Product
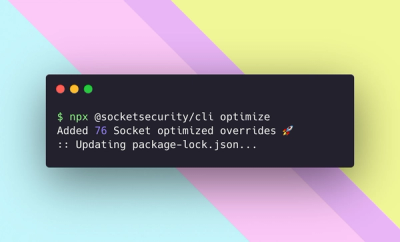
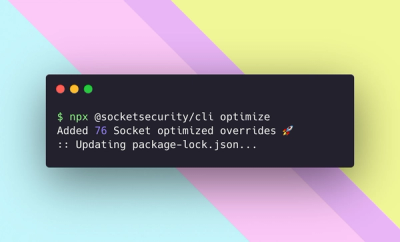
Introducing Socket Optimize
We're excited to introduce Socket Optimize, a powerful CLI command to secure open source dependencies with tested, optimized package overrides.
A Javascript implementation of the SHA-2 cryptographic hash function family.
This Javascript module implements the SHA-2 (Secure Hash Algorithm 2) cryptographic hash function family designed by the United States National Security Agency (NSA) ― SHA-224, SHA-256, SHA-384, SHA-512, and SHA-512/t (including SHA-512/224 and SHA-512/256).
It makes use of the crypto standard built-in module if the module is available, otherwise, an alternative Javascript implementation for SHA-2 that I developed is used.
npm install sha2
Note that this module works with Buffers. As for web browsers that don't have Buffers, you may use SHA2.js for web browsers instead.
Import the module with
const SHA2 = require("sha2");
or if you want to take its methods only,
const {SHA256, SHA384} = require("sha2");
Choose your preferred naming convention!
const SHA2 = require("sha2");
const input = "Was touwaka ga knawa murfanare yor.";
// SHA-224
console.log(SHA2["SHA-224"](input));
console.log(SHA2.SHA_224(input));
console.log(SHA2.SHA224(input));
console.log(SHA2["sha-224"](input));
console.log(SHA2.sha_224(input));
console.log(SHA2.sha224(input));
// All of them give `<Buffer 0a 88 43 df 34 dd a2 45 be 30
// b6 36 65 8b d2 a1 08 7d 17 23 6e fd d8 8e cb 70 c0 08>`.
// SHA-512/80
console.log(SHA2["SHA-512/t"](80, input));
console.log(SHA2.SHA_512_t(80, input));
console.log(SHA2.SHA512_t(80, input));
console.log(SHA2.SHA_512t(80, input));
console.log(SHA2.SHA512t(80, input));
console.log(SHA2["sha-512/t"](80, input));
console.log(SHA2.sha_512_t(80, input));
console.log(SHA2.sha512_t(80, input));
console.log(SHA2.sha_512t(80, input));
console.log(SHA2.sha512t(80, input));
// All of them give `<Buffer de 24 91 60 e0 1c a5 a0 01 ef>`.
They basically take a Buffer. Everything other than a Buffer as their input turns into a Buffer with Buffer.from() internally. Reading these would help you understand it:
Buffer.from(string[, encoding])Buffer.from(arrayBuffer[, byteOffset[, length]])Buffer.from(array)Buffer.from(object[, offsetOrEncoding[, length]])// SHA-384
const {SHA384} = require("sha2");
// Input: "Green chá" in UTF-8.
console.log(SHA384("Green chá"));
console.log(SHA384("Green chá", "utf8"));
console.log(SHA384("477265656e206368c3A1", "hex"));
console.log(SHA384("R3JlZW4gY2jDoQ==", "base64"));
console.log(SHA384([
0x47, 0x72, 0x65, 0x65, 0x6E, 0x20, 0x63, 0x68, 0xC3, 0xA1
]));
// All of them give `<Buffer 63 f2 63 3f f2 bc 1e 24 77 76
// 12 9b 76 97 66 0a 70 13 34 7f 8b ad e2 e5 c1 2c 5a e8 e0
// 53 13 e5 9e 7b 74 84 68 c9 ba ab 37 8f 79 5b 03 42 85 c2>`.
// Input: 0xC0FFEE.
console.log(SHA384(Buffer.from([0xC0, 0xFF, 0xEE])));
console.log(SHA384((new Uint8Array([0xC0, 0xFF, 0xEE])).buffer));
console.log(SHA384(
(new Uint8Array([0xC0, 0x01, 0xC0, 0xFF, 0xEE])).buffer,
2
));
console.log(SHA384("C0ffee", "hex"));
console.log(SHA384("wP/u", "base64"));
console.log(SHA384([0xC0, 0xFF, 0xEE]));
// All of them give `<Buffer 01 1f 36 0d b6 36 cf a4 c7 a6
// 17 68 ad 91 7f e3 d9 5a 6b d8 8a 79 68 ce 43 7b 00 b6 3a
// 32 b0 da 91 13 29 48 8b 85 71 22 4e 42 45 25 0b 62 ba 86>`.
They return a Buffer, so you can do what you can do with a Buffer.
