
Product
Introducing Rust Support in Socket
Socket now supports Rust and Cargo, offering package search for all users and experimental SBOM generation for enterprise projects.
🔒 Unified API for PASsword Hashing algorithms
Coded with ❤️ by Simone Primarosa.
Password breaches have become more and more frequent.
See: Yahoo (twice), LinkedIn, Adobe,
Ashley Madison, and a whole lot more.
Indeed, the above examples doubles as a list of "how NOT to do password storage": simple hashing, unsalted values, misuse of encryption, and failed password migration. (For more information on why these are bad, see our introduction to password hashing theory)
There are two possible interpretations here: first, companies do not put adequate resources in securing passwords; and secondly, getting password hashing right is hard. Furthermore, even if you have followed previous best practice, keeping it right is another technical challenge: algorithm choices, security levels, parameter selection change regularly.

The upash (pronounced u-pash) project aims is to allow you to have a clean and easy-to-use API to use any password hashing algorithm seamlessly in your application.
Do you believe that this is useful? Has it saved you time? Or maybe you simply like it?
If so, support my work with a Star ⭐️.
The upash solution is straight-forward but it is important to follow all the steps carefully.
Firstly, you need to install this package.
npm install --save upash
Then, you need to choose from the
list of supported password hashing algorithms
the one that best suits your needs and install that too.
In the following, we will assume that you choose @phc/argon2, that is also a
suitable solution in case you don't know which one fits better for you.
npm install --save @phc/argon2
Finally, you can enjoy the easy APIs.
const upash = require('upash');
// Install the algorithm of your choice.
upash.install('argon2', require('@phc/argon2'));
// Hash API
const hashstr = await upash.hash('password');
// => "$argon2id$v=19$m=4096,t=3,p=1$PcEZHj1maR/+ZQynyJHWZg$2jEN4xcww7CYp1jakZB1rxbYsZ55XH2HgjYRtdZtubI"
// Verify API
const match = await upash.verify(hashstr, 'password');
// => true
You can store the hash returned by the hash function directly into your database.
You can also install more than one algorithm at once.
This is really handy when you want to update your current password hashing
algorithm.
const upash = require('upash');
// Install the algorithms of your choice.
upash.install('pbkdf2', require('@phc/pbkdf2'));
upash.install('argon2', require('@phc/argon2'));
// You can explicitly tell upash which algorithm to use.
const hashstr_pbkdf2 = await upash.use('pbkdf2').hash('password');
// => "$pbkdf2-sha512$i=10000$O484sW7giRw+nt5WVnp15w$jEUMVZ9adB+63ko/8Dr9oB1jWdndpVVQ65xRlT+tA1GTKcJ7BWlTjdaiILzZAhIPEtgTImKvbgnu8TS/ZrjKgA"
// If you don't do so it will automatically use the last one installed.
const hashstr_argon2 = await upash.hash('password');
// => "$argon2i$v=19$m=4096,t=3,p=1$mTFYKhlcxmjS/v6Y8aEd5g$IKGY+vj0MdezVEKHQ9bvjpROoR5HPun5/AUCjQrHSIs"
// When you verify upash will automatically choose the algorithm to use based
// on the identifier contained in the hash string.
const match_pbkdf2 = await upash.verify(hashstr_pbkdf2, 'password');
// => true
// This will allow you to easily migrate from an algorithm to another.
const match_argon2 = await upash.verify(hashstr_argon2, 'password');
// => true
The following is a curated list of algorithms that adhere to the upash APIs
guidelines and are ready to work at a production level straight out of the box.
All the functions come pre-configured but fine-tuning is always a good practice.
The defaults are maintained by the community and the aim of this project is also
to bring together experts to be able to provide you reasonably secure default
configurations.
Want your package listed here? Open an issue and we will review it.

