
Product
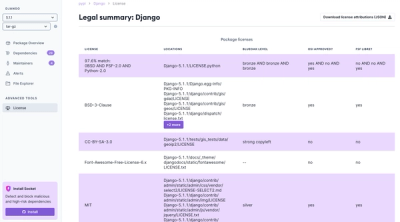
Introducing License Enforcement in Socket
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
Ever needed to test an SSO setup but don't have access to the IDP for whatever reason?
Mock IDP provides a SAML2.0 IDP using POST bindings without need for a user database or complicated enterprise software setup.
Mock-idp requires python 3.6 and pip
Install and run mock-idp using Pip:
$ pip3 install mock-idp
$ mock-idp
...
To override the system configuration create a config file. The service loads config files in the following order:
mockidp.yaml in the current working directory~/.mockidp.yaml in your home directory/etc/mockidp.yaml in the global config directoryHere is a sample (copy of built-in config) file to start with:
service_providers:
- name: "local:service:author"
response_url: "http://localhost:3000/saml_login"
users:
charlie:
first_name: "Charlie"
last_name: "Brown"
email: "charlie@gmail.com"
password: snoopy
linus:
first_name: "Linus"
last_name: "van Pelt"
email: "linus@gmail.com"
password: pumpkin
lucy:
password: charlie
first_name: "Lucy"
last_name: "van Pelt"
email: "lucy@gmail.com"
peppermint:
first_name: "Peppermint"
last_name: "Patty"
email: "peppermint@gmail.com"
password: peppermint
For each service provider (client) that uses the identity provider, an entry in the service providers section of the config is needed. It has two values:
service_providers:
- name: "local:aem:author"
response_url: "http://localhost:14502/saml_login"
Users is a fairly self explanatory list of user credentials recognized by the IDP:
users:
charlie:
first_name: "Charlie"
last_name: "Brown"
email: "charlie@gmail.com"
password: snoopy
roles:
- administrators
To generate a service provider Certificate, run the following commands:
$ openssl genrsa -out saml.pem 2048
$ openssl req -new -key saml.pem -out saml.csr
$ openssl x509 -req -days 365 -in saml.csr -signkey saml.pem -out saml.crt
This will produce three files:
Refer to your service provider documentation on how to install the certificate.
To run the base config just start the service and map port 5000
$ docker run -p 5000:5000 bjornskoglund/mock-idp:0.4.0
Provided you have produced your config file containing service providers and user account information. You can inject into a docker container by the following:
$ docker run -p 5000:5000 -v <absolute path to your config>.yaml:/usr/local/mock-idp/mockidp.yaml bjornskoglund/mock-idp
Copy the cert/cert.pem file into your Service Provider (SP), and be sure that the ISSUER (entity id) provided by the SP matches the name: of the Service Provider in your config.
Install pipenv with pip to handle dependencies
$ pip3 install pipenv
then install environment
$ pipenv install
Run from source:
$ PYTHONPATH=. pipenv run bin/mock-idp
...
All system config is located in mockidp/resources/default_config.yaml.
Mock-IDP has been tested with the following service providers
FAQs
Mock SAML 2.0 Identity Provider
We found that mock-idp demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 1 open source maintainer collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
Product
We're launching a new set of license analysis and compliance features for analyzing, managing, and complying with licenses across a range of supported languages and ecosystems.
Product
We're excited to introduce Socket Optimize, a powerful CLI command to secure open source dependencies with tested, optimized package overrides.