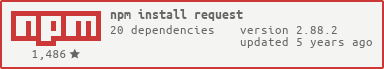
request - npm Package Compare versions
Comparing version 2.46.0 to 2.47.0
@@ -101,4 +101,4 @@ // Copyright 2010-2012 Mikeal Rogers | ||
| request.jar = function () { | ||
| return cookies.jar() | ||
| request.jar = function (store) { | ||
| return cookies.jar(store) | ||
| } | ||
@@ -105,0 +105,0 @@ |
@@ -16,5 +16,2 @@ 'use strict' | ||
| } | ||
| if (!Cookie) { | ||
| return null | ||
| } | ||
| return Cookie.parse(str) | ||
@@ -24,5 +21,5 @@ } | ||
| // Adapt the sometimes-Async api of tough.CookieJar to our requirements | ||
| function RequestJar() { | ||
| function RequestJar(store) { | ||
| var self = this | ||
| self._jar = new CookieJar() | ||
| self._jar = new CookieJar(store) | ||
| } | ||
@@ -42,12 +39,4 @@ RequestJar.prototype.setCookie = function(cookieOrStr, uri, options) { | ||
| exports.jar = function() { | ||
| if (!CookieJar) { | ||
| // tough-cookie not loaded, return a stub object: | ||
| return { | ||
| setCookie: function(){}, | ||
| getCookieString: function(){}, | ||
| getCookies: function(){} | ||
| } | ||
| } | ||
| return new RequestJar() | ||
| exports.jar = function(store) { | ||
| return new RequestJar(store) | ||
| } |
@@ -10,10 +10,10 @@ { | ||
| ], | ||
| "version": "2.46.0", | ||
| "version": "2.47.0", | ||
| "author": "Mikeal Rogers <mikeal.rogers@gmail.com>", | ||
| "repository": { | ||
| "type": "git", | ||
| "url": "https://github.com/mikeal/request.git" | ||
| "url": "https://github.com/request/request.git" | ||
| }, | ||
| "bugs": { | ||
| "url": "http://github.com/mikeal/request/issues" | ||
| "url": "http://github.com/request/request/issues" | ||
| }, | ||
@@ -33,3 +33,3 @@ "license": "Apache-2.0", | ||
| "node-uuid": "~1.4.0", | ||
| "qs": "~1.2.0", | ||
| "qs": "~2.3.1", | ||
| "tunnel-agent": "~0.4.0", | ||
@@ -41,3 +41,4 @@ "tough-cookie": ">=0.12.0", | ||
| "aws-sign2": "~0.5.0", | ||
| "stringstream": "~0.0.4" | ||
| "stringstream": "~0.0.4", | ||
| "combined-stream": "~0.0.5" | ||
| }, | ||
@@ -44,0 +45,0 @@ "scripts": { |
| # Request — Simplified HTTP client | ||
| [](https://gitter.im/mikeal/request?utm_source=badge&utm_medium=badge&utm_campaign=pr-badge&utm_content=badge) | ||
| [](https://nodei.co/npm/request/) | ||
| [](https://gitter.im/request/request?utm_source=badge&utm_medium=badge&utm_campaign=pr-badge&utm_content=badge) | ||
| ## Super simple to use | ||
@@ -150,2 +150,5 @@ | ||
| You can also set the `proxyHeaderExclusiveList` to share certain | ||
| headers only with the proxy and not with destination host. | ||
| By default, this set is: | ||
@@ -181,5 +184,4 @@ | ||
| Note that, when using a tunneling proxy, the `proxy-authorization` | ||
| header is *never* sent to the endpoint server, but only to the proxy | ||
| server. All other headers are sent as-is over the established | ||
| connection. | ||
| header and any headers from custom `proxyHeaderExclusiveList` are | ||
| *never* sent to the endpoint server, but only to the proxy server. | ||
@@ -411,3 +413,3 @@ ### Controlling proxy behaviour using environment variables | ||
| var options = { | ||
| url: 'https://api.github.com/repos/mikeal/request', | ||
| url: 'https://api.github.com/repos/request/request', | ||
| headers: { | ||
@@ -515,2 +517,4 @@ 'User-Agent': 'request' | ||
| tunneling proxy. | ||
| * `proxyHeaderExclusiveList` - A whitelist of headers to send | ||
| exclusively to a tunneling proxy and not to destination. | ||
