
Product
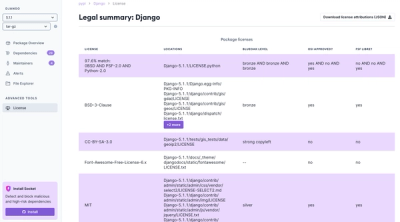
Introducing License Enforcement in Socket
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
@aws-sdk/client-secrets-manager
Advanced tools
AWS SDK for JavaScript Secrets Manager Client for Node.js, Browser and React Native
The @aws-sdk/client-secrets-manager package is a client library for interacting with AWS Secrets Manager service. It allows developers to manage secrets needed in their applications without hardcoding sensitive information. The package provides functionalities such as creating, reading, updating, and deleting secrets, as well as retrieving the current value of a secret.
Create a Secret
This code sample demonstrates how to create a new secret in AWS Secrets Manager.
const { SecretsManagerClient, CreateSecretCommand } = require('@aws-sdk/client-secrets-manager');
const client = new SecretsManagerClient({ region: 'your-region' });
const command = new CreateSecretCommand({
Name: 'MyTestSecret',
SecretString: 'MySecretValue'
});
const run = async () => {
try {
const data = await client.send(command);
console.log(data);
} catch (error) {
console.error(error);
}
};
run();Retrieve a Secret Value
This code sample shows how to retrieve the current value of a secret stored in AWS Secrets Manager.
const { SecretsManagerClient, GetSecretValueCommand } = require('@aws-sdk/client-secrets-manager');
const client = new SecretsManagerClient({ region: 'your-region' });
const command = new GetSecretValueCommand({
SecretId: 'MyTestSecret'
});
const run = async () => {
try {
const data = await client.send(command);
console.log(data.SecretString);
} catch (error) {
console.error(error);
}
};
run();Update a Secret
This code sample illustrates how to update the value of an existing secret in AWS Secrets Manager.
const { SecretsManagerClient, UpdateSecretCommand } = require('@aws-sdk/client-secrets-manager');
const client = new SecretsManagerClient({ region: 'your-region' });
const command = new UpdateSecretCommand({
SecretId: 'MyTestSecret',
SecretString: 'NewSecretValue'
});
const run = async () => {
try {
const data = await client.send(command);
console.log(data);
} catch (error) {
console.error(error);
}
};
run();node-vault is a client library for HashiCorp Vault, a tool for managing secrets. While @aws-sdk/client-secrets-manager is specifically designed for AWS Secrets Manager, node-vault is used for interacting with Vault by HashiCorp. Both provide similar functionalities in terms of secrets management but are intended for different secret storage services.
azure-keyvault-secrets is a client library for managing secrets in Azure Key Vault. Similar to @aws-sdk/client-secrets-manager, it allows for creating, retrieving, updating, and deleting secrets. The main difference lies in the cloud provider, with azure-keyvault-secrets being specific to Azure's ecosystem.
AWS SDK for JavaScript SecretsManager Client for Node.js, Browser and React Native.
AWS Secrets Manager API Reference
AWS Secrets Manager provides a service to enable you to store, manage, and retrieve, secrets.
This guide provides descriptions of the Secrets Manager API. For more information about using this service, see the AWS Secrets Manager User Guide.
API Version
This version of the Secrets Manager API Reference documents the Secrets Manager API version 2017-10-17.
As an alternative to using the API, you can use one of the AWS SDKs, which consist of libraries and sample code for various programming languages and platforms such as Java, Ruby, .NET, iOS, and Android. The SDKs provide a convenient way to create programmatic access to AWS Secrets Manager. For example, the SDKs provide cryptographically signing requests, managing errors, and retrying requests automatically. For more information about the AWS SDKs, including downloading and installing them, see Tools for Amazon Web Services.
We recommend you use the AWS SDKs to make programmatic API calls to Secrets Manager. However, you also can use the Secrets Manager HTTP Query API to make direct calls to the Secrets Manager web service. To learn more about the Secrets Manager HTTP Query API, see Making Query Requests in the AWS Secrets Manager User Guide.
Secrets Manager API supports GET and POST requests for all actions, and doesn't require you to use GET for some actions and POST for others. However, GET requests are subject to the limitation size of a URL. Therefore, for operations that require larger sizes, use a POST request.
Support and Feedback for AWS Secrets Manager
We welcome your feedback. Send your comments to awssecretsmanager-feedback@amazon.com, or post your feedback and questions in the AWS Secrets Manager Discussion Forum. For more information about the AWS Discussion Forums, see Forums Help.
How examples are presented
The JSON that AWS Secrets Manager expects as your request parameters and the service returns as a response to HTTP query requests contain single, long strings without line breaks or white space formatting. The JSON shown in the examples displays the code formatted with both line breaks and white space to improve readability. When example input parameters can also cause long strings extending beyond the screen, you can insert line breaks to enhance readability. You should always submit the input as a single JSON text string.
