
Product
Introducing License Enforcement in Socket
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
Deploy utility for AWS Serverless Application Model (SAM) based projects that significantly speeds up time to deploy updates when the only change is the code of Lambda function and the rest of the stack is the same.
It builds upon aws cloudformation package but will figure out if simply updating code of Lambda functions or updating stack parameters is enough or whether a full aws cloudformation deploy is required.
Install this package globally.
npm install -g sampic
Generate a sample config file for your current git working branch:
cd <project_directory>
sampic init
Make sure you have AWS CLI (version >= 1.11) and git installed and available in the shell environment when running sampic.
Make sure your current working branch is the branch to deploy and simply run the sampic command from your project base directory. Note that changes saved but not yet committed will be bundled in the deployment.
sampic [<options>] [<command>] [<command-options>]
The utility supports the following set of commands:
| Command | Description |
|---|---|
deps-install | Parses your CloudFormation template file (see configuration below) looking for resources of type AWS::Serverless::Function whose runtime is a version of nodejs and CodeUri isn't an s3 url. For each of these functions, it will execute npm install --production in the directory CodeUri points to. |
deps-outdated | Lists outdated npm packages for all nodejs functions found in your CLoudFormation template |
deps-update | Parses your CloudFormation template file (see configuration below) looking for resources of type AWS::Serverless::Function whose runtime is a version of nodejs and CodeUri isn't an s3 url. For each of these functions, it will execute npm update --save in the directory CodeUri points to. |
| Command | Description |
|---|---|
deploy-local | Packages your CloudFormation template using the aws cloudformation package command then deploys it to AWS. If the stack doesn't exist yet, it will create it. If changes since the last deployment only impact lambda function code, it will skip a full CloudFormation deploy and simply update lambda functions code (which is much faster). |
deploy | Bundles git HEAD commit and uploads it to your sampic.cloud account for remote build and deploy. Your Lambda code bundles are always built from dependencies listed in package-lock.json or package.json and installed within an Amazon Linux environment replicating the Lambda exection environment. |
logs | Get detailed logs from a deploy triggered with the deploy command |
signup | Creates your sampic.cloud account required for deploy and logs command to work |
| Command | Description |
|---|---|
help | Launches a bunch of flares pretty high up in the sky to signal you're in distress. |
init | Creates a sample .sampic/config.json file in the present directory (unless it already exists). |
Create a .sampic directory at the base of your project and add a config.json file under it. CloudFormation templates packaged by the aws cloudformation package will also go under this directory. It is a good idea to add it to your .gitignore.
The configuration file declares deployment parameters for git branches you want to deploy. For example, the config file defines deployment instructions when your working branch is master or my-dev-branch:
{
"master": {
"profile": "default",
"region": "us-east-1",
"template": "app.yaml",
"stackName": "my-staging-stack",
"stackParameters": {
"ParameterKey1": "ParameterValue1",
"ParameterKey2": "ParameterValue2"
},
"s3Bucket": "lambdafns-staging",
"capabilities": ["CAPABILITY_IAM"]
},
"my-dev-branch": {
"profile": "default",
"region": "us-east-1",
"template": "app.yaml",
"stackName": "my-dev-stack",
"s3Bucket": "lambdafns-dev",
"capabilities": ["CAPABILITY_IAM"]
}
}
profile (optional) refers to a named profile under ~/.aws/credentials. No need to define this if you'll use the default AWS profileregion is the AWS region your CloudFormation stack is deployed intemplate is your SAM template filestackName is the name of the CloudFormation stack this branch should be deployed tostackParameters (optional) passed as template parameters when deploying the template to CloudFormations3Bucket is the bucket where artifacts (lambda function code, external swagger files, ...) are uploaded tocapabilities is used when running to the aws cloudformation deploy command. See AWS docs for more but usually, deploying SAM templates need at least CAPABILITY_IAM listed in there.If your application has more than one template deployed to different stacks, sampic supports that but the configuration is a bit different.
{
"master": {
"profile": "default",
"region": "us-east-1",
"stacks": {
"myStackA": {
"template": "stackA-template.yaml",
"name": "stack-A"
},
"myStackB": {
"template": "stackB-template.yaml",
"name": "stack-A",
"parameters": {
"ParameterKey1": "ParameterValue1",
"ParameterKey2": "ParameterValue2"
}
}
},
"s3Bucket": "lambdafns-staging",
"capabilities": ["CAPABILITY_IAM"]
}
}
Once you're config is set up with a <branch>.stacks option, commands parsing your CloudFormation template will list stack names and ask you which template you want to work with:
$ sampic deploy
Using config for current git branch: master
Which stack?
(1) stackA-template.yaml => stack-A
(2) stackB-template.yaml => stack-B
Specify stack number:
Alternatively, you can use the stack key (<branch>.stacks.<key>) from CLI to skip the prompt:
$ sampic deploy --stack myStackA
deploy-localThe script goes through the following steps:
.sampic/config.jsonaws cloudformation package. The output template file is saved as .sampic/<STACK_NAME>-packaged-template.yamlaws cloudformation update-stack using the current template and specifying new parameter values.aws cloudformation deploy to do a full stack update..sampic/<STACK_NAME>-packaged-template.yaml as .sampic/<STACK_NAME>-deployed-template.yaml and we're done.FAQs
[DEPRECATED] Package is now named 'sampic'
The npm package sampique receives a total of 0 weekly downloads. As such, sampique popularity was classified as not popular.
We found that sampique demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
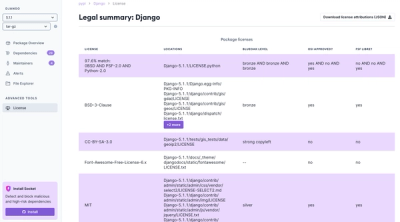
Product
We're launching a new set of license analysis and compliance features for analyzing, managing, and complying with licenses across a range of supported languages and ecosystems.
Product
We're excited to introduce Socket Optimize, a powerful CLI command to secure open source dependencies with tested, optimized package overrides.