@@ -602,3 +606,3 @@ | ||
| ``` | ||
| ### request.jar | ||
| ### request.jar() | ||
@@ -692,3 +696,2 @@ Function that creates a new cookie jar. | ||
| ```javascript | ||
| // `npm install --save tough-cookie` before this works | ||
| var j = request.jar(); | ||
@@ -703,5 +706,26 @@ var cookie = request.cookie('key1=value1'); | ||
| To inspect your cookie jar after a request | ||
| To use a custom cookie store (such as a | ||
| [`FileCookieStore`](https://github.com/mitsuru/tough-cookie-filestore) | ||
| which supports saving to and restoring from JSON files), pass it as a parameter | ||
| to `request.jar()`: | ||
| ```javascript | ||
| var FileCookieStore = require('tough-cookie-filestore'); | ||
| // NOTE - currently the 'cookies.json' file must already exist! | ||
| var j = request.jar(new FileCookieStore('cookies.json')); | ||
| request = request.defaults({ jar : j }) | ||
| request('http://www.google.com', function() { | ||
| request('http://images.google.com') | ||
| }) | ||
| ``` | ||
| The cookie store must be a | ||
| [`tough-cookie`](https://github.com/goinstant/tough-cookie) | ||
| store and it must support synchronous operations; see the | ||
| [`CookieStore` API docs](https://github.com/goinstant/tough-cookie/#cookiestore-api) | ||
| for details. | ||
| To inspect your cookie jar after a request: | ||
| ```javascript | ||
| var j = request.jar() | ||
@@ -708,0 +732,0 @@ request({url: 'http://www.google.com', jar: j}, function () { |
141
request.js
@@ -28,2 +28,3 @@ 'use strict' | ||
| , net = require('net') | ||
| , CombinedStream = require('combined-stream') | ||
@@ -60,3 +61,2 @@ var safeStringify = helpers.safeStringify | ||
| 'pragma', | ||
| 'proxy-authorization', | ||
| 'referer', | ||
@@ -69,2 +69,6 @@ 'te', | ||
| var defaultProxyHeaderExclusiveList = [ | ||
| 'proxy-authorization' | ||
| ] | ||
| function filterForNonReserved(reserved, options) { | ||
@@ -117,5 +121,11 @@ // Filter out properties that are not reserved. | ||
| function constructProxyHeaderWhiteList(headers, proxyHeaderWhiteList) { | ||
| var whiteList = proxyHeaderWhiteList | ||
| .reduce(function (set, header) { | ||
| set[header] = true | ||
| return set | ||
| }, {}) | ||
| return Object.keys(headers) | ||
| .filter(function (header) { | ||
| return proxyHeaderWhiteList.indexOf(header.toLowerCase()) !== -1 | ||
| return whiteList[header.toLowerCase()] | ||
| }) | ||
@@ -130,13 +140,3 @@ .reduce(function (set, header) { | ||
| var proxy = request.proxy | ||
| var proxyHeaders = request.proxyHeaders | ||
| var proxyAuth | ||
| if (proxy.auth) { | ||
| proxyAuth = proxy.auth | ||
| } | ||
| if (!proxy.auth && request.proxyAuthorization) { | ||
| proxyHeaders['Proxy-Authorization'] = request.proxyAuthorization | ||
| } | ||
| var tunnelOptions = { | ||
@@ -146,4 +146,4 @@ proxy: { | ||
| port: +proxy.port, | ||
| proxyAuth: proxyAuth, | ||
| headers: proxyHeaders | ||
| proxyAuth: proxy.auth, | ||
| headers: request.proxyHeaders | ||
| }, | ||
@@ -312,2 +312,12 @@ rejectUnauthorized: request.rejectUnauthorized, | ||
| // Always include `defaultProxyHeaderExclusiveList` | ||
| if (!self.proxyHeaderExclusiveList) { | ||
| self.proxyHeaderExclusiveList = [] | ||
| } | ||
| var proxyHeaderExclusiveList = self.proxyHeaderExclusiveList.concat(defaultProxyHeaderExclusiveList) | ||
| // Treat `proxyHeaderExclusiveList` as part of `proxyHeaderWhiteList` | ||
| if (!self.proxyHeaderWhiteList) { | ||
