
Product
Introducing Ruby Support in Socket
Socket is launching Ruby support for all users. Enhance your Rails projects with AI-powered security scans for vulnerabilities and supply chain threats. Now in Beta!
@aws-cdk/aws-iam
Advanced tools
CDK routines for easily assigning correct and minimal IAM permissions
@aws-cdk/aws-iam is an AWS Cloud Development Kit (CDK) library that allows you to define AWS Identity and Access Management (IAM) resources in your CDK applications. This package provides constructs for creating and managing IAM roles, users, policies, and groups, enabling you to manage permissions and access control in your AWS environment programmatically.
Create IAM Role
This code sample demonstrates how to create an IAM role that can be assumed by EC2 instances and has read-only access to Amazon S3.
const iam = require('@aws-cdk/aws-iam');
const cdk = require('@aws-cdk/core');
class MyStack extends cdk.Stack {
constructor(scope, id, props) {
super(scope, id, props);
new iam.Role(this, 'MyRole', {
assumedBy: new iam.ServicePrincipal('ec2.amazonaws.com'),
managedPolicies: [
iam.ManagedPolicy.fromAwsManagedPolicyName('AmazonS3ReadOnlyAccess')
]
});
}
}
const app = new cdk.App();
new MyStack(app, 'MyStack');Create IAM User
This code sample demonstrates how to create an IAM user with administrator access.
const iam = require('@aws-cdk/aws-iam');
const cdk = require('@aws-cdk/core');
class MyStack extends cdk.Stack {
constructor(scope, id, props) {
super(scope, id, props);
new iam.User(this, 'MyUser', {
userName: 'my-user',
managedPolicies: [
iam.ManagedPolicy.fromAwsManagedPolicyName('AdministratorAccess')
]
});
}
}
const app = new cdk.App();
new MyStack(app, 'MyStack');Attach Inline Policy to Role
This code sample demonstrates how to create an IAM role and attach an inline policy that allows listing objects in a specific S3 bucket.
const iam = require('@aws-cdk/aws-iam');
const cdk = require('@aws-cdk/core');
class MyStack extends cdk.Stack {
constructor(scope, id, props) {
super(scope, id, props);
const role = new iam.Role(this, 'MyRole', {
assumedBy: new iam.ServicePrincipal('lambda.amazonaws.com')
});
role.addToPolicy(new iam.PolicyStatement({
actions: ['s3:ListBucket'],
resources: ['arn:aws:s3:::my-bucket']
}));
}
}
const app = new cdk.App();
new MyStack(app, 'MyStack');The aws-sdk package is the official AWS SDK for JavaScript, which allows you to interact with AWS services, including IAM, using JavaScript. Unlike @aws-cdk/aws-iam, which is used for defining and deploying AWS infrastructure, aws-sdk is used for making API calls to AWS services.
The serverless framework is a toolkit for deploying and operating serverless architectures, including AWS Lambda functions and associated IAM roles and policies. It provides a higher-level abstraction compared to @aws-cdk/aws-iam and is focused on serverless applications.
Terraform is an open-source infrastructure as code software tool that provides a consistent CLI workflow to manage hundreds of cloud services, including AWS IAM. It is similar to @aws-cdk/aws-iam in that it allows you to define and manage AWS infrastructure, but it is not limited to AWS and supports multiple cloud providers.
This is a developer preview (public beta) module. Releases might lack important features and might have future breaking changes.
This API is still under active development and subject to non-backward compatible changes or removal in any future version. Use of the API is not recommended in production environments. Experimental APIs are not subject to the Semantic Versioning model.
Define a role and add permissions to it. This will automatically create and attach an IAM policy to the role:
Define a policy and attach it to groups, users and roles. Note that it is possible to attach
the policy either by calling xxx.attachInlinePolicy(policy) or policy.attachToXxx(xxx).
attaching policies to user and group
Managed policies can be attached using xxx.attachManagedPolicy(arn):
Many of the AWS CDK resources have grant* methods that allow you to grant other resources access to that resource. As an example, the following code gives a Lambda function write permissions (Put, Update, Delete) to a DynamoDB table.
const fn = new lambda.Function(...);
const table = new dynamodb.Table(...);
table.grantWriteData(fn);
The more generic grant method allows you to give specific permissions to a resource:
const fn = new lambda.Function(...);
const table = new dynamodb.Table(...);
table.grant(fn, 'dynamodb:PutItem');
The grant* methods accept an IGrantable object. This interface is implemented by IAM principles resources (groups, users and roles) and resources that assume a role such as a Lambda function, EC2 instance or a Codebuild project.
