
Product
Introducing Ruby Support in Socket
Socket is launching Ruby support for all users. Enhance your Rails projects with AI-powered security scans for vulnerabilities and supply chain threats. Now in Beta!
@aws-cdk/aws-kms
Advanced tools
@aws-cdk/aws-kms is an AWS CDK library that allows you to define and manage AWS Key Management Service (KMS) resources in your AWS infrastructure as code. It provides constructs for creating and managing KMS keys, aliases, and grants, enabling secure encryption and decryption of data.
Create a KMS Key
This code sample demonstrates how to create a new KMS key with key rotation enabled and an alias using the AWS CDK.
const cdk = require('@aws-cdk/core');
const kms = require('@aws-cdk/aws-kms');
const app = new cdk.App();
const stack = new cdk.Stack(app, 'MyStack');
const key = new kms.Key(stack, 'MyKey', {
enableKeyRotation: true,
alias: 'alias/my-key'
});
app.synth();Create a KMS Alias
This code sample demonstrates how to create a new KMS alias that points to an existing KMS key using the AWS CDK.
const cdk = require('@aws-cdk/core');
const kms = require('@aws-cdk/aws-kms');
const app = new cdk.App();
const stack = new cdk.Stack(app, 'MyStack');
const key = new kms.Key(stack, 'MyKey');
const alias = new kms.Alias(stack, 'MyAlias', {
aliasName: 'alias/my-alias',
targetKey: key
});
app.synth();Grant Permissions to a KMS Key
This code sample demonstrates how to grant encrypt and decrypt permissions to an IAM user for a KMS key using the AWS CDK.
const cdk = require('@aws-cdk/core');
const kms = require('@aws-cdk/aws-kms');
const iam = require('@aws-cdk/aws-iam');
const app = new cdk.App();
const stack = new cdk.Stack(app, 'MyStack');
const key = new kms.Key(stack, 'MyKey');
const user = new iam.User(stack, 'MyUser');
key.grantEncryptDecrypt(user);
app.synth();The aws-sdk package is the official AWS SDK for JavaScript, which provides a comprehensive set of tools for interacting with AWS services, including KMS. Unlike @aws-cdk/aws-kms, which is used for defining infrastructure as code, aws-sdk is used for making API calls to AWS services directly from your application code.
The serverless package is a framework for building and deploying serverless applications on AWS and other cloud providers. It includes support for managing AWS KMS keys as part of your serverless infrastructure. While it provides similar functionality for managing KMS keys, it is more focused on serverless architectures compared to the broader infrastructure management capabilities of @aws-cdk/aws-kms.
Terraform is an open-source infrastructure as code tool that allows you to define and manage cloud resources, including AWS KMS keys, using a declarative configuration language. It provides similar functionality to @aws-cdk/aws-kms but uses a different syntax and approach to infrastructure management.
Define a KMS key:
import kms = require('@aws-cdk/aws-kms');
new kms.Key(this, 'MyKey', {
enableKeyRotation: true
});
Add a couple of aliases:
const key = new kms.Key(this, 'MyKey');
key.addAlias('alias/foo');
key.addAlias('alias/bar');
see Trust Account Identities for additional details
To use a KMS key in a different stack in the same CDK application, pass the construct to the other stack:
see Trust Account Identities for additional details
To use a KMS key that is not defined in this CDK app, but is created through other means, use
Key.fromKeyArn(parent, name, ref):
const myKeyImported = kms.Key.fromKeyArn(this, 'MyImportedKey', 'arn:aws:...');
// you can do stuff with this imported key.
myKeyImported.addAlias('alias/foo');
Note that a call to .addToPolicy(statement) on myKeyImported will not have
an affect on the key's policy because it is not owned by your stack. The call
will be a no-op.
KMS keys can be created to trust IAM policies. This is the default behavior in the console and is described here. This same behavior can be enabled by:
new Key(stack, 'MyKey', { trustAccountIdentities: true });
Using trustAccountIdentities solves many issues around cyclic dependencies
between stacks. The most common use case is creating an S3 Bucket with CMK
default encryption which is later accessed by IAM roles in other stacks.