@@ -317,6 +327,10 @@ self.proxyHeaderWhiteList = defaultProxyHeaderWhiteList | ||
| var proxyHeaderWhiteList = self.proxyHeaderWhiteList.concat(proxyHeaderExclusiveList) | ||
| var proxyHost = constructProxyHost(self.uri) | ||
| self.proxyHeaders = constructProxyHeaderWhiteList(self.headers, self.proxyHeaderWhiteList) | ||
| self.proxyHeaders = constructProxyHeaderWhiteList(self.headers, proxyHeaderWhiteList) | ||
| self.proxyHeaders.host = proxyHost | ||
| proxyHeaderExclusiveList.forEach(self.removeHeader, self) | ||
| var tunnelFn = getTunnelFn(self) | ||
@@ -342,8 +356,2 @@ var tunnelOptions = construcTunnelOptions(self) | ||
| // Never send proxy-auth to the endpoint! | ||
| if (self.hasHeader('proxy-authorization')) { | ||
| self.proxyAuthorization = self.getHeader('proxy-authorization') | ||
| self.removeHeader('proxy-authorization') | ||
| } | ||
| if (!self.method) { | ||
@@ -459,7 +467,8 @@ self.method = options.method || 'GET' | ||
| if (!self.hasHeader('host')) { | ||
| self.setHeader('host', self.uri.hostname) | ||
| var hostHeaderName = self.originalHostHeaderName || 'host' | ||
| self.setHeader(hostHeaderName, self.uri.hostname) | ||
| if (self.uri.port) { | ||
| if ( !(self.uri.port === 80 && self.uri.protocol === 'http:') && | ||
| !(self.uri.port === 443 && self.uri.protocol === 'https:') ) { | ||
| self.setHeader('host', self.getHeader('host') + (':' + self.uri.port) ) | ||
| self.setHeader(hostHeaderName, self.getHeader('host') + (':' + self.uri.port) ) | ||
| } | ||
@@ -569,13 +578,8 @@ } | ||
| if (self.proxy && !self.tunnel) { | ||
| if (self.proxy.auth && !self.proxyAuthorization) { | ||
| var proxyAuthPieces = self.proxy.auth.split(':').map(function(item){ | ||
| return querystring.unescape(item) | ||
| }) | ||
| var authHeader = 'Basic ' + toBase64(proxyAuthPieces.join(':')) | ||
| self.proxyAuthorization = authHeader | ||
| } | ||
| if (self.proxyAuthorization) { | ||
| self.setHeader('proxy-authorization', self.proxyAuthorization) | ||
| } | ||
| if (!self.tunnel && self.proxy && self.proxy.auth && !self.hasHeader('proxy-authorization')) { | ||
| var proxyAuthPieces = self.proxy.auth.split(':').map(function(item){ | ||
| return querystring.unescape(item) | ||
| }) | ||
| var authHeader = 'Basic ' + toBase64(proxyAuthPieces.join(':')) | ||
| self.setHeader('proxy-authorization', authHeader) | ||
| } | ||
@@ -648,11 +652,3 @@ | ||
| } else { | ||
| self.agent = self.agent || self.getAgent() | ||
| if (self.maxSockets) { | ||
| // Don't use our pooling if node has the refactored client | ||
| self.agent.maxSockets = self.maxSockets | ||
| } | ||
| if (self.pool.maxSockets) { | ||
| // Don't use our pooling if node has the refactored client | ||
| self.agent.maxSockets = self.pool.maxSockets | ||
| } | ||
| self.agent = self.agent || self.getNewAgent() | ||
| } | ||
@@ -699,10 +695,7 @@ | ||
| } | ||
| if (self._multipart) { | ||
| self._multipart.pipe(self) | ||
| } | ||
| if (self.body) { | ||
| if (Array.isArray(self.body)) { | ||
| self.body.forEach(function (part) { | ||
| self.write(part) | ||
| }) | ||
| } else { | ||
| self.write(self.body) | ||
| } | ||
| self.write(self.body) | ||
| self.end() | ||
@@ -769,3 +762,3 @@ } else if (self.requestBodyStream) { | ||
| if (self.agent) { | ||
| self.agent = self.getAgent() | ||
| self.agent = self.getNewAgent() | ||
| } | ||
@@ -791,3 +784,3 @@ | ||
| self.agent = null | ||
| self.agent = self.getAgent() | ||
| self.agent = self.getNewAgent() | ||
| } | ||