Logging API Requests
AWS Secrets Manager supports AWS CloudTrail, a service that records AWS API calls for your AWS account and delivers log files to an Amazon S3 bucket. By using information that's collected by AWS CloudTrail, you can determine the requests successfully made to Secrets Manager, who made the request, when it was made, and so on. For more about AWS Secrets Manager and support for AWS CloudTrail, see Logging AWS Secrets Manager Events with AWS CloudTrail in the AWS Secrets Manager User Guide. To learn more about CloudTrail, including enabling it and find your log files, see the AWS CloudTrail User Guide.
To install the this package, simply type add or install @aws-sdk/client-secrets-manager using your favorite package manager:
npm install @aws-sdk/client-secrets-manageryarn add @aws-sdk/client-secrets-managerpnpm add @aws-sdk/client-secrets-managerThe AWS SDK is modulized by clients and commands.
To send a request, you only need to import the SecretsManagerClient and
the commands you need, for example CancelRotateSecretCommand:
// ES5 example
const { SecretsManagerClient, CancelRotateSecretCommand } = require("@aws-sdk/client-secrets-manager");
// ES6+ example
import { SecretsManagerClient, CancelRotateSecretCommand } from "@aws-sdk/client-secrets-manager";
To send a request, you:
send operation on client with command object as input.destroy() to close open connections.// a client can be shared by difference commands.
const client = new SecretsManagerClient({ region: "REGION" });
const params = {
/** input parameters */
};
const command = new CancelRotateSecretCommand(params);
We recommend using await operator to wait for the promise returned by send operation as follows:
// async/await.
try {
const data = await client.send(command);
// process data.
} catch (error) {
// error handling.
} finally {
// finally.
}
Async-await is clean, concise, intuitive, easy to debug and has better error handling as compared to using Promise chains or callbacks.
You can also use Promise chaining to execute send operation.
client.send(command).then(
(data) => {
// process data.
},
(error) => {
// error handling.
}
);
Promises can also be called using .catch() and .finally() as follows:
client
.send(command)
.then((data) => {
// process data.
})
.catch((error) => {
// error handling.
})
.finally(() => {
// finally.
});
We do not recommend using callbacks because of callback hell, but they are supported by the send operation.
// callbacks.
client.send(command, (err, data) => {
// proccess err and data.
});
The client can also send requests using v2 compatible style. However, it results in a bigger bundle size and may be dropped in next major version. More details in the blog post on modular packages in AWS SDK for JavaScript
import * as AWS from "@aws-sdk/client-secrets-manager";
const client = new AWS.SecretsManager({ region: "REGION" });
// async/await.
try {
const data = client.cancelRotateSecret(params);
// process data.
} catch (error) {
// error handling.
}
// Promises.
client
.cancelRotateSecret(params)
.then((data) => {
// process data.
})
.catch((error) => {
// error handling.
});
// callbacks.
client.cancelRotateSecret(params, (err, data) => {
// proccess err and data.
});
When the service returns an exception, the error will include the exception information, as well as response metadata (e.g. request id).
try {
const data = await client.send(command);
// process data.
} catch (error) {
const { requestId, cfId, extendedRequestId } = error.$metadata;
console.log({ requestId, cfId, extendedRequestId });
/**
* The keys within exceptions are also parsed.
* You can access them by specifying exception names:
* if (error.name === 'SomeServiceException') {
* const value = error.specialKeyInException;
* }
*/
}
Please use these community resources for getting help. We use the GitHub issues for tracking bugs and feature requests, but have limited bandwidth to address them.
aws-sdk-js
on AWS Developer Blog.aws-sdk-js.To test your universal JavaScript code in Node.js, browser and react-native environments, visit our code samples repo.
This client code is generated automatically. Any modifications will be overwritten the next time the @aws-sdk/client-secrets-manager package is updated.
To contribute to client you can check our generate clients scripts.
This SDK is distributed under the Apache License, Version 2.0, see LICENSE for more information.
FAQs
AWS SDK for JavaScript Secrets Manager Client for Node.js, Browser and React Native
We found that @aws-sdk/client-secrets-manager demonstrated a healthy version release cadence and project activity because the last version was released less than a year ago. It has 5 open source maintainers collaborating on the project.
Did you know?

Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Product
Ensure open-source compliance with Socket’s License Enforcement Beta. Set up your License Policy and secure your software!
Product
We're launching a new set of license analysis and compliance features for analyzing, managing, and complying with licenses across a range of supported languages and ecosystems.
Product
We're excited to introduce Socket Optimize, a powerful CLI command to secure open source dependencies with tested, optimized package overrides.