
Security News
Crates.io Users Targeted by Phishing Emails
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
@ayana/logger-api
Advanced tools



Logger API for usage in libraries
This is a really small module defining the API of @ayana/logger for usage in libraries.
Some people who make a library might not want to force people to use @ayana/logger but still use it in their applications for logging. With @ayana/logger-api it is up to the user if he want's to use @ayana/logger or not. If the user doesn't install the @ayana/logger module themselves, libraries using @ayana/logger-api won't show any log output. However if the user does install it, the logging will work.
Technically the library user could just disable @ayana/logger but that is configuration effort and also leaves the module installed doing nothing and consuming disk space.
With NPM
npm i @ayana/logger-api
With Yarn
yarn add @ayana/logger-api
Look at the README of the main module for usage. Note that some features aren't available for libraries as it is an anti-pattern to access them.
Refer to the LICENSE file.
FAQs
Logger API for usage in libraries
We found that @ayana/logger-api demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 2 open source maintainers collaborating on the project.
Did you know?

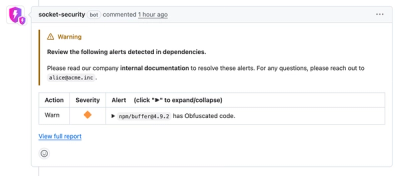
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.

Security News
The Rust Security Response WG is warning of phishing emails from rustfoundation.dev targeting crates.io users.
Product
Socket now lets you customize pull request alert headers, helping security teams share clear guidance right in PRs to speed reviews and reduce back-and-forth.

Product
Socket's Rust support is moving to Beta: all users can scan Cargo projects and generate SBOMs, including Cargo.toml-only crates, with Rust-aware supply chain checks.