@@ -797,3 +790,3 @@ } | ||
| Request.prototype.getAgent = function () { | ||
| Request.prototype.getNewAgent = function () { | ||
| var self = this | ||
@@ -835,12 +828,2 @@ var Agent = self.agentClass | ||
| if (!self.httpModule.globalAgent) { | ||
| // node 0.4.x | ||
| options.host = self.host | ||
| options.port = self.port | ||
| if (poolKey) { | ||
| poolKey += ':' | ||
| } | ||
| poolKey += self.host + ':' + self.port | ||
| } | ||
| // ca option is only relevant if proxy or destination are https | ||
@@ -905,2 +888,6 @@ var proxy = self.proxy | ||
| self.pool[poolKey] = new Agent(options) | ||
| // properly set maxSockets on new agents | ||
| if (self.pool.maxSockets) { | ||
| self.pool[poolKey].maxSockets = self.pool.maxSockets | ||
| } | ||
| } | ||
@@ -1036,4 +1023,9 @@ | ||
| // Save the original host before any redirect (if it changes, we need to | ||
| // remove any authorization headers) | ||
| self.originalHost = self.headers.host | ||
| // remove any authorization headers). Also remember the case of the header | ||
| // name because lots of broken servers expect Host instead of host and we | ||
| // want the caller to be able to specify this. | ||
| self.originalHost = self.getHeader('host') | ||
| if (!self.originalHostHeaderName) { | ||
| self.originalHostHeaderName = self.hasHeader('host') | ||
| } | ||
| if (self.setHost) { | ||
@@ -1443,3 +1435,3 @@ self.removeHeader('host') | ||
| var self = this | ||
| self.body = [] | ||
| self._multipart = new CombinedStream() | ||
@@ -1458,3 +1450,3 @@ if (!self.hasHeader('content-type')) { | ||
| if (self.preambleCRLF) { | ||
| self.body.push(new Buffer('\r\n')) | ||
| self._multipart.append('\r\n') | ||
| } | ||
@@ -1467,16 +1459,16 @@ | ||
| } | ||
| delete part.body | ||
| var preamble = '--' + self.boundary + '\r\n' | ||
| Object.keys(part).forEach(function (key) { | ||
| if (key === 'body') { return } | ||
| preamble += key + ': ' + part[key] + '\r\n' | ||
| }) | ||
| preamble += '\r\n' | ||
| self.body.push(new Buffer(preamble)) | ||
| self.body.push(new Buffer(body)) | ||
| self.body.push(new Buffer('\r\n')) | ||
| self._multipart.append(preamble) | ||
| self._multipart.append(body) | ||
| self._multipart.append('\r\n') | ||
| }) | ||
| self.body.push(new Buffer('--' + self.boundary + '--')) | ||
| self._multipart.append('--' + self.boundary + '--') | ||
| if (self.postambleCRLF) { | ||
| self.body.push(new Buffer('\r\n')) | ||
| self._multipart.append('\r\n') | ||
| } | ||
@@ -1761,2 +1753,5 @@ | ||
| Request.defaultProxyHeaderExclusiveList = | ||
| defaultProxyHeaderExclusiveList.slice() | ||
| // Exports | ||
@@ -1763,0 +1758,0 @@ |
Sorry, the diff of this file is too big to display
Sorry, the diff of this file is not supported yet
New alerts
License Policy Violation
LicenseThis package is not allowed per your license policy. Review the package's license to ensure compliance.
Found 1 instance in 1 package
Fixed alerts
License Policy Violation
LicenseThis package is not allowed per your license policy. Review the package's license to ensure compliance.
Found 1 instance in 1 package
Improved metrics
- Number of lines in readme file
- increased by3.33%
744
Worsened metrics
- Total package byte prevSize
- decreased by-39.21%
137086
- Dependency count
- increased by6.67%
16
- Lines of code
- decreased by-1.16%
1791
Dependency changes
+ Addedcombined-stream@~0.0.5
+ Addedqs@2.3.3(transitive)
- Removedqs@1.2.2(transitive)
Updatedqs@~2.3.1