Product
Introducing Webhook Events for Pull Request Scans
Add real-time Socket webhook events to your workflows to automatically receive pull request scan results and security alerts in real time.
@bosonprotocol/eventcapture
Advanced tools
Wrap event capture to fix missed events after a chain reorganization
This library wraps the blockchain event capture on-flight, so that it's possible:
Instead of subscribing directly to the events of a contracts using the on method, create a new EventWrapper instance.
npm install @bosonprotocol/eventcapture
contract.on(eventName, listener)
new EventWrapper(
contract,
eventName,
listener,
onCancelledTransactionHandler,
new EventStore())
npm run test
Be sure the .env file is defining the JSON_RPC_URL
JSON_RPC_PROVIDER=xxxxxxx
Then run the example
npm run example
npm run build
npm publish
FAQs
Wrap event capture to fix missed events after a chain reorganization
The npm package @bosonprotocol/eventcapture receives a total of 3 weekly downloads. As such, @bosonprotocol/eventcapture popularity was classified as not popular.
We found that @bosonprotocol/eventcapture demonstrated a not healthy version release cadence and project activity because the last version was released a year ago. It has 10 open source maintainers collaborating on the project.
Did you know?

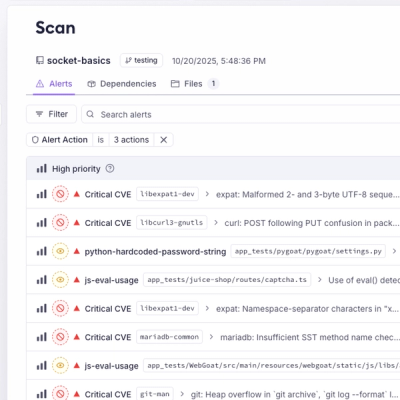
Socket for GitHub automatically highlights issues in each pull request and monitors the health of all your open source dependencies. Discover the contents of your packages and block harmful activity before you install or update your dependencies.
Product
Add real-time Socket webhook events to your workflows to automatically receive pull request scan results and security alerts in real time.

Research
The Socket Threat Research Team uncovered malicious NuGet packages typosquatting the popular Nethereum project to steal wallet keys.
Product
A single platform for static analysis, secrets detection, container scanning, and CVE checks—built on trusted open source tools, ready to run out of the box.