Generally, each function allows configuration of 'work factors’. Underlying mechanisms used to achieve irreversibility and govern work factors (such as time, space, and parallelism) vary between functions.
You want to adjust the work factor to keep pace with threats' increasing hardware capabilities so as to impede attackers while providing acceptable user experience and scale.
A common rule of thumb for tuning the work factor (or cost) is to make the function run as slow as possible without affecting the users' experience and without increasing the need for extra hardware over budget.
The CLI lets you hash and verify password directly from your terminal.
You can use it to test work, memory and parallelism parameters on different
machines.
For installation and usage information about the CLI, see the upash-cli page.
If you are not building a new application, chances are high that you have
already implemented some hash/verify logic for your passwords.
The migration guide provides some good guidance on how
to accomplish an upgrade in place without adversely affecting existing user
accounts and future proofing your upgrade so you can seamlessly upgrade again
(which you eventually will need to do).
Please if you do not find a migration documentation that fits your case, open an issue.
Upgrading the hashing algorithm used to hash passwords inside your application can be a really painful operation if not done well. You should take a lot of attention in order to not adversely affect existing user accounts.
This article is a nice start that should give you some ideas on what are the problems related to that process.
Example of implementations can be found in the upgrade algorithm guide.
Installs a compatible password hashing function.
Uninstalls a password hashing function previously installed.
Array.<string>Gets the list of the installed password hashing functions.
ObjectSelects manually which password hashing function to use. You can call hash and verify on the object returned.
string | nullReturns the name of the algorithm that has generated the hash string.
Promise.<boolean>Determines whether or not the hash provided matches the hash generated for the given password choosing the right algorithm based on the identifier contained in the hash.
Promise.<string>Computes the hash string of the given password using the 'last' algorithm installed.
Installs a compatible password hashing function.
Kind: global function
Access: public
| Param | Type | Description |
|---|---|---|
| name | string | The name of the password hashing function. |
| algorithm | Object | The password hashing function object. |
| algorithm.hash | function | A function that takes a password and returns a cryptographically secure password hash string. |
| algorithm.verify | function | A function that takes a secure password hash string and a password and returns whether or not the password is valid for the given hash string. |
| algorithm.identifiers | function | A function that returns the list of identifiers that this password hashing algorithm is able to generate / verify. |
Uninstalls a password hashing function previously installed.
Kind: global function
Access: public
| Param | Type | Description |
|---|---|---|
| name | string | The name of the algorithm to uninstall or 'last' to uninstall the last one installed. |
Array.<string>Gets the list of the installed password hashing functions.
Kind: global function
Returns: Array.<string> - The array of the available password hashing
functions.
Access: public
ObjectSelects manually which password hashing function to use. You can call hash and verify on the object returned.
Kind: global function
Returns: Object - The password hashing function object.
Access: public
| Param | Type | Description |
|---|---|---|
| name | string | undefined | The name of the algorithm to use. |
string | nullReturns the name of the algorithm that has generated the hash string.
Kind: global function
Returns: string | null - The name of password hashing algorithm.
Access: public
| Param | Type | Description |
|---|---|---|
| hashstr | string | Secure hash string generated from this package. |
Promise.<boolean>Determines whether or not the hash provided matches the hash generated for the given password choosing the right algorithm based on the identifier contained in the hash.
Kind: global function
Returns: Promise.<boolean> - A boolean that is true if the hash computed
for the password matches.
Access: public
| Param | Type | Description |
|---|---|---|
| hashstr | string | Secure hash string generated from this package. |
| password | string | User's password input. |
Promise.<string>Computes the hash string of the given password using the 'last' algorithm installed.
Kind: global function
Returns: Promise.<string> - The generated secure hash string.
Access: public
| Param | Type | Description |
|---|---|---|
| password | string | The password to hash. |
| [options] | Object | Optional configurations related to the hashing function. See the algorithm specific documentation for the options supported. |
Contributions are REALLY welcome and if you find a security flaw in this code, PLEASE report it.
See also the list of contributors who participated in this project.
This project is licensed under the MIT License - see the license file for details.
FAQs
Unified API for password hashing algorithms
The npm package upash receives a total of 1,469 weekly downloads. As such, upash popularity was classified as popular.
We found that upash demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket now supports Rust and Cargo, offering package search for all users and experimental SBOM generation for enterprise projects.
Product
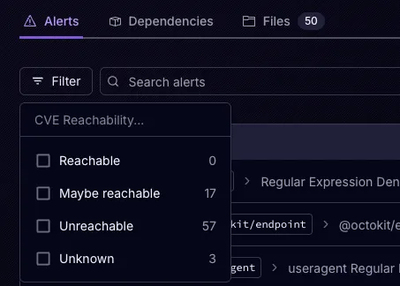
Socket’s precomputed reachability slashes false positives by flagging up to 80% of vulnerabilities as irrelevant, with no setup and instant results.

Product
Socket is launching experimental protection for Chrome extensions, scanning for malware and risky permissions to prevent silent supply chain attacks.