
Security News
Maven Central Adds Sigstore Signature Validation
Maven Central now validates Sigstore signatures, making it easier for developers to verify the provenance of Java packages.
github.com/plutov/paypal/v4
Get started with PayPal REST APIs
It is possible that some endpoints are missing in this client, but you can use built-in paypal functions to perform a request: NewClient -> NewRequest -> SendWithAuth
import "github.com/plutov/paypal/v4"
// Create a client instance
c, err := paypal.NewClient("clientID", "secretID", paypal.APIBaseSandBox)
c.SetLog(os.Stdout) // Set log to terminal stdout
auth, err := c.GetAuthorization("2DC87612EK520411B")
capture, err := c.CaptureAuthorization(authID, &paypal.Amount{Total: "7.00", Currency: "USD"}, true)
auth, err := c.VoidAuthorization(authID)
auth, err := c.ReauthorizeAuthorization(authID, &paypal.Amount{Total: "7.00", Currency: "USD"})
refund, err := c.GetRefund("O-4J082351X3132253H")
order, err := c.GetOrder("O-4J082351X3132253H")
ctx := context.Background()
units := []paypal.PurchaseUnitRequest{}
source := &paypal.PaymentSource{}
appCtx := &paypal.ApplicationContext{}
order, err := c.CreateOrder(ctx, paypal.OrderIntentCapture, units, ource, appCtx)
order, err := c.UpdateOrder("O-4J082351X3132253H", []paypal.PurchaseUnitRequest{})
auth, err := c.AuthorizeOrder(orderID, paypal.AuthorizeOrderRequest{})
capture, err := c.CaptureOrder(orderID, paypal.CaptureOrderRequest{})
token, err := c.GrantNewAccessTokenFromAuthCode("<Authorization-Code>", "http://example.com/myapp/return.php")
// ... or by refresh token
token, err := c.GrantNewAccessTokenFromRefreshToken("<Refresh-Token>")
userInfo, err := c.GetUserInfo("openid")
payout := paypal.Payout{
SenderBatchHeader: &paypal.SenderBatchHeader{
EmailSubject: "Subject will be displayed on PayPal",
},
Items: []paypal.PayoutItem{
paypal.PayoutItem{
RecipientType: "EMAIL",
Receiver: "single-email-payout@mail.com",
Amount: &paypal.AmountPayout{
Value: "15.11",
Currency: "USD",
},
Note: "Optional note",
SenderItemID: "Optional Item ID",
},
},
}
payoutResp, err := c.CreatePayout(payout)
payout, err := c.GetPayout("PayoutBatchID")
payoutItem, err := c.GetPayoutItem("PayoutItemID")
payoutItem, err := c.CancelPayoutItem("PayoutItemID")
webprofile := WebProfile{
Name: "YeowZa! T-Shirt Shop",
Presentation: Presentation{
BrandName: "YeowZa! Paypal",
LogoImage: "http://www.yeowza.com",
LocaleCode: "US",
},
InputFields: InputFields{
AllowNote: true,
NoShipping: NoShippingDisplay,
AddressOverride: AddrOverrideFromCall,
},
FlowConfig: FlowConfig{
LandingPageType: LandingPageTypeBilling,
BankTXNPendingURL: "http://www.yeowza.com",
},
}
result, err := c.CreateWebProfile(webprofile)
webprofile, err := c.GetWebProfile("XP-CP6S-W9DY-96H8-MVN2")
webprofiles, err := c.GetWebProfiles()
webprofile := WebProfile{
ID: "XP-CP6S-W9DY-96H8-MVN2",
Name: "Shop YeowZa! YeowZa! ",
}
err := c.SetWebProfile(webprofile)
err := c.DeleteWebProfile("XP-CP6S-W9DY-96H8-MVN2")
// Store CC
c.StoreCreditCard(paypal.CreditCard{
Number: "4417119669820331",
Type: "visa",
ExpireMonth: "11",
ExpireYear: "2020",
CVV2: "874",
FirstName: "Foo",
LastName: "Bar",
})
// Delete it
c.DeleteCreditCard("CARD-ID-123")
// Edit it
c.PatchCreditCard("CARD-ID-123", []paypal.CreditCardField{
paypal.CreditCardField{
Operation: "replace",
Path: "/billing_address/line1",
Value: "New value",
},
})
// Get it
c.GetCreditCard("CARD-ID-123")
// Get all stored credit cards
c.GetCreditCards(nil)
// Create a webhook
c.CreateWebhook(paypal.CreateWebhookRequest{
URL: "webhook URL",
EventTypes: []paypal.WebhookEventType{
paypal.WebhookEventType{
Name: "PAYMENT.AUTHORIZATION.CREATED",
},
},
})
// Update a registered webhook
c.UpdateWebhook("WebhookID", []paypal.WebhookField{
paypal.WebhookField{
Operation: "replace",
Path: "/event_types",
Value: []interface{}{
map[string]interface{}{
"name": "PAYMENT.SALE.REFUNDED",
},
},
},
})
// Get a registered webhook
c.GetWebhook("WebhookID")
// Delete a webhook
c.DeleteWebhook("WebhookID")
// List registered webhooks
c.ListWebhooks(paypal.AncorTypeApplication)
// GenerateInvoiceNumber: generates the next invoice number that is available to the merchant.
c.GenerateInvoiceNumber(ctx) // might return something like "0001" or "0010".
// the second argument is an ID, it should be valid
invoice, err := c.GetInvoiceDetails(ctx, "INV2-XFXV-YW42-ZANU-4F33")
for now, we are yet to implement the ShowAllInvoices endpoint, so use the following cURL request for the same(this gives you the list of invoice-IDs for this customer)
curl -v -X GET https://api-m.sandbox.paypal.com/v2/invoicing/invoices?total_required=true \
-H "Content-Type: application/json" \
-H "Authorization: Bearer <Token>"
refer to the beginning of this Usage section for obtaining a Token.
Main contributors:
go test -v ./...
FAQs
Unknown package
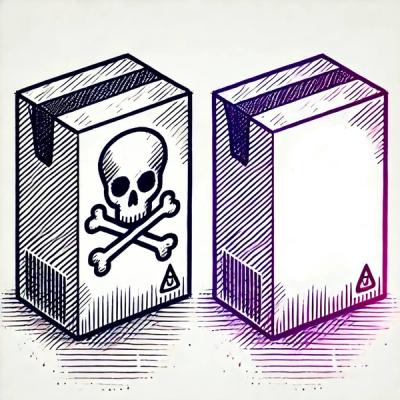
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
Maven Central now validates Sigstore signatures, making it easier for developers to verify the provenance of Java packages.

Security News
CISOs are racing to adopt AI for cybersecurity, but hurdles in budgets and governance may leave some falling behind in the fight against cyber threats.
Research
Security News
Socket researchers uncovered a backdoored typosquat of BoltDB in the Go ecosystem, exploiting Go Module Proxy caching to persist undetected for years.