You can find which grant* methods exist for a resource in the AWS CDK API Reference.
If you need to create roles that will be assumed by 3rd parties, it is generally a good idea to require an ExternalId
to assume them. Configuring
an ExternalId works like this:
When we say Principal, we mean an entity you grant permissions to. This
entity can be an AWS Service, a Role, or something more abstract such as "all
users in this account" or even "all users in this organization". An
Identity is an IAM representing a single IAM entity that can have
a policy attached, one of Role, User, or Group.
When defining policy statements as part of an AssumeRole policy or as part of a
resource policy, statements would usually refer to a specific IAM principal
under Principal.
IAM principals are modeled as classes that derive from the iam.PolicyPrincipal
abstract class. Principal objects include principal type (string) and value
(array of string), optional set of conditions and the action that this principal
requires when it is used in an assume role policy document.
To add a principal to a policy statement you can either use the abstract
statement.addPrincipal, one of the concrete addXxxPrincipal methods:
addAwsPrincipal, addArnPrincipal or new ArnPrincipal(arn) for { "AWS": arn }addAwsAccountPrincipal or new AccountPrincipal(accountId) for { "AWS": account-arn }addServicePrincipal or new ServicePrincipal(service) for { "Service": service }addAccountRootPrincipal or new AccountRootPrincipal() for { "AWS": { "Ref: "AWS::AccountId" } }addCanonicalUserPrincipal or new CanonicalUserPrincipal(id) for { "CanonicalUser": id }addFederatedPrincipal or new FederatedPrincipal(federated, conditions, assumeAction) for
{ "Federated": arn } and a set of optional conditions and the assume role action to use.addAnyPrincipal or new AnyPrincipal for { "AWS": "*" }If multiple principals are added to the policy statement, they will be merged together:
const statement = new PolicyStatement();
statement.addServicePrincipal('cloudwatch.amazonaws.com');
statement.addServicePrincipal('ec2.amazonaws.com');
statement.addArnPrincipal('arn:aws:boom:boom');
Will result in:
{
"Principal": {
"Service": [ "cloudwatch.amazonaws.com", "ec2.amazonaws.com" ],
"AWS": "arn:aws:boom:boom"
}
}
The CompositePrincipal class can also be used to define complex principals, for example:
const role = new iam.Role(this, 'MyRole', {
assumedBy: new iam.CompositePrincipal(
new iam.ServicePrincipal('ec2.amazonaws.com'),
new iam.AccountPrincipal('1818188181818187272')
)
});
0.35.0 (2019-06-19)
cdk context (#2870) (b8a1c8e), closes #2854name in StageProps to stageName. (#2882) (be574a1)hwType to hardwareType (#2916) (1aa0589), closes #2896aws-sns-subscribers (#2804) (9ef899c)AssetProps.packaging has been removed and is now automatically discovered based on the file type.ZipDirectoryAsset has been removed, use aws-s3-assets.Asset.FileAsset has been removed, use aws-s3-assets.Asset.Code.directory and Code.file have been removed. Use Code.asset.hardwareType from hwType.TableOptions.pitrEnabled renamed to pointInTimeRecovery.TableOptions.sseEnabled renamed to serverSideEncryption.TableOptions.ttlAttributeName renamed to timeToLiveAttribute.TableOptions.streamSpecification renamed stream.ContainerImage.fromAsset() now takes only build directory
directly (no need to pass scope or id anymore).ISecret.secretJsonValue renamed to secretValueFromJson.ParameterStoreString has been removed. Use StringParameter.fromStringParameterAttributes.ParameterStoreSecureString has been removed. Use StringParameter.fromSecureStringParameterAttributes.ParameterOptions.name was renamed to parameterName.newStream renamed to addStream and doesn't need a scopenewSubscriptionFilter renamed to addSubscriptionFilter and doesn't need a scopenewMetricFilter renamed to addMetricFilter and doesn't need a scopeNewSubscriptionFilterProps renamed to SubscriptionPropsNewLogStreamProps renamed to LogStreamOptionsNewMetricFilterProps renamed to MetricFilterOptionsJSONPattern renamed to JsonPatternMethodOptions.authorizerId is now called authorizer and accepts an IAuthorizer which is a placeholder interface for the authorizer resource.restapi.executeApiArn renamed to arnForExecuteApi.restapi.latestDeployment and deploymentStage are now read-only.EventPattern.detail is now a map.scheduleExpression: string is now schedule: Schedule.cdk.RemovalPolicy