// SHA-256
const {SHA256} = require("sha2");
const nyanbuffer = SHA256(`
░░░░░░░▄▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▄░░░░░░
░░░░░░█░░▄▀▀▀▀▀▀▀▀▀▀▀▀▀▄░░█░░░░░
░░░░░░█░█░▀░░░░░▀░░▀░░░░█░█░░░░░
░░░░░░█░█░░░░░░░░▄▀▀▄░▀░█░█▄▀▀▄░
█▀▀█▄░█░█░░▀░░░░░█░░░▀▄▄█▄▀░░░█░
▀▄▄░▀██░█▄░▀░░░▄▄▀░░░░░░░░░░░░▀▄
░░▀█▄▄█░█░░░░▄░░█░░░▄█░░░▄░▄█░░█
░░░░░▀█░▀▄▀░░░░░█░██░▄░░▄░░▄░███
░░░░░▄█▄░░▀▀▀▀▀▀▀▀▄░░▀▀▀▀▀▀▀░▄▀░
░░░░█░░▄█▀█▀▀█▀▀▀▀▀▀█▀▀█▀█▀▀█░░░
░░░░▀▀▀▀░░▀▀▀░░░░░░░░▀▀▀░░▀▀░░░░
`);
// <Buffer 91 7a f1 59 e6 a8 7a 2b 3d 3c d1 6c d5 f1 a7
// 89 b7 ec 90 07 75 ad d0 52 16 73 05 d3 97 e9 85 f2>
console.log(nyanbuffer.toString("hex"));
// "917af159e6a87a2b3d3cd16cd5f1a789b7ec900775add052167305d397e985f2"
console.log(nyanbuffer.toString("base64"));
// "kXrxWeaoeis9PNFs1fGnibfskAd1rdBSFnMF05fphfI="
console.log(Array.from(nyanbuffer));
// [145, 122, 241, 89, 230, 168, 122, 43, 61, 60, 209,
// 108, 213, 241, 167, 137, 183, 236, 144, 7, 117, 173,
// 208, 82, 22, 115, 5, 211, 151, 233, 133, 242]
console.log(nyanbuffer.equals(nyanbuffer));
// true
SHA2["SHA-224"](......)SHA2.SHA_224(......)SHA2.SHA224(......)SHA2["sha-224"](......)SHA2.sha_224(......)SHA2.sha224(......)SHA2["SHA-256"](......)SHA2["SHA-384"](......)SHA2["SHA-512"](......)SHA2["SHA-512/t"](t, ......)SHA2.SHA_512_t(t, ......)SHA2.SHA512_t(t, ......)SHA2.SHA_512t(t, ......)SHA2.SHA512t(t, ......)SHA2["sha-512/t"](t, ......)SHA2.sha_512_t(t, ......)SHA2.sha512_t(t, ......)SHA2.sha_512t(t, ......)SHA2.sha512t(t, ......)SHA2["SHA-512/224"](......)SHA2["SHA-512/256"](......)Making a hash of a password with one of the algorithms of the SHA-2 family and keeping it, is not recommended. For that purpose, use slow hash functions which are slow by design such as PBKDF2, bcrypt, and scrypt, instead.
This module is not appropriate for hashing huge binary data, such as that of a 1 GB file.
written by Donald E. Eastlake 3rd, and Tony Hansen in May 2011.
published by National Institute of Standards and Technology (NIST) in August 2015.
This Javascript module has been licensed under the MIT license:
// 80
////////////////////////////////////////////////////////////////////////////////
/*
SHA2.js
(A Javascript implementation of
the United States of America (USA)
Federal Information Processing Standard (FIPS)
Secure Hash Algorithm 2 (SHA-2))
developed
by K. (https://github.com/wlzla000)
on January 16-22 and 26, 2018,
licensed under
the MIT license
Copyright (c) 2018 K.
Permission is hereby granted, free of charge, to any person
obtaining a copy of this software and associated documentation
files (the "Software"), to deal in the Software without
restriction, including without limitation the rights to use,
copy, modify, merge, publish, distribute, sublicense, and/or
sell copies of the Software, and to permit persons to whom the
Software is furnished to do so, subject to the following
conditions:
The above copyright notice and this permission notice shall be
included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND,
EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES
OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND
NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT
HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY,
WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING
FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR
OTHER DEALINGS IN THE SOFTWARE.
*/
////////////////////////////////////////////////////////////////////////////////
/*
SHA2-Node.js
(A Node.js module implementation of
the United States of America (USA)
Federal Information Processing Standard (FIPS)
Secure Hash Algorithm 2 (SHA-2))
developed
by K. (https://github.com/wlzla000)
on January 23-26, 2018,
licensed under
the MIT license
Copyright (c) 2018 K.
Permission is hereby granted, free of charge, to any person
obtaining a copy of this software and associated documentation
files (the "Software"), to deal in the Software without
restriction, including without limitation the rights to use,
copy, modify, merge, publish, distribute, sublicense, and/or
sell copies of the Software, and to permit persons to whom the
Software is furnished to do so, subject to the following
conditions:
The above copyright notice and this permission notice shall be
included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND,
EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES
OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND
NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT
HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY,
WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING
FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR
OTHER DEALINGS IN THE SOFTWARE.
*/
, and its dependency crypto also has the MIT license.
Thank you for providing a great piece of music for programming, Nick Kaelar and Team Salvato!
FAQs
A Javascript implementation of the SHA-2 cryptographic hash function family.
The npm package sha2 receives a total of 0 weekly downloads. As such, sha2 popularity was classified as not popular.
We found that sha2 demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
We're excited to introduce Socket Optimize, a powerful CLI command to secure open source dependencies with tested, optimized package overrides.

Product
We're excited to announce that Socket now supports the Java programming language.

Security News
Socket detected a malicious Python package impersonating a popular browser cookie library to steal passwords, screenshots, webcam images, and Discord tokens.