stack-1 (bucket and key created)
// ... snip
const myKmsKey = new kms.Key(this, 'MyKey', { trustAccountIdentities: true });
const bucket = new Bucket(this, 'MyEncryptedBucket', {
bucketName: 'myEncryptedBucket',
encryption: BucketEncryption.KMS,
encryptionKey: myKmsKey
});
stack-2 (lambda that operates on bucket and key)
// ... snip
const fn = new lambda.Function(this, 'MyFunction', {
runtime: lambda.Runtime.NODEJS_10_X,
handler: 'index.handler',
code: lambda.Code.fromAsset(path.join(__dirname, 'lambda-handler')),
});
const bucket = s3.Bucket.fromBucketName(this, 'BucketId', 'myEncryptedBucket');
const key = kms.Key.fromKeyArn(this, 'KeyId', 'arn:aws:...'); // key ARN passed via stack props
bucket.grantReadWrite(fn);
key.grantEncryptDecrypt(fn);
The challenge in this scenario is the KMS key policy behavior. The simple way to understand
this, is IAM policies for account entities can only grant the permissions granted to the
account root principle in the key policy. When trustAccountIdentities is true,
the following policy statement is added:
{
"Sid": "Enable IAM User Permissions",
"Effect": "Allow",
"Principal": {"AWS": "arn:aws:iam::111122223333:root"},
"Action": "kms:*",
"Resource": "*"
}
As the name suggests this trusts IAM policies to control access to the key. If account root does not have permissions to the specific actions, then the key policy and the IAM policy for the entity (e.g. Lambda) both need to grant permission.
1.32.0 (2020-04-07)
UserPoolClient construct no longer has the property
userPoolClientClientSecret. The functionality to retrieve the client
secret never existed in CloudFormation, so this property was not
working in the first place.userPoolClientName property on the UserPoolClient
construct will throw an error if client name was not configured on the
UserPoolClient during initialization. This property was previously
incorrectly configured and was returning a not-implemented message from
CloudFormation every time.sourceCodeProvider prop to connect your app to a source
code provider. The props repository, accessToken and oauthToken do not exist
anymore in AppProps.retentionPeriodHours is now retentionPeriod and of type DurationCluster now creates a default managed nodegroup as its default capacity. Set the new cluster property defaultCapacityType to DefaultCapacityType.EC2 to preserve EC2 as its default capacity.add*Trigger() methods to configure
lambda triggers has now been replaced by a single
addTrigger() method.addTrigger() method will fail if a trigger
was already configured for that user pool operation.{[key: string]: any} instead of plain any. You were always supposed to pass a map/dictionary in these locations, but the type system didn't enforce it. It now does.aws:SecureTransport for staging bucket (#7192) (ed106ea)Size unit representing digital information quantity (#6940) (22a560d)acm-certificatemanager: DnsValidatedCertificateHandler support for SubjectAlternativeNames (#7050) (a711c01), closes #4659
aws-kinesis: test assume order between stacks (#7065) (17aab37)
cli: can't use credential providers for stacks with assets (#7022) (afd7045), closes #7005
cloudtrail: include s3KeyPrefix in bucket policy resource (#7053) (b49881f), closes #6741
cognito: user pool - passwordPolicy.minLength is not optional in all cases (#6971) (49cdd8f)
dynamodb: cannot use attribute as key in a GSI, non-key in another (#7075) (a6bd34f), closes #4398
ecs: default Service throws in a VPC without private subnets (#7188) (0ef6a95), closes #7062
events: Batch target does not work (#7191) (6f00783), closes #7137
kinesis: retention period does not use Duration type (#7037) (1186227), closes #7036
rewrite-imports: incorrect main in package.json (#7021) (2bf85b3)
stepfunctions-tasks: batch job - can not use task input as array size (#7008) (923d2a1), closes #6922
stepfunctions-tasks: confusion between multiple ways to run a Lambda (#6796) (7485448), closes #4801
FAQs
The CDK Construct Library for AWS::KMS
The npm package @aws-cdk/aws-kms receives a total of 116,565 weekly downloads. As such, @aws-cdk/aws-kms popularity was classified as popular.
We found that @aws-cdk/aws-kms demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 4 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Socket is launching Ruby support for all users. Enhance your Rails projects with AI-powered security scans for vulnerabilities and supply chain threats. Now in Beta!

Product
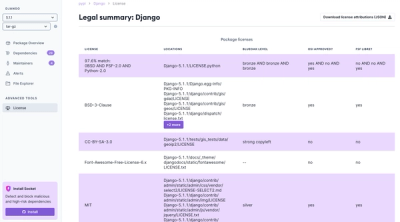
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
Product
We're launching a new set of license analysis and compliance features for analyzing, managing, and complying with licenses across a range of supported languages and ecosystems.