
Product
Introducing Tier 1 Reachability: Precision CVE Triage for Enterprise Teams
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
MABWiser (IJAIT 2021, ICTAI 2019) is a research library written in Python for rapid prototyping of multi-armed bandit algorithms. It supports context-free, parametric and non-parametric contextual bandit models and provides built-in parallelization for both training and testing components.
The library also provides a simulation utility for comparing different policies and performing hyper-parameter tuning. MABWiser follows a scikit-learn style public interface, adheres to PEP-8 standards, and is tested heavily.
MABWiser is developed by the Artificial Intelligence Center of Excellence at Fidelity Investments. Documentation is available at fidelity.github.io/mabwiser.
To solve personalized recommendation problems, MABWiser is integrated into our Mab2Rec library. Mab2Rec enables building content- and context-aware recommender systems, whereby MABWiser helps selecting the next best item (arm).
To solve combinatorial optimization problems, MABWiser is integrated into Adaptive Large Neighborhood Search. The ALNS library enables building metaheuristics for complex optimization problems, whereby MABWiser helps selecting the next best destroy, repair operation (arm).
# An example that shows how to use the UCB1 learning policy
# to choose between two arms based on their expected rewards.
# Import MABWiser Library
from mabwiser.mab import MAB, LearningPolicy, NeighborhoodPolicy
# Data
arms = ['Arm1', 'Arm2']
decisions = ['Arm1', 'Arm1', 'Arm2', 'Arm1']
rewards = [20, 17, 25, 9]
# Model
mab = MAB(arms, LearningPolicy.UCB1(alpha=1.25))
# Train
mab.fit(decisions, rewards)
# Test
mab.predict()
Available Learning Policies:
Available Neighborhood Policies:
MABWiser requires Python 3.8+ and can be installed from PyPI using pip install mabwiser or by building from source as shown in installation instructions.
Please submit bug reports and feature requests as Issues.
If you use MABWiser in a publication, please cite it as:
@article{DBLP:journals/ijait/StrongKK21,
author = {Emily Strong and Bernard Kleynhans and Serdar Kadioglu},
title = {{MABWiser:} Parallelizable Contextual Multi-armed Bandits},
journal = {Int. J. Artif. Intell. Tools},
volume = {30},
number = {4},
pages = {2150021:1--2150021:19},
year = {2021},
url = {https://doi.org/10.1142/S0218213021500214},
doi = {10.1142/S0218213021500214},
}
@inproceedings{DBLP:conf/ictai/StrongKK19,
author = {Emily Strong and Bernard Kleynhans and Serdar Kadioglu},
title = {MABWiser: {A} Parallelizable Contextual Multi-Armed Bandit Library for Python},
booktitle = {31st {IEEE} International Conference on Tools with Artificial Intelligence, {ICTAI} 2019, Portland, OR, USA, November 4-6, 2019},
pages = {909--914},
publisher = {{IEEE}},
year = {2019},
url = {https://doi.org/10.1109/ICTAI.2019.00129},
doi = {10.1109/ICTAI.2019.00129},
}
MABWiser is licensed under the Apache License 2.0.
FAQs
MABWiser: Parallelizable Contextual Multi-Armed Bandits Library
We found that mabwiser demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 5 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket’s new Tier 1 Reachability filters out up to 80% of irrelevant CVEs, so security teams can focus on the vulnerabilities that matter.
Research
/Security News
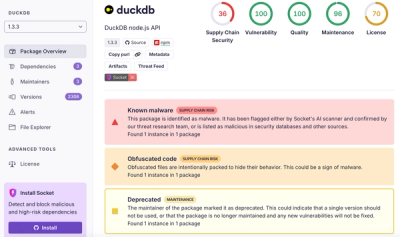
Ongoing npm supply chain attack spreads to DuckDB: multiple packages compromised with the same wallet-drainer malware.

Security News
The MCP Steering Committee has launched the official MCP Registry in preview, a central hub for discovering and publishing MCP servers.