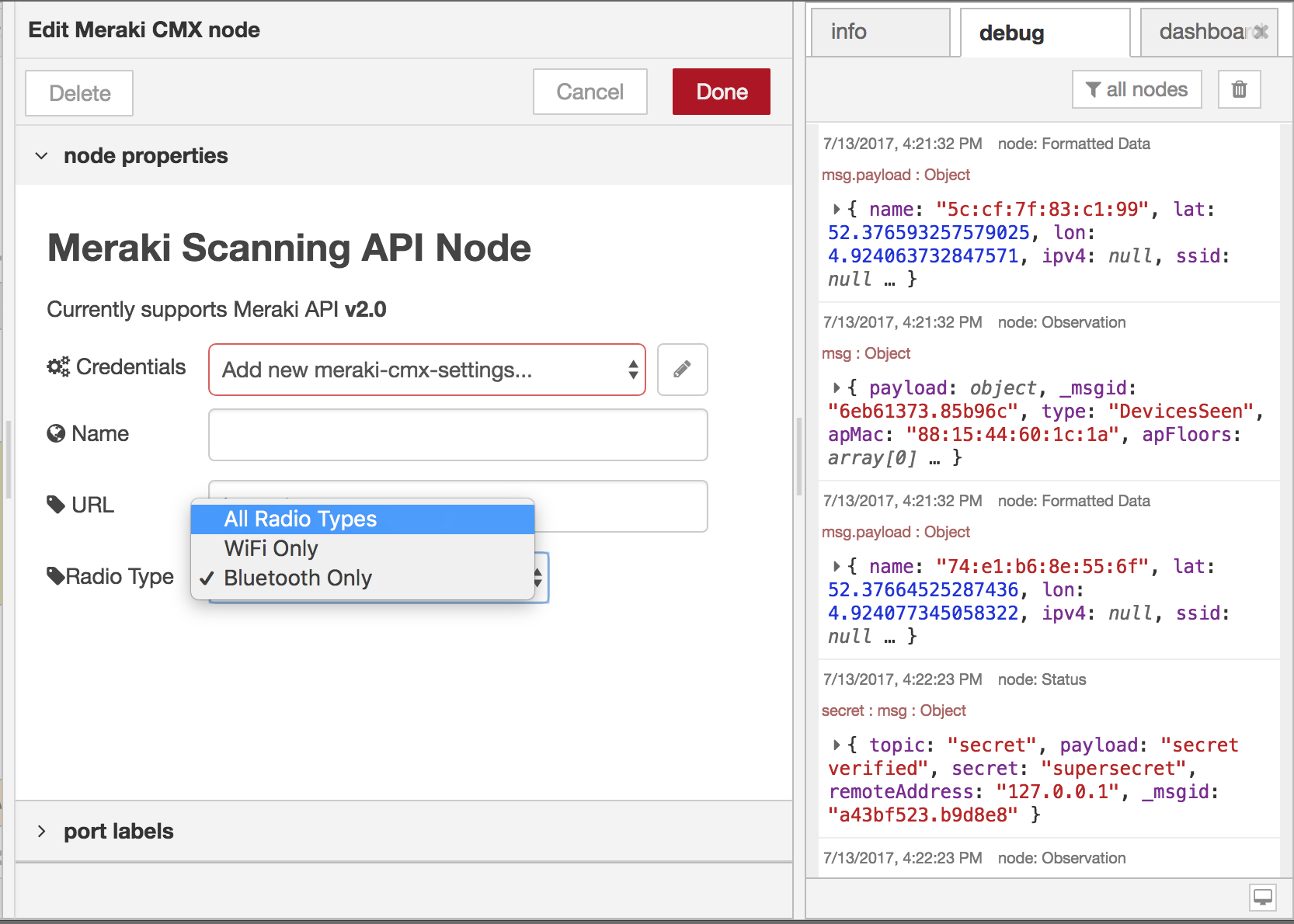
The Node requires the following configurations
http://yourserver:port/URLAugust 2017
msg objectJuly 2017
[{"id":"8d0a63e4.7ff19","type":"debug","z":"9560177e.d80b58","name":"Data","active":true,"console":"false","complete":"payload","x":510,"y":120,"wires":[]},{"id":"e6a6b005.01677","type":"Meraki CMX","z":"9560177e.d80b58","name":"","url":"/scanning","settings":"","radioType":"BluetoothDevicesSeen","x":100,"y":140,"wires":[["8d0a63e4.7ff19","23f1e4d9.3149ec"],["a303ae76.9149d"]]},{"id":"6b254578.dfd17c","type":"debug","z":"9560177e.d80b58","name":"Status: Data","active":true,"console":"false","complete":"true","x":490,"y":200,"wires":[]},{"id":"aa97b7a4.7e4b18","type":"split","z":"9560177e.d80b58","name":"","splt":"\\n","spltType":"str","arraySplt":1,"arraySpltType":"len","stream":false,"addname":"topic","x":330,"y":520,"wires":[["5700cec1.0367b"]]},{"id":"cb89fe11.4c4b5","type":"function","z":"9560177e.d80b58","name":"Extract Observations","func":"// Flatten JSON\nmsg.type = msg.payload.type;\nmsg.apMac = msg.payload.data.apMac;\nmsg.apFloors = msg.payload.data.apFloors\nmsg.apTags = msg.payload.data.apTags;\nmsg.payload = msg.payload.data.observations;\n\nreturn msg;","outputs":1,"noerr":0,"x":240,"y":480,"wires":[["aa97b7a4.7e4b18"]]},{"id":"5700cec1.0367b","type":"debug","z":"9560177e.d80b58","name":"Observation","active":true,"console":"false","complete":"true","x":490,"y":520,"wires":[]},{"id":"a303ae76.9149d","type":"switch","z":"9560177e.d80b58","name":"","property":"topic","propertyType":"msg","rules":[{"t":"eq","v":"data","vt":"str"},{"t":"eq","v":"version","vt":"str"},{"t":"eq","v":"validator","vt":"str"},{"t":"eq","v":"secret","vt":"str"},{"t":"eq","v":"type","vt":"str"},{"t":"eq","v":"error","vt":"str"},{"t":"else"}],"checkall":"true","outputs":7,"x":290,"y":300,"wires":[["6b254578.dfd17c"],["53f245f.0b2c2bc"],["5287b886.c827f8"],["4668f0fa.353d8"],["7946f407.72013c"],["adce6018.ce8af"],["4c7a8875.a90598"]]},{"id":"5287b886.c827f8","type":"debug","z":"9560177e.d80b58","name":"Status: Validator","active":true,"console":"false","complete":"true","x":480,"y":280,"wires":[]},{"id":"4668f0fa.353d8","type":"debug","z":"9560177e.d80b58","name":"Status: Secret","active":true,"console":"false","complete":"true","x":480,"y":320,"wires":[]},{"id":"7946f407.72013c","type":"debug","z":"9560177e.d80b58","name":"Status: Type","active":true,"console":"false","complete":"true","x":490,"y":360,"wires":[]},{"id":"adce6018.ce8af","type":"debug","z":"9560177e.d80b58","name":"Status: Error","active":true,"console":"false","complete":"true","x":490,"y":400,"wires":[]},{"id":"4c7a8875.a90598","type":"debug","z":"9560177e.d80b58","name":"Status: Otherwise","active":true,"console":"false","complete":"true","x":470,"y":440,"wires":[]},{"id":"23f1e4d9.3149ec","type":"link out","z":"9560177e.d80b58","name":"Meraki Scanning","links":["21b70a5e.6a00c6"],"x":275,"y":160,"wires":[]},{"id":"21b70a5e.6a00c6","type":"link in","z":"9560177e.d80b58","name":"Split Observations","links":["23f1e4d9.3149ec"],"x":60,"y":480,"wires":[["cb89fe11.4c4b5"]]},{"id":"ae4f659c.475398","type":"comment","z":"9560177e.d80b58","name":"Workflow Examples","info":"","x":120,"y":440,"wires":[]},{"id":"53f245f.0b2c2bc","type":"debug","z":"9560177e.d80b58","name":"Status: Version","active":true,"console":"false","complete":"true","x":480,"y":240,"wires":[]},{"id":"e7a18191.9674a","type":"comment","z":"9560177e.d80b58","name":"Meraki Scanning Node - README","info":"Update the Meraki node with your Meraki Network's\nvalidator and secret","x":410,"y":60,"wires":[]}]
FAQs
A Cisco Meraki Node-RED node to receive CMX data for location analytics with WiFi
The npm package node-red-contrib-meraki-cmx receives a total of 6 weekly downloads. As such, node-red-contrib-meraki-cmx popularity was classified as not popular.
We found that node-red-contrib-meraki-cmx demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Tea.xyz, a crypto project aimed at rewarding open source contributions, is once again facing backlash due to an influx of spam packages flooding public package registries.

Security News
As cyber threats become more autonomous, AI-powered defenses are crucial for businesses to stay ahead of attackers who can exploit software vulnerabilities at scale.

Security News
UnitedHealth Group disclosed that the ransomware attack on Change Healthcare compromised protected health information for millions in the U.S., with estimated costs to the company expected to reach $1 billion.