to configure the resource's removal policy.applyRemovalPolicy is now CfnResource.applyRemovalPolicy.RemovalPolicy.Orphan has been renamed to Retain.RemovalPolicy.Forbid has been removed, use Retain.RepositoryProps.retain is now removalPolicy, and defaults to Retain instead of remove since ECR is a stateful resourceKeyProps.retain is now removalPolicyLogGroupProps.retainLogGroup is now removalPolicyLogStreamProps.retainLogStream is now removalPolicyDatabaseClusterProps.deleteReplacePolicy is now removalPolicyDatabaseInstanceNewProps.deleteReplacePolicy is now removalPolicyattr instead of the resource type. For example, in S3 bucket.bucketArn is now bucket.attrArn.propertyOverrides has been removed from all "Cfn" resources, instead
users can now read/write resource properties directly on the resource class. For example, instead of lambda.propertyOverrides.runtime just use lambda.runtime.stageName instead of nameFunction.addLayer to addLayers and made it variadicIFunction.handler propertyIVersion.versionArn property (the value is at functionArn)SingletonLayerVersionLogRetentionPolicyStatement no longer has a fluid API, and accepts a
props object to be able to set the important fields.ImportedResourcePrincipal to UnknownPrincipal.managedPolicyArns renamed to managedPolicies, takes
return value from ManagedPolicy.fromAwsManagedPolicyName().PolicyDocument.postProcess() is now removed.PolicyDocument.addStatement() renamed to addStatements.PolicyStatement is no longer IResolvable, call .toStatementJson()
to retrieve the IAM policy statement JSON.AwsPrincipal has been removed, use ArnPrincipal instead.s3.StorageClass is now an enum-like class instead of a regular
enum. This means that you need to call .value in order to obtain it's value.s3.Coordinates renamed to s3.LocationArtifact.s3Coordinates renamed to Artifact.s3Location.BuildSpec object.lambda.Runtime.NodeJS* are now lambda.Runtime.Nodejs*Stack APIstack.name renamed to stack.stackNamestack.stackName will return the concrete stack name. Use Aws.stackName to indicate { Ref: "AWS::StackName" }.stack.account and stack.region will return the concrete account/region only if they are explicitly specified when the stack is defined (under the env prop). Otherwise, they will return a token that resolves to the AWS::AccountId and AWS::Region intrinsic references. Use Context.getDefaultAccount() and Context.getDefaultRegion() to obtain the defaults passed through the toolkit in case those are needed. Use Token.isUnresolved(v) to check if you have a concrete or intrinsic.stack.logicalId has been removed. Use stack.getLogicalId()stack.env has been removed, use stack.account, stack.region and stack.environment insteadstack.accountId renamed to stack.account (to allow treating account more abstractly)AvailabilityZoneProvider can now be accessed through Context.getAvailabilityZones()SSMParameterProvider can now be accessed through Context.getSsmParameter()parseArn is now Arn.parsearnFromComponents is now arn.formatnode.lock and node.unlock are now privatestack.requireRegion and requireAccountId have been removed. Use Token.unresolved(stack.region) insteadstack.parentApp have been removed. Use App.isApp(stack.node.root) instead.stack.missingContext is now privatestack.renameLogical have been renamed to stack.renameLogicalIdIAddressingScheme, HashedAddressingScheme and LogicalIDs are now internal. Override Stack.allocateLogicalId to customize how logical IDs are allocated to resources.--rename, and the stack
names are now immutable on the stack artifact.@aws-cdk/aws-sns-subscribers
package.roleName in RoleProps is now of type PhysicalNamebucketName in BucketProps is now of type PhysicalNameroleName in RoleProps is now of type PhysicalNameFAQs
CDK routines for easily assigning correct and minimal IAM permissions
The npm package @aws-cdk/aws-iam receives a total of 144,063 weekly downloads. As such, @aws-cdk/aws-iam popularity was classified as popular.
We found that @aws-cdk/aws-iam demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 4 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket is launching Ruby support for all users. Enhance your Rails projects with AI-powered security scans for vulnerabilities and supply chain threats. Now in Beta!

Product
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
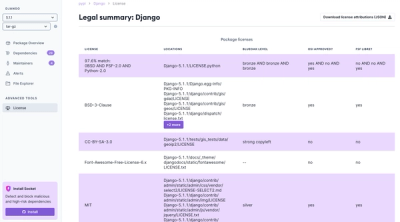
Product
We're launching a new set of license analysis and compliance features for analyzing, managing, and complying with licenses across a range of supported languages and ecosystems.